Data classification policy is the predefined course of action that helps to identify the sensitivity of the data. The actions include categorizing data in a way that reflects its sensitivity, such as protecting data for confidentiality, integrity, and availability.
In this blog, you will learn what you need to know about the necessity of classifying data as senior management, the procedures to classify data, and how to establish a data classification policy effectively.
The concept of data classification policy
A data classification policy is primarily concerned with information management to guarantee that sensitive information is handled appropriately in light of the threat it poses to an organisation.
Additionally, it considers how the collected data is used and structured inside an organisation, allowing authorised individuals to obtain the appropriate bits of information at the appropriate time while guaranteeing that only authorised personnel permit access to view information.
Any organization’s database contains data that varies in terms of its sensitivity, meaning that certain data are more sensitive than others.
Is the classification of data is same as risk analysis?
Classification of data, security policy, and risk analysis are all interrelated tasks that businesses utilise to improve security i.e.
- A data classification policy embodies the organisation’s risk tolerance.
- A security policy is a high-level document that expresses the senior management purpose about how information security is to be accomplished, what activities are permissible, and the quantity of risk that the organisation is willing to take. A data security policy, for example, might conduct a risk assessment or classify the organisation’s data.
- Risk analysis maps organizational assets against risks having a serious adverse effect and serves as a trigger for establishing risk-mitigating remedies.
As a result, data classification policy and risk analysis are distinct concepts that are included under the umbrella of security policy.
What are the three data classification labels?
The three classification labels for data are as follows:

1. Restricted or Confidential data
Restricted or confidential information refers to data that, if compromised or accessed without authorisation, might result in large legal fines or catastrophic adverse effect on the business. Specific authorisation and/or approval are required for access to this type of data. Social Security numbers, cardholder data, and mergers and acquisitions paper documents are all examples of confidential data. Generally, confidential data is safeguarded by legislation such as HIPAA and the PCI DSS.
2. Sensitive data
This sort of data is available to only senior management. This might contain an internal-only human resources folder for senior managers, electronic form paper documents as well as other correspondence, business strategies, and so forth.
3. Public data
This kind of data is available to the whole public (i.e., all employees/company workers, third party agents). It is completely free to use, repurpose, and share. First and last names, job descriptions, press releases or company newsletters are all examples.
How does the data classification policy work?
A data classification strategy describes the relationships between various components within an organisation.
It then evaluates all metadata of the data that belong to the organisation and classifies them based on their storage location and access permissions. These data be classified based on their classification labels such as confidential, sensitive or, public.
The data classification policies should also take into account any industry-specific data classification labels or categories described by several standards such as ISO27001, NIST etc.
What are some essential advantages of data classification policies?
Businesses gain in a variety of ways by establishing a data classification policy, including the following:
- Data classification policies assist an organisation in determining the types of data that may be used, their availability, their location, the access, data integrity, and security levels that are required, and whether or not current handling and processing implementations comply with data protection laws and regulations.
- It is the most effective and efficient method of data protection since it aids in the categorization of data in order to safeguard crucial data such as medical records, financial records, research data and protected information. If this crucial data falls into the wrong hands, firms may face penalties for breaking laws and regulations, as well as financial loss or harm to their reputation.
- Organizations can use information classification rules to ensure compliance with regulatory requirements, industry best practices, and consumer expectations.
- Additionally, it assists companies in maximising allotted security budgets by allowing them to prioritise security measures depending on the quantity of data that must be protected, its location, and the threat landscape.
What are the steps to classify data?
