
In the past, if someone called themselves hacker chances are, they received some backlash or negative connotations. However, in recent times as the field of information is on the rise a new term ‘Ethical Hacking’ has emerged and opened many different avenues for IT and cyber security professionals.
The term ethical hacking was first coined by former IBM executive John Patrick in the 1990s, although the practical concepts were implemented much later on and are still in the development phases. More and more organisations are leaning towards the idea of using the help of ethical hackers to better protect their companies from cyber attacks.
In this article, we will look at the ins and outs of ethical hacking, what an ethical hacker actually does, their roles and responsibilities, job markets and how you can create your skill set in this domain.
What is ethical hacking?
Hacking in the IT world meant gaining unauthorised access to a computer system and making any software or hardware technology perform tasks that are not the intended purpose. With time, this concept changed offering clarity into its definition that anyone with curiosity and hunger for learning is a hacker, not the ones with criminal intent. They are more often known as cybercriminals, threat actors, malicious attackers, etc words go in here.
Ethical hacking is the same concept of gaining unauthorised access to systems but with the explicit permission of the system owner. An ethical hacker finds security vulnerabilities and flaws in a company’s IT infrastructure and reports them back to the stakeholders or relevant personnel for remediations.

An ethical hacker is given a scope of work and within that scope, they generally try to replicate what a real-world malicious hacker would do when attempting a cyber attack. This can consist of gaining access to systems, sensitive data exposure, exploiting insecure configurations, exploiting known hardware or software vulnerabilities, operating system or kernel exploits, and so on.
This proactive practise helps organisations to identify vulnerabilities in their environment and patch them before a malicious attacker finds the opportunity to exploit them.
What are the key concepts and responsibilities of an ethical hacker?
While ethical hacking may sound to be an amazing opportunity to break and hack a company’s IT assets, there are some boundaries that all ethical hackers should be aware of and must practice at all times.
First and foremost, before starting any activity that involves security testing of a target, prior approval should be taken from relevant owners. Preferably in a written form.
After taking permission, the scope of work should be identified and defined by the relevant owners. This scope of work would generally list down things like URLs, IP addresses, systems etc are allowed to be tested, An ethical hacker should under no circumstances deviate from the defined scope.
In some cases other than the allowed assets, the scope also includes which tests to conduct and which do not carry out. For example, many organisations will not allow ethical hackers to perform denial of service attacks.
Third, an ethical hacker should at all times report all vulnerabilities found during the security assessment. And if requested by the organisation, steps to reproduce the vulnerability along with evidence of exploitations should also be given.
And lastly, the ethical hacker should keep in mind to protect the data of the company and to not perform any actions that may lead to information leakage of any kind. They must not disclose any vulnerabilities found without the permission of the owners. In some cases, ethical hackers may also be required to sign Non-disclosure agreements (NDAs).
An ethical hacker must also ensure that the business continuity of the company is not disrupted at any time and there is no downtime as a result of their assessments.
Ethical hacking techniques
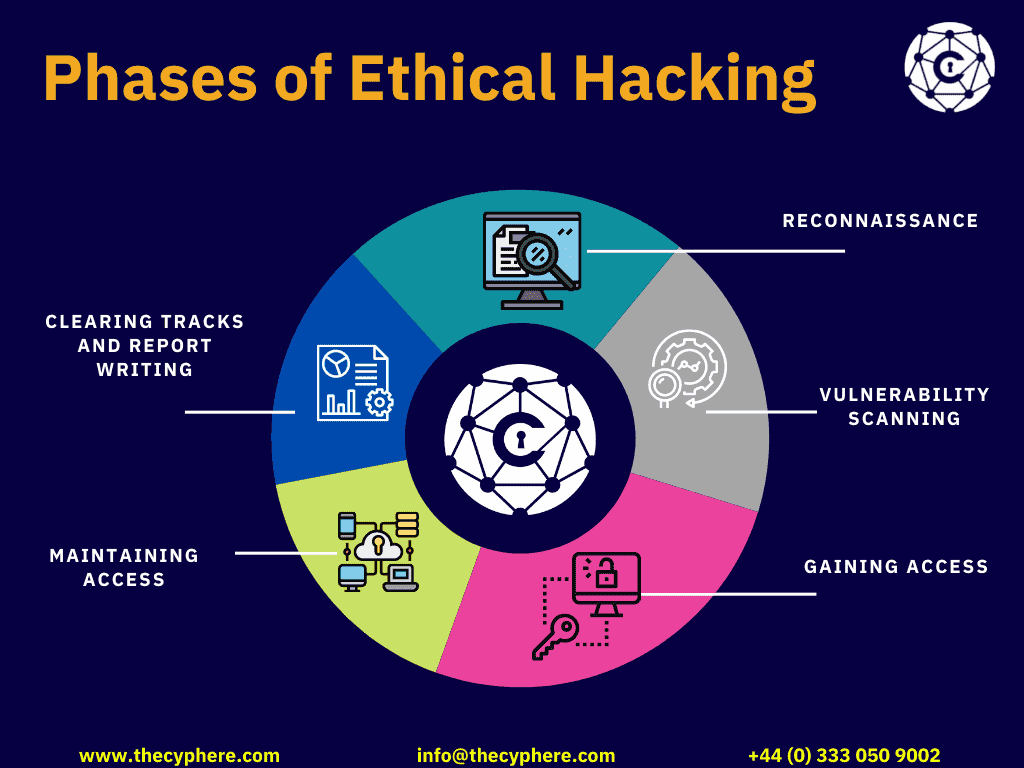
