Remember when you installed Whatsapp? You most likely got a prompt asking you to click “Allow” so the app could access your media, run in the background, or manage contacts. In that instance, you were extending privileged access to the application, so it runs effectively for you.
In a world where data breaches and privacy infringements have serious consequences on the business, the principle of least privilege is one of the topmost security best practices that systems and companies need to follow. The principle of least privilege (PoLP) is the foundation of a business’s cyber security structure.
This is one of the most common issues found during internal network pen tests, mainly because it allows pen testers an easy route to privilege escalate to the highest levels in the shortest possible timeframes.
This blog will explain the Principle of least privilege, the difference between privileged and non-privileged accounts and famous breaches due to negligence in this area. We will also explore the benefits of least privileged access and discuss least privileged access control best practices.
What is the principle of least privilege?
The principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. It is the basis of the zero-trust model however zero-trust model is much more comprehensive.

Security professionals usually regard this principle as concerning user access rights, admin privileges and computer security frameworks. However, the Principle of least privilege has a broader application range, including access controls & security throughout an organisation. PoLP even applies to scenarios outside the work environment.
Security can be a complex discipline, however, its job remains the coverage of three principles of information security, also known as CIA triad:
- Confidentiality
- Integrity
- Availability

what does “the principle of least privilege” mean as applied to security?
In security, the principle of least privilege functions by allowing systems just enough access permissions to perform their required tasks. It thrives on the concept of a “need-to-know” basis. Networks, users, software & compute systems should only have access to data they need to know. The information they access must be relevant to their functions.
How the principle of least privilege (PoLP) works?
Just as privilege implies the special authorisation given to users or technologies to bypass certain security restraints, least means the opposite. The principle of least privilege is the practice of restricting the access rights of systems, users, accounts, and computing processes to the required resources only that are sufficient to perform specific activities.
Adhering to the principle of least privilege eliminates an intruder’s risk of gaining access to critical secrets or networks hosting sensitive data. It basically increases the difficulty of lateral movement and attacks within a network.
Implement least privilege access control to limit attackers’ access from infiltrating further into the enterprise networks or internal networks, stopping them from spreading to the wider areas within an organisation. Put simply, the least privilege principle is a big step toward cyber hygiene by controlling permissions.
Principle of Least privilege example
There are numerous examples of the least privilege principle at play in real-life:
- A cashier at a till has limited access to tend cash and deal with routine tasks at the front desk of a shop. However, only her manager has higher privileges to make changes to settings or reset the software in case there is a technical issue with the till or computer system in use.
- In banking, there are different teams who have access to load payments, release payments, audit and approve/reject bigger transactions. This is an example of multi-tier privilege model.
Coming back to the security topic, Microsoft have an excellent guide on implementing Least-Privilege Administrative Models. Least privilege policy template and process must be defined for the IT and security teams to ensure there is less administrative overhead, reduced change management backlog and smaller attack surface – all benefiting the organisation to maintain strong defences.
Although the PoLP is straightforward, privilege enforcement can be a bit challenging to implement effectively, especially when you consider variables such as:
- Varying operating systems (Windows, macOS, Linux, Unix)
- Increasing numbers and varieties of apps, networks and endpoints, ranging from desktops, laptops, tablets, smartphones, network and security devices and IoT.
- Various computing environments (cloud, virtual, hybrid)
- Different types of user account variables such as identities, roles (human, applications systems, machine)
A 2016 Forrester study also found that 80% of information security threats involve accounts with higher privileges. Another reason why the principle of least privilege, also the Principle of least authority, is essential security control.
Ensuring the least privilege is instrumental in mitigating information security risks, protecting sensitive data and minimising business disruptions that may result from system errors or malicious threats such as ransomware attacks, Denial of Service (DoS) attacks.
The cloud
Cloud and virtualized environments provide numerous benefits, the simple truth is why we see an exponential rise in cloud adoption. During our assessments, mainly AWS penetration testing, Azure pentest or Office 365 tenancy reviews, privilege audit is one of the main components.
