With all the remote works, online businesses, and digital lifestyle, applications (software) have become an integral part of our lives. In contrast, the growing rate of data breaches and cyber-attacks exploiting minor glitches in application functionality has diverted attention to application security which is still underrated in the era of phenomenal technological advancement.
Many organisations believe in rich-functioned applications and do not care about the security and privacy requirement. But this cannot deny the fact and necessity of security activities in the application, whether these are findings of an application penetration test, secure code review or any other security validation exercise.
The alarming rate of cyber incidents has raised compliance and regulation demands, which have mandated the companies to ensure user data confidentiality and privacy as a primary factor in any business.
To avoid the vulnerabilities in application design and architecture, the development team must follow security guidelines with a clear understanding to design, develop and deploy the software, and this is where secure SDLC plays its parts.
This article covers everything you need to know about secure software development lifecycle, i.e., what SDLC is, what processes it offers and why it is so important to have.
What is a Secure Software Development Life Cycle (SDLC)?
The Secure Software Development Life Cycle is a framework and systematic approach to combining security into the software development lifecycle. It involves embedding security to the foundation of application or software from scratch to each stage of development till the post-development phase. It is developed to undertake security and privacy concerns from the beginning of the application to throughout the development phases and process.
As a result, it significantly reduces the development cost, provides guidance to developers to create profoundly secure software, benefits in adhering to the compliance requirements, and identifies risk in each development stage.
Besides this, it helps developers and security teams detect and remediate the flaws at their earliest rather than exploring them after the release or later stages of development. Of course, secure SDLC can be added during the production or after the release, but that increases the cost to a great extent, especially after the release. However, adding security to your software development lifecycle is never too late.
In secure SDLC, the development team and security team work side by side with one common goal of robust, secured progress and software delivery. It does not entirely eliminate the security threats but significantly reduces them and makes it easy to remediate the vulnerabilities or whatsoever that emerge in the future.
While the traditional security development processes focus on building rich-featured applications, the secure SDLC focuses on developing quality-featured applications protected against invaders and cyber attacks. Secure SDLC requires the careful adaptation of security best practices and processes to help applications stand on the foothold and be resilient to threats.
Why Is Secure SDLC Important?
Secure software development life cycle is not a new concept, but it has become an essential element in the modern application development cycle. Now, we have no time to think of security as a luxury.
The days are gone when you release products in the wild and add bug patches because this costs time and finances.
Secure SDLC is essential to ensure that the application is not subjected to common cyber attack vectors and has been built while considering potential vulnerabilities.
Understand it this way, suppose you have developed a web application without any rate-limiting control and released it. An attacker who got to know your application/software does not have any rate-limiting factor on the admin login page can launch a potential brute force attack and eventually compromise it after some unsuccessful struggles.
Since there was no account lockout policy, the attacker successfully made multiple attempts. Immediately, the attacker has access to your admin panel and has a vast opportunity to roam around and perform malicious activities.
To fix this flaw, you must make changes to your software architecture and design and implement a new code. All these new additions will take time to check the performance. You have to re-test all the application processes, which will cost double in terms of developer and quality assurance utilities.
In contrast, if this security issue were considered while documenting the software requirements, it would be easy to address business risks and common security flaws in the development cycle.
What are the five stages of secure SDLC?
The secure software development life cycle contributes protection and assurance to each development process and prioritises end-to-end protected user experiences. Everyone interprets secure SDLC in different ways, but the approach to securing the software remains the same.
You may find secure SDLC comprises 5 or 7 stages at multiple places. But you do not need to get confused with it because either it is five stages process or 7; all of them serve the mutual goal of analysing, developing and securing the software against known-unknown security issues.
In addition, the secure SDLC stages serve as best practices for every developer and software development company. Therefore adherence to a secure software development life cycle (SDLC) eventually leads to you adhering to best practices of the secure development process.
Following are the common five stages of the secure software development life cycle (SDLC).