There are many techniques and methodologies that are followed when conducting a cyber security assessment, and many ethical hackers have developed their own methodologies from experience. Generally, when hacking any system, it comes down to following 5 phases of hacking and then expanding upon them.
The phases of hacking are:
Reconnaissance
In this phase, the ethical hacker tries to gather all the possible information about the target assets. This includes finding out what type of technologies are being used, what type of network architecture is implemented, is there any defence mechanism in place, email addresses, locations, office timings, IP addresses, DNS records, MX records, subdomains etc are all noted down in the information-gathering phase.
This step is the most crucial, the better the information is gathered the better are the chances of exploitation. Generally ethical hackers should spend most of their time in developing a reconnaise strategy.
Scanning

Once all information is gathered, it is important to narrow down the useful information and reduce the attack surface. The ethical hacker should then perform vulnerability scans on the information gathered and locate vulnerabilities. Scanning includes doing port scans for available services, website scanning, server scanning etc.
This phase yields any potential vulnerabilities that can be exploited.
Gaining Access
Now that the ethical hacker has a list of possible vulnerabilities, the actual exploitation or hacking happens in this phase. The ethical hacker launches a full fledged attack on the assets using the information gained in the previous two phases.
Maintaining Access
In the case of ethical hacking, this step is optional. If the ethical hacker has enough information to display the impact of the vulnerability then he does not need to create persistent access in the target company.
However if the ethical hacker needs to come back and continue his tasks on the compromised system whenever needed then he can deploy trojans to create backdoors and continue the security assessment. This technique can also be used when trying to launch further attacks from a compromised system inside the organisation.
Clearing tracks and report writing
Again in ethical hacking, this phase is optional and depends on the initial agreement between the ethical hacker and the organisation. Clearing tracks basically means that the hacker removes all traces of this attack from the organisation’s systems such as removing any logs, deleting any files he created, uninstalling any applications etc.
Finally, the ethical hacker needs to document all his findings during the assessment, all the vulnerabilities found along with steps to reproduce and in some cases, potential remediations are also listed down.
What problems does ethical hacking identify?
Ethical hacking involves performing a security assessment of an organisation’s IT assets, he aims to replicate the actions of an attacker or malicious hacker. To do so, the ethical hacker looks for all attack vectors that can be used against the target.
As described in the phases above, an ethical hacker gathers information and looks for vulnerabilities against the asset in a combination of automated and manual testing with the help of multiple hacking tools. After exploitation, the ethical hacker submits a report highlighting all the security vulnerabilities found.
Some common vulnerabilities that ethical hackers find are:
- Use of default credentials.
- Server misconfigurations.
- Broken access controls.
- Sensitive data exposure.
- Injection attacks.
- Use of known vulnerable components and lack of patch management.
- Missing encryption etc.
Apart from solving problems on a technical level, using a certified ethical hacker also saves small companies from investing in their own information security department and provides a cost-effective solution in which small companies do not need to hire cyber security professionals on their payroll but instead they can offer contracts to ethical hackers and achieve the same results.
Type of hackers
Hackers can be divided into three categories depending on the approach they use while performing hacking.