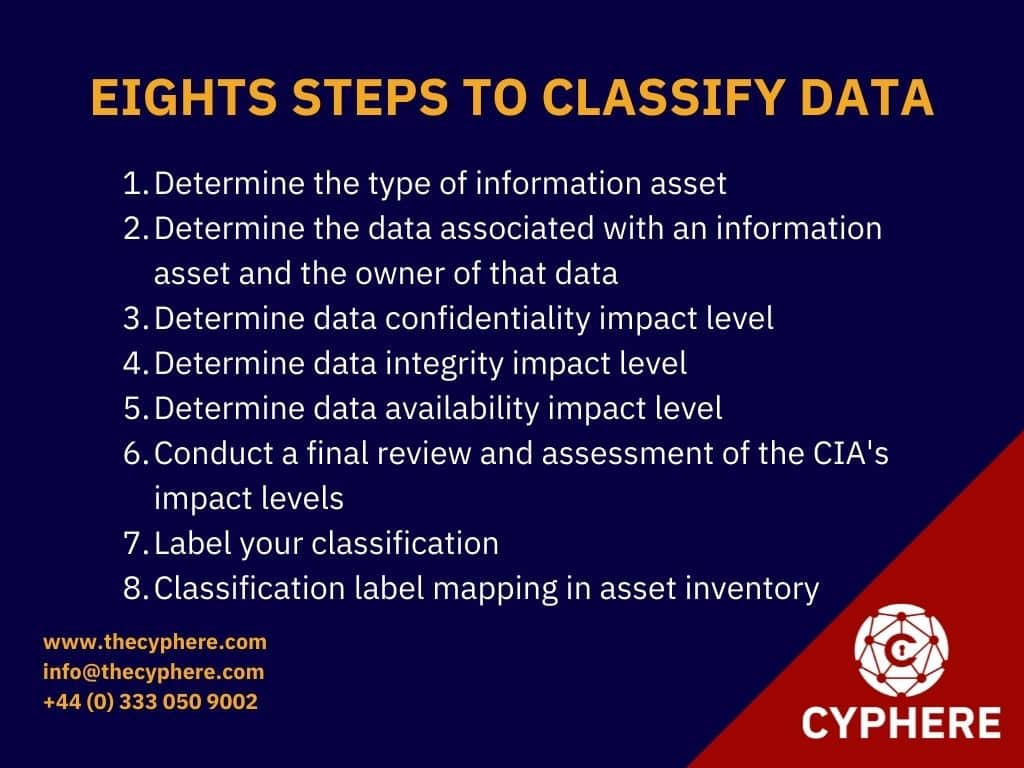
The following are the mandatory steps for every type of information classification procedure:
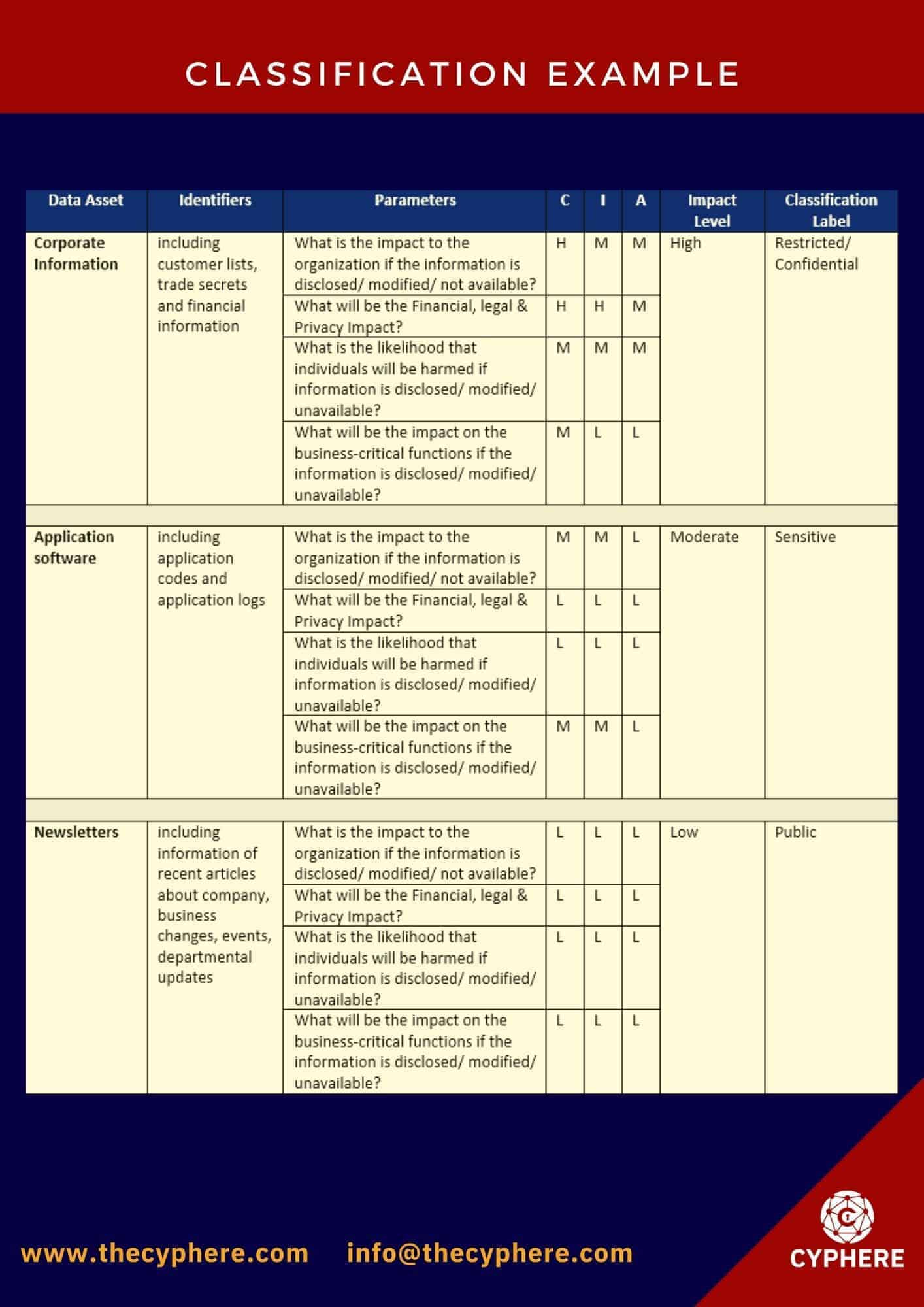
1. Determine the type of information asset
Determine if the asset is information, an application, software, a service, or any physical asset.