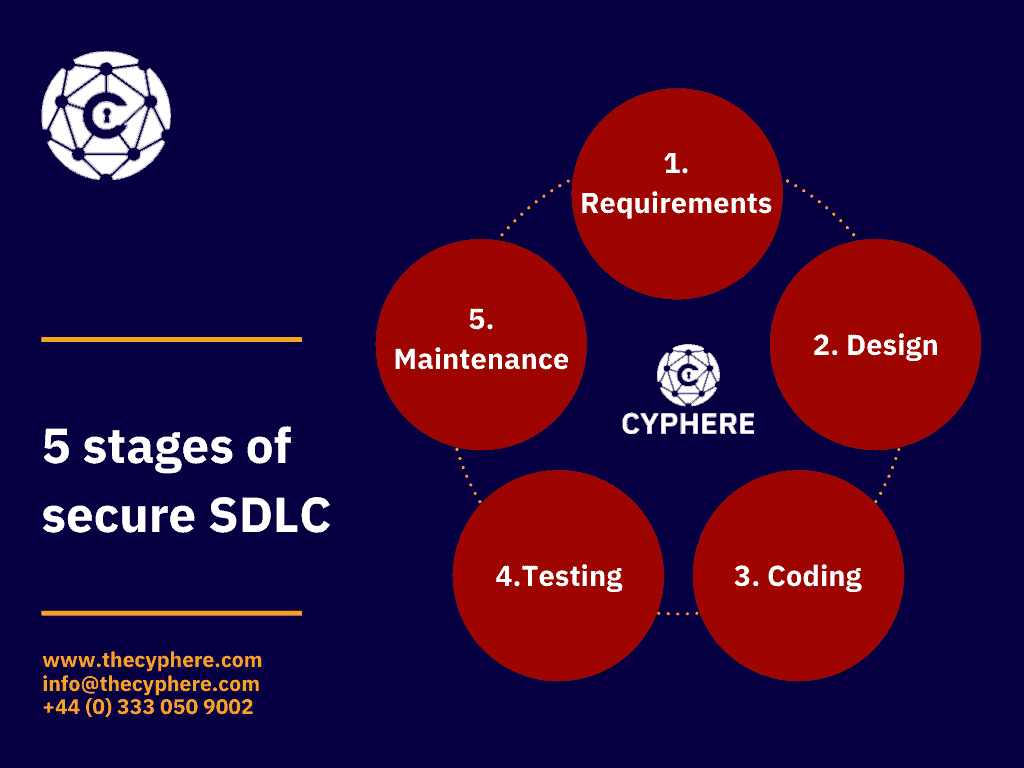
Requirements
The first stage of the secure software development life cycle (secure SDLC) is about requirement gathering and is also known as the planning phase. In this stage, you collect all the application requirements to plan a smooth and error-free application field.
This includes scheduling project timeline, planning, cost estimation, and project (software) goals analysed with the security specifications. At this stage, you must evaluate software or application key areas with security considerations and seek the solutions in advance.
In summary, during this stage, your requirements for software features are collected from the stakeholders and management team and mapped with multiple abuse cases to review the security risk with each functional condition.
Following are some of the security considerations that you can gather and decide in the requirement phase with the optimal solution in the secure SDLC processes:
- Determination of software functionality with end-user experience
- Identify all resources required for the development, such as human resources, third-party libraries, cost, compliance, etc.
- Identification of software data classification and policies according to the regulatory body, data classification, i.e., whether software stores any sensitive, financial, healthcare data, etc., must comply with the regulatory bodies such as HIPAA, PCI, GDPR, etc. If yes, how would data meet the regulation requirements?
- Software resiliency against attacks such as brute force, credential stuffing, etc.
- Data encryption, sharing and storage mechanism
- Login, Multi-factor authentication requirements
Design
Once requirements are gathered and you plan out the software security requirements, it is time to move on next phase of secure SDLC, which is designing. In the design phase, you can assess what technologies and techniques would be used, what will be the software architecture, and what security activities, coding and framework would be followed for the development model.