White hat hackers
White hat hackers are also known as ethical hackers, who test the targets after permission form the owners. A white-hat hacker responsibly reports all the vulnerabilities found to the asset owners.
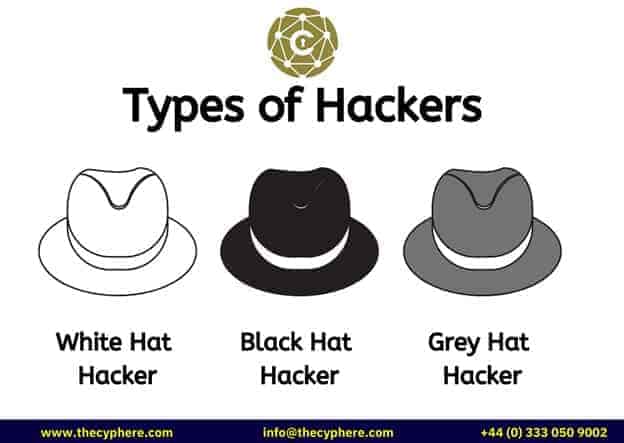
Black hat hackers
Black hat hackers are anyone who exploits a system, application or network without the permission of the owner and with a malicious intention. Black hats hackers often hack for personal gains or financial gains. They can steal or destroy the company’s valuable data and cause financial damage to the company. Black hat hacking is illegal and can result in criminal charges.
Grey hat hackers
Grey hat hackers are a combination of white and black hats. An example is that they hacked the company without permission but later reported the vulnerability. In such cases, it is up to the company if they want to file charges for breaking their system or thank the hacker for reporting the vulnerability.
Types of ethical hacking
There are many many types of technologies out in the world right now, from the basic web applications and web servers to Internet of things devices like smart TVs, Cars etc. Each one of these technologies can be hacked under ethical hacking.
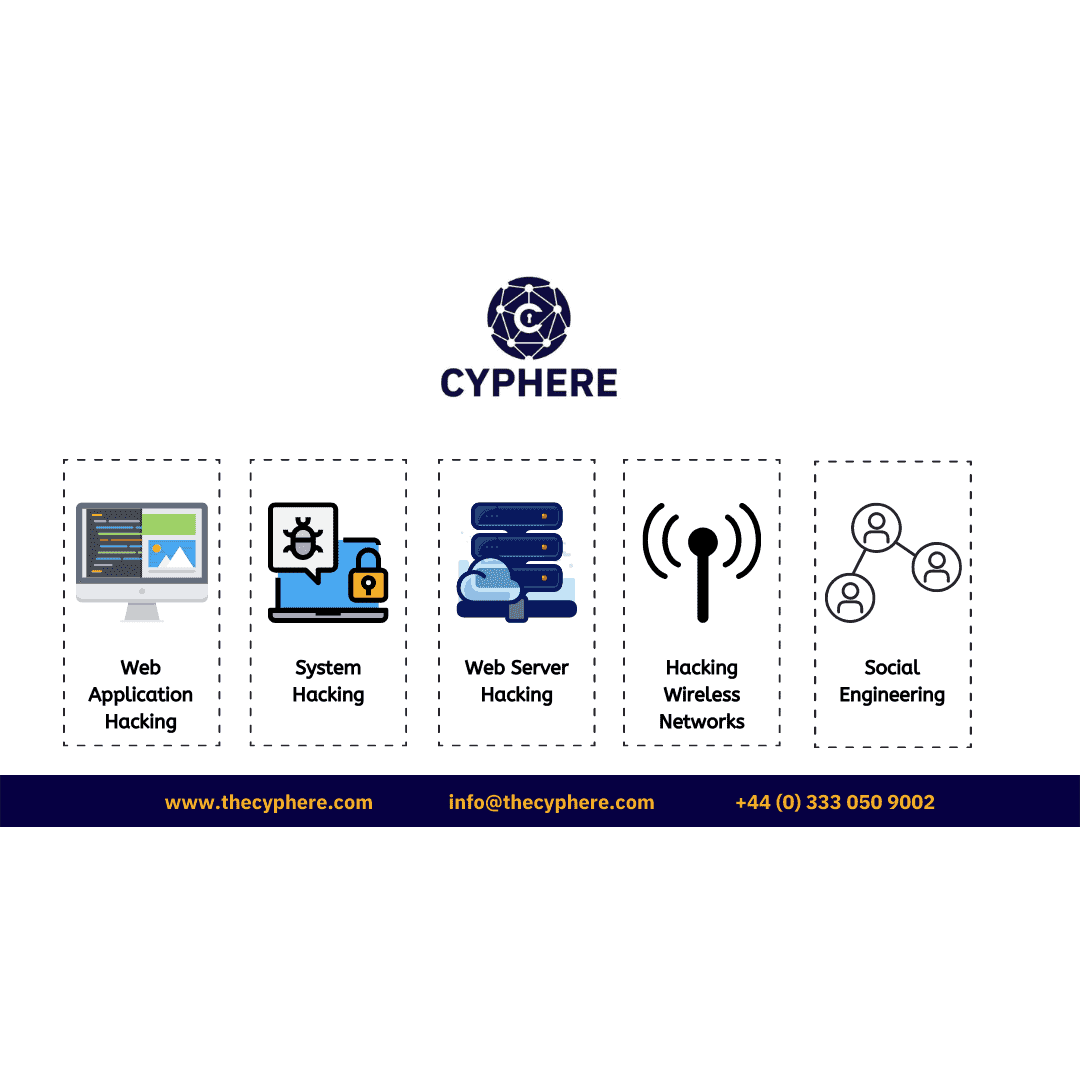
A few of the areas in which an ethical hacker can build their hacking skills are:
Application hacking
Application hacking mainly focuses on web applications, mobile applications and APIs. An ethical hacker tried to find vulnerabilities with these technologies. OWASP is a very good resource that launches the top 10 vulnerabilities that can be found in each domain.
Web Server hacking
Web servers host the application we see every day, these servers are a prime target for any malicious hacker and need to be tested to ensure there is no existing vulnerability.
Wireless network hacking
Wireless network hacking consists of testing wireless access points and networks for security weaknesses.
Network hacking
Ethical hackers can try to compromise the entire network of a company and gain unauthorised access to the company’s network.
System hacking
If the network configurations are secure then the systems on the network should also be secure. System hacking consists of an ethical hacker targeting all systems like desktops, servers, laptops, mobile devices etc inside an organisation to gain access.
Social engineering
Social engineering techniques are used to hack humans. What this means is that hackers exploit the trust of humans and trick them into believing and handing over sensitive information and credentials. Phishing is an example of social engineering.