Insecure privileged access management is likely the case during a hybrid environment where legacy applications, computer systems and services are used.
Latest systems such as AWS, Office 365, and Azure portals provide granular access with multiple privileges and roles to allow control and scalability. However, with multiple sites, and multi-cloud implementations, it can be quite a task for the teams leaving them with more chances of confusion and gaps without a lack of strict processes including tools.
Difference Between Privileged and Non-privileged Accounts
Privileged accounts enjoy elevated, non-restricted access to target systems, services or accounts that non-privileged accounts don’t have access to. Organisations often allot privileges to users based on two parameters:
- Business unit or job function (e.g. Customer service department, HR unit, IT officials
- Rank or level (Executive Directors get privilege over primary staff).
Aside from these two, factors such as; time of day, special circumstances, unique assignments, various operating systems, etc also come into play from time to time.
There are 3 common types of accounts;
- Superuser accounts (Most privileged such as domain administrator account, enterprise administrator account)
- Standard accounts (such as domain users)
- Guest accounts or non-user accounts (none, anonymous or little privileges)
Superuser accounts
These accounts are for administration and monitoring security and top-ranking IT employees. Also termed the “root account”, this account often has virtually unlimited privileges over a system network. Such rights may include read-write execute rights and the power to perform system-wide changes across a network. These include reconfiguring core system settings, adding and deleting users and data, and installing & uninstalling files and software, among others.
A superuser account in a Linux or Unix system has an all-encompassing presence on the network. It has unrestricted user access to all processes, commands, sensitive information and system resources. These admin accounts can even impact others by changing access controls.
Due to their privileged credentials and the extent of the damage they can cause, root accounts should only be accessed by IT admins when extremely necessary. A single error or malicious attack can paralyse the entire system or entirely disrupt an enterprise.
Hence, admins should also have standard accounts for routine tasks to ensure system security.
Standard user accounts
Standard accounts are also known as the least privilege to accounts or limited user accounts (LUA). These possess a limited set of privileges. They can run programs on networks and computers, modify simple processes and run minor and specific system functions. These are often allocated to staff in an organisation for routine tasks in different departments such as HR, IT, Finance, and Admin.
In an enterprise that observes the least privilege model, the majority of the users should be operating standard accounts 100% of the time. For example, a user on a standard level (e.g. Sales rep) shouldn’t have access to a company server like the core IT repo with software installs, licensing and setup information. This would otherwise be a direct risk to a server, bypassing basic server security best practices.
Guest or Non-user accounts
These accounts have zero to minimal privileges. They only have access to bare minimal functions, for instance, running simple programs. Some organisations define guest users with more than normal access such as internet browsing, access to certain file shares, etc. Such guest accounts (for one-time contractors) are most suited for internal processes or services, or sometimes part of the default account privileges.
There is a different definition of guest accounts when it comes to services or applications. Some applications name a user session as a guest account based on cookies assigned under unauthenticated sessions.
Guest account in Windows
The guest account lets other users use your computer without being able to change any settings, access private files or install any applications. Windows 10 no longer offers a guest account to share your PC but you can create a restricted account (the equivalent of a guest account).
Famous Breaches Due to Privileged Access Abuse
Malware & ransomware, insider threats, third-party vendors & partners, and privileged user errors account for the most common privilege abuse faced by enterprises.
This short review of some cyber attack situations that companies have faced in the past is included here. It will help you understand how to avoid similar occurrences in your organisation.
These are some of the famous examples of how threat actors took advantage of higher privileges in the real world;
Target Breach
In 2013, an international retail enterprise – Target – was targeted by attackers. They rendered infiltrated the company’s internal systems without raising any alarms to defensive teams. In a cyberattack that affected 70 million customers, the infiltrators stole credentials from a third-party vendor – an HVAC company. This contractor had access to far more privileges than needed to execute its maintenance tasks on the Target network. This is why the importance of cyber security best practices for eCommerce organisations is greater than before.
