
Databases are essential for organisations because they store data critical for the organisation to function. This data can include customer information, financial records, and contact details. Organisations need to access this data quickly and securely to make decisions and run their business. A database can help them do this by providing a centralised location for all their data.
Database security is essential because organisations must protect their data from being accessed or stolen. We regularly assess weaknesses in databases during internal pen test assessments and ensure that there is extra stress on the security of the databases. After all, these are the crown jewels of an organisation.
What is database security?
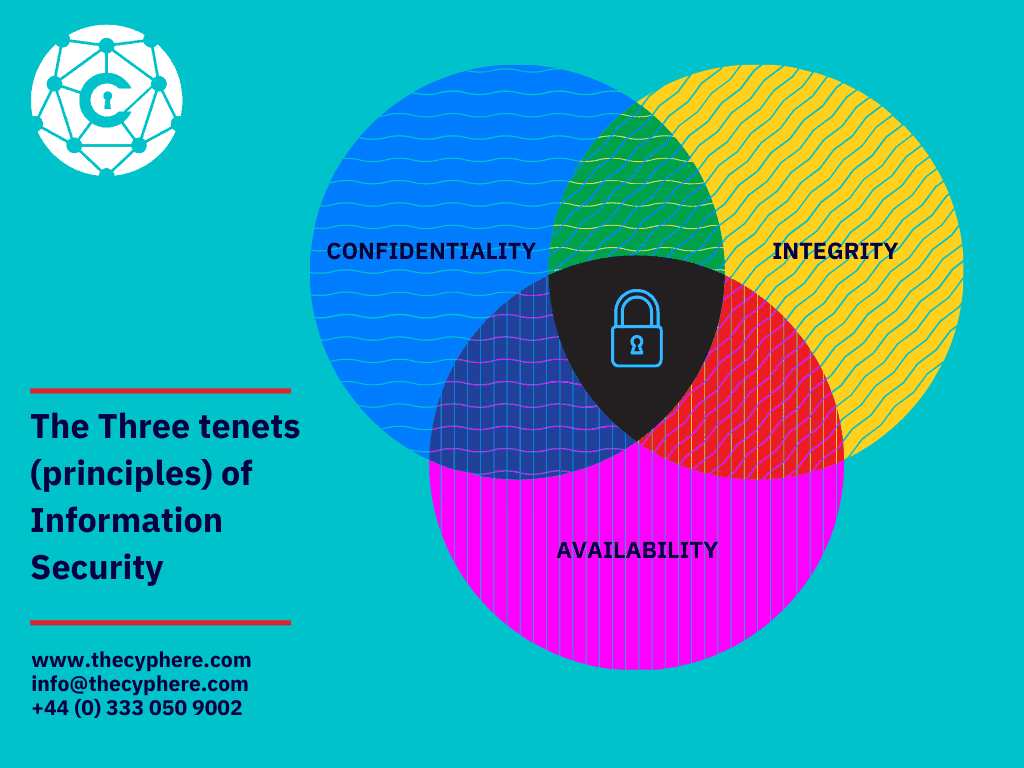
Secure database refers to the policies, controls, tools and mechanisms designed to ensure that the security CIA triad (i.e. Confidentiality, Integrity, Availability) of the database is maintained. Ensuring Database security plays a crucial role in protecting an organisation from cyber attacks that steal sensitive data and leak it on the Internet.
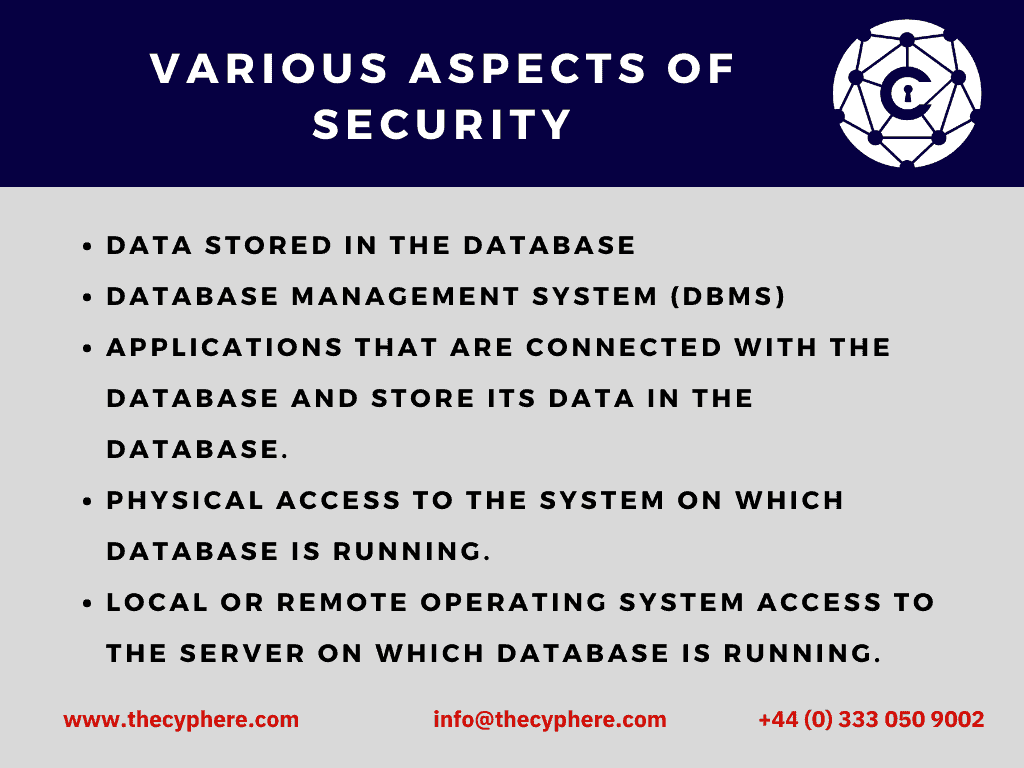
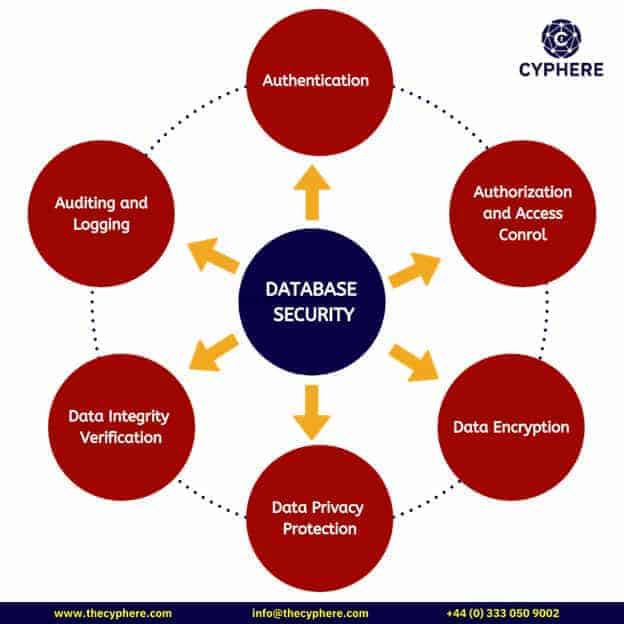
Database security measures aim to protect not only data residing within the database but also database management systems (DBMS) and all associated applications to prevent data leakage and misuse of data. These various aspects of database security are:
- Data stored in the database
- Database Management System (DBMS)
- Applications that are connected with the database and store their data in the database.
- Physical access to the system on which the database is running.
- Local or remote operating system access to the database server.
Why is database security important?
Database security was previously not taken as seriously as it is nowadays. This is because organisations lack awareness of how serious the database compromise could be.
Sensitive data stored in databases can be as sensitive as passwords, API keys, credit card numbers, personally identifiable information (PII), medical record numbers etc. Compromise of data may result in:
Compromise of data confidentiality