2. Determine the data associated with an information asset and the owner of that data.
Define the sort of data included in an information asset, such as business data, employee data, marketing data, or personally identifiable information (PII). Define the owner of that data identifier as well.
3. Determine data confidentiality impact level
Ensuring authorised access to and disclosure of personally identifiable, proprietary, and protected information by establishing the level of confidentiality. The impact level can either be low, moderate or high.
4. Determine data integrity impact level
By determining the level of integrity, you may protect data against alteration or destruction while also assuring nonrepudiation and authenticity. The impact level can either be low, moderate or high.
5. Determine data availability impact level
Determining the amount of data availability is critical for guaranteeing timely and reliable access to information. The impact level can either be low, moderate or high.
6. Conduct a final review and assessment of the CIA’s impact levels
The final impact level of the CIA triad will be determined in accordance with the highest degree of Confidentiality, Integrity, or Availability assigned.
– Any parameter with a high rating will have a high overall influence on the entire CIA triad.
– For the whole CIA triad, all moderate ratings will result in a moderate level of impact.
– All low ratings result in a low level of influence over the whole CIA triad.
– The combination of lows and moderates will result in the CIA triad having a moderate impact level.
7. Label your classification
– For data with a final impact level of High, it will be classed as Confidential.
– Data categorised as Public shall have a final impact level of Low.
– All other data must be designated as Sensitive.
8. Classification label mapping in asset inventory
Each information asset should have a classification label associated with it.
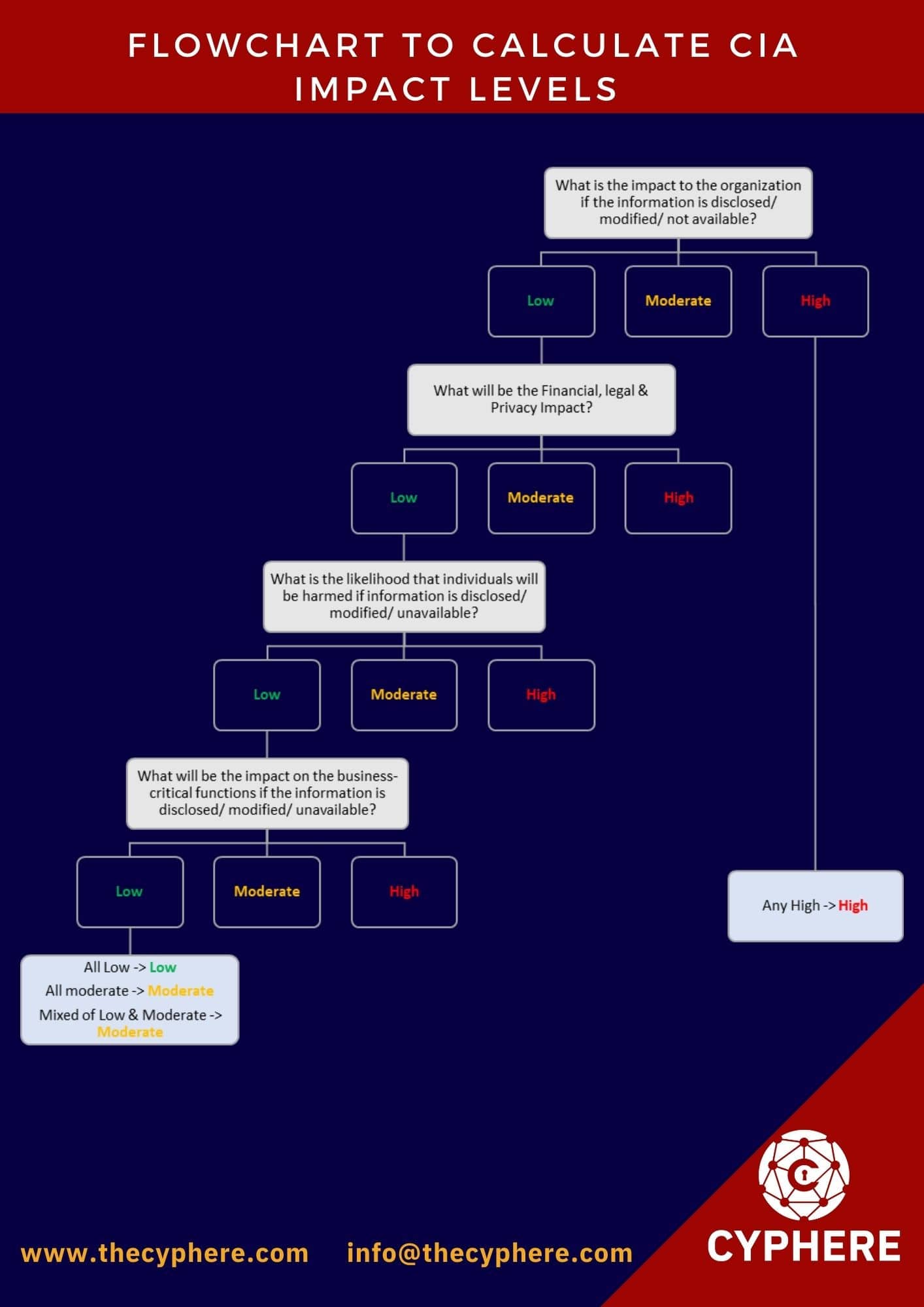
How to determine the CIA impact levels?