Target could have avoided this breach if it had reviewed access provisions for its suppliers and staff regularly. By limiting access permissions required to the least resources and areas needed by the heating and ventilation company, the outcome may have been different. Restricting access of vendors/third-party staff has been a challenging security control for many organisations. However, to avoid scenarios similar to Target’s, companies must give such rules utmost importance. Enterprises should provide access on a need basis only.
SolarWinds
In 2020, nation state backed attackers compromised SolarWinds, a major United States IT firm. This infiltration went undetected for almost a year, giving attackers access to SolarWinds’ (rights reserved) sensitive data and its clients. Most of these clients were US department agencies and corporates. The attackers worked by inserting malicious code into the SolarWinds Orion code. When SolarWinds unknowingly sent out regular software updates containing the malicious code, it created a backdoor via service accounts that enjoyed high privileges in the network that the attackers used to spy on customers.
This attack was possible because of the unrestricted access to critical systems that SolarWinds Orion requires to operate efficiently. The software requires global shared administrator access to work, a common requirement with legacy application systems like Orion.
The principle of least privilege is difficult – impossible really – to implement with systems like this where either by functionality or by misconfiguration privileged access is trusted on to the software in use. The systems require higher privileges that are needed to perform specific functions, which creates ample room for trust internally because none of the logging and alerting mechanisms will flag such an event.
While such incidents may be quite hard to avoid in this context, enterprises can mitigate such occurrences to a degree by choosing to screen vendors or applications that require access and ensuring stricter information security measures. As much as possible, organisations should enforce the least privilege application and access management by removing excessive application privileges. This is applicable to critical assets such as databases also (MySQL, MSQL, etc).

Principle of Least privilege benefits
The benefits of the principle of least privilege (PoLP) model are numerous, far more than wasting time thinking around downsides. Cyber threats are real, and when they become successful attacks – their effects are crippling. Access management is of the highest importance today. Here are some benefits enterprises gain when they follow the principle of least privilege;
1. Limited access = Limited attack surface = Increased difficulty
By restricting user privileges to a role-based process, organisations automatically reduce the chances of unauthorised access and infiltration. It is an effective way for companies to reduce their systems from being exploited. Even in the event of an attack, the attack surface range is minimal abuse of system or systems takes place, leaving attackers with hardly any choice.
For a detailed proactive approach to your cyber security strategy, follow 10 steps cyber security model as recommended by NCSC.
2. Improved security
Enterprises can better protect themselves, their users, and clients from privacy infringements and data leaks by implementing the principle of least privilege. PoLP ensures stricter security controls raising entire organisations’ internal profile. High-clearance staff should be the only ones with admin rights to sensitive areas of the system, and they should use this access with caution. On a broader level, this principle can be extended to physical access controls and other areas of access control within an organisation (at user, object, service, system, network and environment levels).
3. Reduces malware infection
The principle of least privilege significantly reduces malware spread and infection as it starves the malware of access points to infiltrate. This way, malware (such as ransomware, and spyware) is unable to expand their attacks around the internal systems.
4. Helps enterprises with security compliance
When regulatory agencies perform security audits, organisations that synchronise the principle of least privilege in their systems have a better chance of being cleared and adhering to security compliance requirements such as PCI DSS, ISO 27001, and GDPR a few. Not only it is a security best practice, but increasingly, many compliance regulations across various fields also require privilege audit as part of the penetration testing for systems security.
For instance, in the Payments industry, the PCI DSS Compliance requirements state that “To ensure critical data can only be accessed by authorised personnel, systems and processes must be in place to limit access on a need-to-know basis and according to job responsibilities.”