IoT hacking
IoT hacking is the next big thing in IT, this includes hacking devices that are connected to the internet that are not primarily computer systems.
How does ethical hacking Work?
When an ethical hacker or white-hat hacker is contracted to carry out a security assessment he must carry out the following steps to ensure the best ethical hacking working procedure:
1. Define scope and outcomes
It is necessary for any ethical hacker to outline the scope of testing and the outcomes that the organisation is expecting from the activity. The kind of questions to asks in this phase include:
- What computer assets are in scope, their IP addresses / URLs should be listed.
- Does the testing include application, servers, databases, and operating systems in the scope?
- Is social engineering part of the testing?
- What will the timelines be?
- Does the testing need to be in a specific business or off-business hours?
- Will the testing be black box or white box?
- Will the testing be conducted with network security defences such as firewalls in place?
- What should the report include?
- What does the company wish to achieve from this activity?
2. Learning about the target
The main purpose of an ethical hacker is to:
- Identify security vulnerabilities in the target assets.
- Demonstrate how much potential damage a cybercriminal causes.
- Help organisations in remediating the reported vulnerabilities.
- Assess an organisation’s security posture.
And the first step to achieve this is to thoroughly learn all that is publicly available about the target assets. This includes information like IP addresses, Operating systems, Application stacks and technology, software versions, patch levels, open ports and services, users, email addresses and anything else that can help in exploitation.
3. Compromising the target
Using the information gathered in the discovery phase, the ethical hacker then exploits the vulnerabilities to gain access to the target system. In this phase, all possible entryways are tested and all findings from low hanging fruits to attacks like remote code execution are tested. If any defence mechanisms like anti-viruses or firewalls are implemented then the ethical hacker also tries to bypass those.
The end goal is to find all ways a malicious hacker can enter the IT assets of the organisation.
4. Documentation
Lastly, the ethical hacker records all his observations and findings in a formal report containing affected assets, type of vulnerability, steps to reproduce, remediation techniques etc.
How are ethical hackers different from malicious hackers?