If sensitive data stored in databases is leaked and users’ passwords are made public, data confidentiality is compromised.
Example Scenario
If a database stores data from a web application where many users sign up and create their accounts, the passwords of users stored in the database must be hashed with a secure algorithm. So that even if the database is compromised, users’ passwords are not disclosed in plaintext.
Compromise of data privacy
Compromise of data privacy means that personal information is released to unauthorised individuals or groups. This can occur when organisations do not have strict security measures in place to protect people’s information.
Examples – Breach of data privacy
- An example of this is the Cambridge Analytica scandal, where 87 million Facebook users had their personal data harvested without their consent.
- If someone’s medical information is revealed from a hospital database that was compromised, then their privacy will have been violated.
Compromise of data integrity
Data integrity is compromised if the data stored in the database is modified to represent falsified information about the users.
Compromise of data integrity means that data is changed or deleted in an unauthorised way. This can happen when someone with malicious intent gains access to a computer system and alters or destroys the data stored there.
Examples of data integrity breach
- An example of this is the Stuxnet virus, which was used to attack Iranian nuclear facilities and cause physical damage to their centrifuges.
- Another example is the WannaCry ransomware attack, which encrypted data on infected computers and demanded a ransom be paid in order to regain access.
Compromise of data availability
Compromise of data availability means that authorised users are unable to access the data they need when they need it. This can happen due to a number of reasons, such as power outages, hardware failures, or malicious attacks.
Examples of data availability risks
- If the data stored in a database is associated with a web application that stores users’ credits which can be used to buy certain items on the website, deletion of that data can lead to financial damage to the users and the organisation.