Similarly, API, SDK, front-end, back-end, cloud service, data flow, application modules, database, network communication, etc., are analysed in this phase. Along with evaluating all designs, you perform the architecture risk analysis, gap analysis and threat modelling side by side to consider the business risks on the system’s functionality.
In essence, this SDLC process translates all the gathered requirements and shows how the application will look in real. It involves creating the functional requirement with the design such as:
- Analysis of authentication and authorisation mechanism along with the procedure to authenticate the requests
- Implementation of measures to prevent access control or remote attack
- Investigation of software behaviour under circumstances such as insecure cryptogram, invalid session token, security control bypass, and much more.
Development/ Coding
Here in this stage, all of the documented software design and requirements are developed with secure coding practices. This is a broad phase in which your developers are provided with a secure code practice guideline to align the software features and design with the security consideration.
All of the written codes, third-party libraries, and open-source components are tested with static, dynamic, automated and manual security testing to remove unnecessary codes and detect software and business logic flaws that could be triggered with code manipulation.
Coding practices vary with application specification; there are multiple guidelines that you can follow according to your product, such as CWE Top 25, PA-DSS, OWASP Top 10, DISA STIG, etc. Have a look at our PHP security guide to help you gain edge on secure coding practices:
Testing
Now your codes are verified and suitable to go, it is time for you to integrate all of your unit cases and deploy the application. But before the software release, you must perform detailed security testing to discover underlying security vulnerabilities that an attacker could benefit from compromising your application and breaching it.
You can test your application with an assessment like vulnerability scanning and penetration testing to identify critical flaws that might have been missed earlier.
This stage is important to ensure full-stack security and cross-check the server’s configuration, back-end controls, and best security practices. You must not deploy your software unless you remediate all identified risks.
Maintenance
This is the most critical stage of the secure software development life cycle (secure SDLC) and an ongoing development process. Once your software is released and go live in the real world, there is a high probability that attackers will try to intrude in.
In addition, you may discover flaws and glitches due to any reason, and you must patch them before it affects the customer trust cost, financial loss, or brand reputation.
Maintenance focuses on continuous improvement with both user and security perspectives to meet your requirements gathered in the first stage of secure SDLC. Whatever flaws or threats come in, the maintenance, you should resolve everything through appropriate patch management policies, annual or quarter penetration tests, annual third-party risk assessment and on-demand compromise assessment.
Secure software development lifecycle (SDLC) Best Practices
Here is a list of secure SDLC best practices for organisations looking to secure their development lifecycle:
Educate your developers/ development teams
Your development teams put the soul into your application development process. This is why they need to be aware of security testing and ongoing attack trends. Train your developers with professional education, secure coding guidelines, and security best practices.
So, whenever they start designing and creating an app, they are aware of implementing straightforward security controls and seeing the consequences of their insecure scripts.
Set precise requirements
Whenever you think of designing an application or software, always start with setting a clear goal and then map the security specification around it. It would help if you had all element priorities with associated security and regulatory requirement.
Hence, you do not get the last-minute hassle of incorporating or adjusting the security assurance activities.
Always test
The key to a secure application (software) is to verify the effectiveness of implemented code and security measures. Whenever you create software, test them with white box and black box techniques, penetration testing, source code review, full-stack security test, etc. to be aware of internal and external threats.
While testing your application, do not rely upon automated tools because your tools cannot compete with human intelligence and attacker mindset. Always do manual checks on the business logic flaws or critical app functionality to ensure they are resilient enough against attack.

Promptly patch
There is always a new attack trend and threats that you must mitigate before any attacker tries to exploit it. Either through the latest attack trend or security assessment, you can identify security flaws in your application after its release.
Then, whenever you encounter a bug, patch them promptly to secure your application. Often one minor vulnerability provides a pathway to multiple vulnerabilities that, if exploited, collapse the overall security posture.
Get in touch with us to discuss your security concerns around the secure software development lifecycle (SDLC). We offer a complete suite of the application development cycle to address and restrict vulnerabilities from affecting application security and disrupting the functionality.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.