Certified ethical hacker uses his knowledge about computer systems to protect an organisation’s assets and help the organisation in their risk management strategies. They provide essential services to companies who need to assess their network security postures and protect themselves from data breaches. Ethical hacking is legal and one of the highest paying and fastest-growing professions in information technology today.
Malicious hackers on the other hand intend to gain unauthorised access only for the sake of financial gain or personal gain and recognition. They only bring reputational, financial and business damage to the organisation.
Ethical hacking vs. Penetration testing
Ethical hacking and penetration testing are two terms that are used interchangeably and many companies use both of these when posting job roles.
Penetration testing can be called a branch of ethical hacking in which the pen tester works under a defined time duration and scope and tries to hack the defined assets. Penetration testing is a narrow term focusing on performing cyber security assessments. It is different from ethical hacking as ethical hacking is wider and more comprehensive terminology in which penetration testing is one branch.

Is ethical hacking legal?
Even though looking at the definition of ethical hacking one could see that gaining unauthorised access may be wrong, ethical hacking is a completely legal job.
There is some overlap in the methodology of black hat hackers and ethical hackers but there is a fundamental difference that all activities carried out during ethical hacking are approved and trusted by the organisation. Not to mention that criminal hackers work with the intent to harm the target organisation whereas the ethical hacker works closely with the team to protect the organisation.
Nevertheless, all information security professionals should bear in mind that there are situations in which ethical hacking or white-hat hacking can become illegal, so everyone should be vary while carrying out their activities. Some of these scenarios include:
- Exposure of confidential company information (such as trade secrets)
- Altering, destroying or misuse of company data.
- Plant backdoors into the company system for later access without explicit permission.
Who hires ethical hackers?
Certified ethical hackers are hired in almost all industry sectors today, especially in banking, financial and fintech corporations. Some of the places for a certified ethical hacker to work include:
- Financial institutions.
- Ecommerce marketplaces
- SaaS companies
- Data centres and cloud computing companies
- Local, state, federal government bodies
- Entertainment and media providers.
- Cyber security service providers.
- Consultancy firms.
- Software houses.
Ethical hacking jobs: How the role is evolving
There are several ethical hacker job roles that an individual can opt for. Some of the more popular ethical hacking jobs include:
- Penetration tester
- Forensics analyst
- Computer crime investigator
- Data security analyst
- Application security analyst
- SOC analyst
- Incident response handler
- Risk and Compliance manager
- Malware Analyst
- Cloud security analyst
- Security auditor
- Network security architect
Can you make a living out of ethical hacking?
Cyber security and ethical hacking jobs are on the rise and are often paid very well. Of course, the final amount does take into account the candidate’s skill set, whether or not he is a certified ethical hacker and has years of experience but overall this is a high pay job. To give an estimate, the average annual salaries range between £35000-£110000 in UK and around 70000 US$ – 150000 US$.
Skills Required to Become an Ethical Hacker
There is no formal education path or criteria to becoming an ethical hacker, so each organisation can set its own baseline requirements. These typically include a basic computer science degree with certifications relevant to information security or cyber security.
A candidate should have basic computer skills, basic knowledge of networking, operating systems, databases, programming languages, web application architecture, scripting and have a solid foundation in the principles of information security.
Ethical hacking courses
Nowadays there are many online platforms that offer both paid and free ethical hacking courses. Some of the more popular ethical hacking courses platforms include:
- Cybrary
- Udemy
- Cousera
- Pentester Academy
- PentesterLab
- StationX
- EH Academy
There are also many platforms available where beginners can practice their skills, after learning an ethical hacking course, on intentionally vulnerable security systems and compromise them using a different system, network and web hacking techniques. These platforms include:
- Hack the Box
- Vulnhub
- TryHackMe
- PentesterLab




Ethical Hacking Certification
Apart from gaining knowledge by watching online courses, it is equally important to gain relevant ethical hacking certifications from well-known certification bodies. Some popular certifications that would help in landing a job include:
- Certified Ethical Hacking (CEH) by Ec-council.
- Offensive Security Certified Professional (OSCP) by Offensive security.
- Certified Professional Penetration Tester (eCPPTv2) by eLearnSecurity.
- Junior Penetration Tester (eJPT) by eLearnSecurity
- Security+ and Pentest+ by CompTIA
- GIAC by SANS
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.
