- Examples of countless Denial of Service attacks that render websites ineffective and can’t serve their customers.
Due to the critical nature of data stored in databases, knowing how to secure databases is a demanding skill. The reason is that database security involves information security from various perspectives. Security analysts need to know how to implement network and service access controls, use strong passwords, enable database auditing etc.
Database Security threats
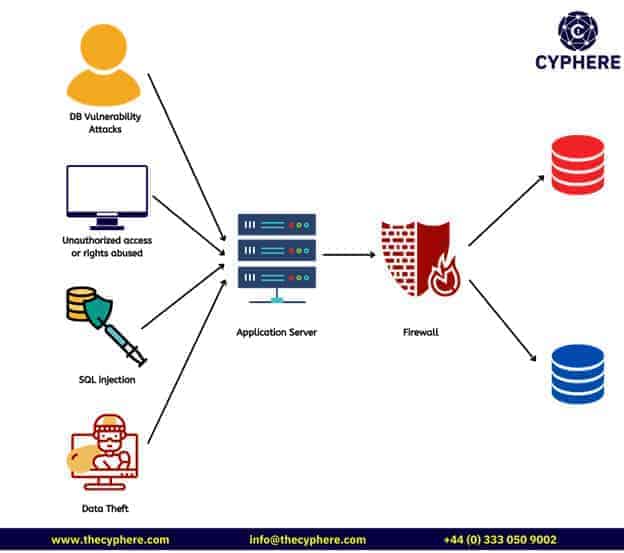
Nowadays, databases face many threats that may eventually lead to database compromise. These threats include exploitation of security vulnerabilities, firewall misconfiguration risks or human errors etc. Some well-known database security threats are discussed below:
Insider threats
An insider threat in the context of database security is one of the three possible actors from the following:
- A malicious employee of an organisation who intends to harm the organisation
- An ignorant employee who makes critical errors that make the database vulnerable to exploitation
- An intruder who by any method gains access to the internal infrastructure of the organisation and pivots it to gain access to the database.
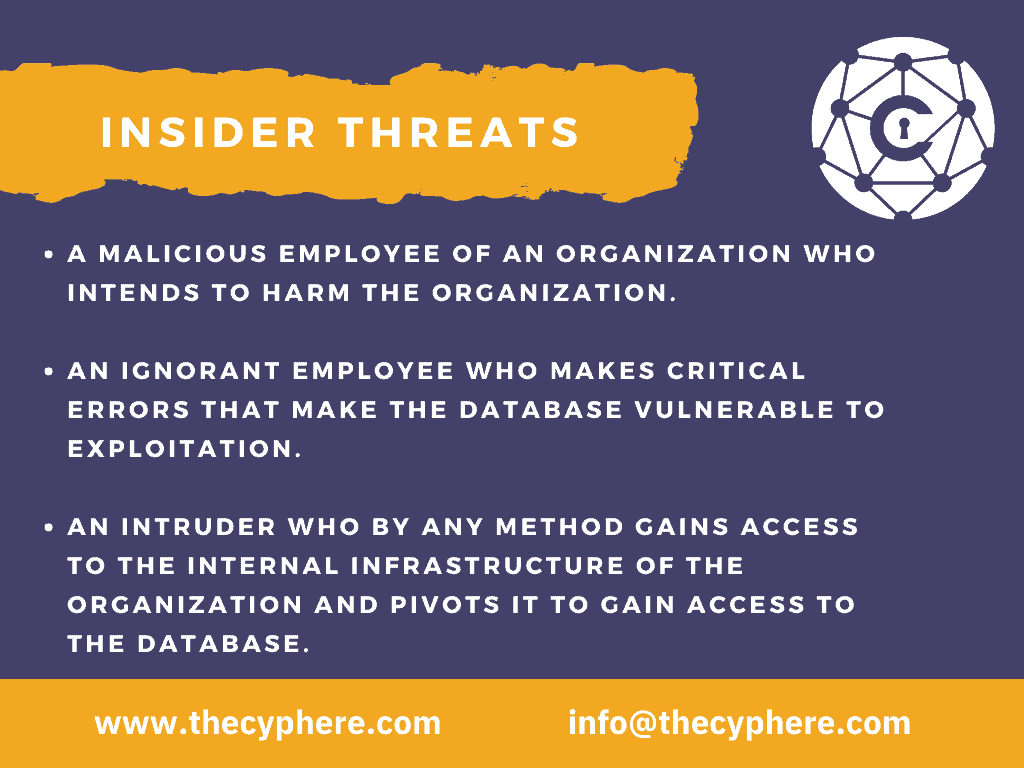
Insider threats are one of the most common ways by which databases are exploited and their occurrence results due to the non-compliance of the principle of least privilege.
Human error
Statistics show that nearly half of the reported data breaches resulted because of human errors. These errors include the usage of weak passwords, insecure password sharing, reuse of the same password across multiple platforms and uninformed usage of the Internet.