Disadvantages of the least privilege model
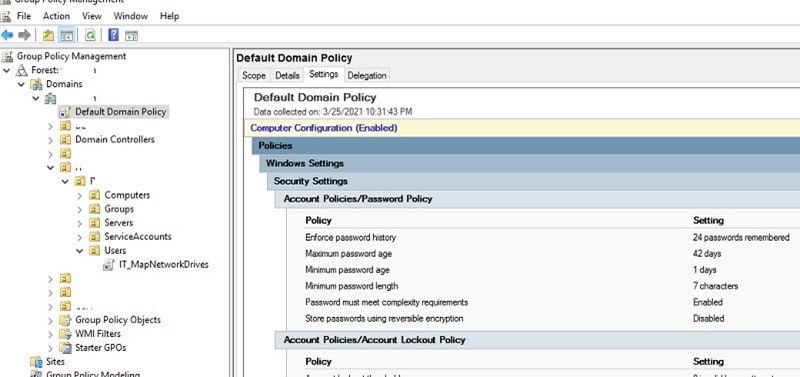
Keep in mind that the PoLP is just one dot connecting to others in a defensive controls strategy. Let’s take this example where a financial controller in an organisation requires a privileged account to make changes in the finance portal used by the internal departments. Active Directory integrated portal allocates privileges to the controller without reviewing the privileges that allow him higher access around the windows network too. In the case of a spear-phishing attack targeted at this controller, threat actors could gain administrator-level access due to the underlying account used by the controller. On the contrary, an attacker would have normal user-level access if the financial controller was supplied with a different account to be used for privileged tasks or via a jump box for privileged tasks only.
Organisations should consider other protective technologies to support the principle of least privilege, such as firewalls that prevent connections, antivirus, host-based intrusion detection systems and software restriction processes that limit what applications can install and execute. This practice should be deployed at the environment, networks, systems, and services down to the user/role level.

Least privilege best practices to follow
Here is a list of five practices for enterprises to adopt while implementing the least privilege principle;
- Use administrator accounts only when absolutely necessary. The security risk is much higher when operating these accounts, so use should be limited to sensitive tasks and where possible internally.
- Carry out a privilege audit across the estate or Active directory whichever is suitable. Ensure you account for, manage and regularly review employee, vendor and freelancer credentials.
- Eliminate default admin and anonymous rights. Users should be entitled to the least necessary privileges by default. Users should request elevated privileges relevant to their particular tasks if specific job roles require higher access. Account privileges should be limited to essential functions only.
- Create a system and network segments based on the asset category or classes. These should separate users from processes and rank them based on access requirements and privilege groups, thereby minimising malware’s attack surface.
- Adopt a just-in-time (JIT) strategy – Privileges should preferably be limited and time-bound. Implement one-time use privileges to ensure most users do not have unbridled access to the system’s sensitive areas. Access should last only as long as needed to complete specific tasks.
That’s not the end of this. It is important that regular reviews are performed to ensure the access management strategy is in line with functional requirements.
- Ensure that privileged account usage audit events are carefully selected not to overwhelm the monitoring teams and mechanisms. It includes logging of success or failure or both the events in cases of logons, objects access, directory services, passwords change, unusual service access, etc.
- Perform privilege account audits and ensure processes are in place to remove them after use.
- Follow strict change management procedures to ensure no exceptions are allowed and all requests comply with relevant processes and approvals.
To get you ready for the pub quiz…
Which security principle prevents any one administrator from having sufficient access to compromise?
The principle of least privilege (PoLP)
Refer to the related topic of privileged access management to know more about concept, advantages and solution selection.
Get in touch to discuss your security concerns, strategy, or any other challenges around the subject.
Harman Singh is a security professional with over 15 years of consulting experience in both public and private sectors.
As the Managing Consultant at Cyphere, he provides cyber security services to retailers, fintech companies, SaaS providers, housing and social care, construction and more. Harman specialises in technical risk assessments, penetration testing and security strategy.
He regularly speaks at industry events, has been a trainer at prestigious conferences such as Black Hat and shares his expertise on topics such as ‘less is more’ when it comes to cybersecurity. He is a strong advocate for ensuring cyber security as an enabler for business growth.
In addition to his consultancy work, Harman is an active blogger and author who has written articles for Infosecurity Magazine, VentureBeat and other websites.