Exploitation of database software vulnerabilities
Malicious actors survive by finding and exploiting vulnerabilities in the huge amount of software out there. Database management systems are one of this software. The exploitation of a database vulnerability can lead to administrator access to the database and complete compromise of data.
Responsible security personnel should keep themselves updated by regularly monitoring threat feeds and security release notes of database software. So that they can update the databases by applying relevant patches.
SQL injection attacks
SQL injection is a web application specific attack vector which utilises web application input fields to manipulate queries and show unintended data to the attacker. SQL injection is one of the most severe web application attacks because it impacts all the data stored in a database.
Organisations can protect themselves from these web application attacks by following secure coding practices and regularly performing penetration testing of web applications to ensure that no areas of the applications are left unprotected.
Denial of service (DoS/DDoS) attacks
Denial of service attack refers to sending a huge amount of requests to the database server which renders the server unusable. This happens because the server is unable to handle all the requests at once. This results in the web application associated with that database being unresponsive and the organisation publishing the web server fails to provide uninterrupted availability of services.
Malware attacks
Malware is any malicious software that provides unauthorised access of a system to the adversary. Malware exploits vulnerabilities in the database to give the attacker root access to the system and hence the database. Organisations should take measures to prevent unauthorised dropping and execution of binaries within the infrastructure.
Database security best practices
In order for an organisation to ensure that their databases are not compromised, there are certain best practices they must follow. Since the databases are accessible via network and operating systems, their security considerations cover much more than just the database itself. Some of the best practices of database security are given below.
Ensuring physical security
Whether The database of an organisation may reside on-premises or in a cloud environment, Its physical access must be restricted and it should be in a climate-friendly location.
Database administration and network controls
Access to the database must remain within certain authorised users. The principle of least privilege says that only those who are responsible for administration and database activity monitoring should be given access to a certain resource.
Applying the same principle in databases can help reduce the possibility of database compromise by insider threat or human error. Similarly the access of databases over the network should also be restricted to internal zones.
Monitoring and securing end-user account/device
It is also important to monitor who is accessing the servers on which the database is running. Unnoticed and unauthorised access to the system can lead to severe data breach and reputational loss. Audit logs of servers should be created with enough details and logged to a central security solution such as a Security Information and Event Management (SIEM) solution.
Encryption of data:
The data residing in the database, if sensitive, must be encrypted with strong cryptographic controls to ensure that in case of a data breach, the data is not revealed in plaintext. The encryption keys that are used to encrypt the data must be stored and processed as per the best practices.
Ensuring database software security:
Not updating applications frequently can allow attackers to exploit the vulnerabilities in un-patched versions of databases. Security release notes of software should be monitored regularly in order to ensure timely updates of the application. If there is built-in security control within the software, it should be enabled and if it is not, legitimate reasons must be found for disabling that security control.
Ensuring application/web server security:
If an application is associated with the database, that application must be protected by following secure coding practices. The application can be leveraged as a side-channel attack and so it must be protected by performing penetration testing and following security best practices.
Regular backup of database:
Database backups must be taken regularly and the record of backing up must be documented. All the backup files are also subjected to the same best practices and security controls such as the database itself
Enabling system auditing:
Audit logs of the operating system and database must be maintained and monitored regularly to find any discrepancies. The audit logs should record all system and database logins as well as creation, modification and deletion of data within the database.
Using different alerting software, alerts can also be created to notify relevant personnel about potentially malicious activities. Effective monitoring of databases may allow the security analysts to timely identify a potential breach and take necessary measures to remediate it immediately.
Keeping web servers and database servers separate
By keeping web servers and database servers separate, the attack surface for the attacker is reduced. The goal is to keep the database server in a secure zone without any public interaction. And since web applications are hosted in a demilitarised zone (DMZ), they are publicly accessible. And if a web server was compromised and the database was running on the same server, the attacker might get access of the database too.
Use web applications and database firewalls
In order to cover any potential vulnerabilities in database or web applications, database and web application firewalls should be in place. The web servers should only accept traffic that is routed via web application firewall and block all traffic that is routed towards the origin IP address directly. While the database firewall should only allow traffic from the web server on the allowed port and block all other IP addresses.
Testing database security controls
Database security controls are essential for protecting your data, but it’s important to also test these controls to ensure they’re working correctly. Security testing can help identify any vulnerabilities that may still exist in your system after implementing these controls. By identifying and fixing these vulnerabilities, you can help protect your data from unauthorised access or theft, and shape up your future security strategy after analysing weaknesses. This could be the requirement for people, processes or tech controls.
Regular security audits help you to see the gaps that internal teams may miss on regular basis. Get in touch for a free conversation to know further on this topic.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.