The flowchart below will aid organisations in calculating the confidentiality, integrity, and availability levels associated with each piece of data and classifying it according to the established classification labels.
Example
Confidential data Types That Are Predefined
According to state and federal laws, the following data types have designated different categories of Restricted data. This is not an exhaustive list of limited data types. The following are the predefined categories of confidential data:
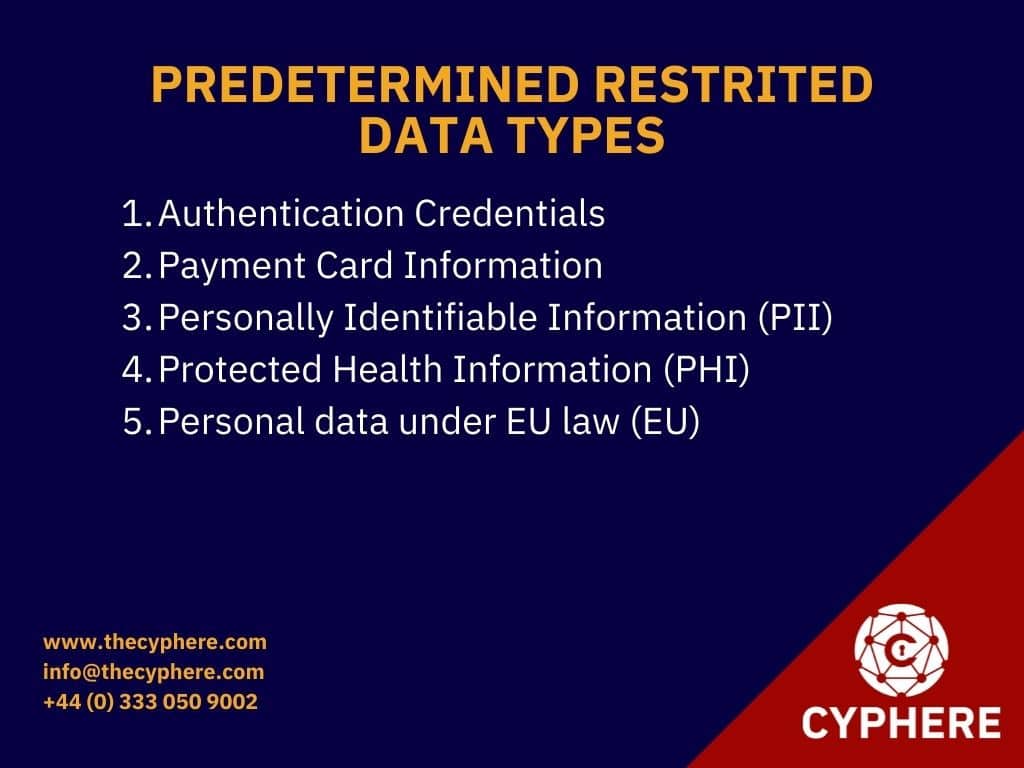
Authentication Credentials
The authentication credentials are pieces of information that an individual maintains in confidence and uses to identify that the individual is who they claim to be for example:
- Passwords
- Exchanged secrets
- Symmetric cryptographic keys
- One time passwords (OTP)
- Security questions
Payment Card Information (
Payment card information is described as a credit card number (sometimes called a primary account number, or PAN) in conjunction with one or more of the following data elements:
- Name of the cardholder
- Date of card expiry
- Values for the CVC2, CVV2, and CID
- PIN or block of PINs
- Magnetic stripe information on a credit card
Personally Identifiable Information (PII)
PII is defined as a person’s first name or first initial and last name in conjunction with one or more of the following data components:
- Social security number
- Driver’s licence number issued by the state
- An identification card issued by the state
- Combination of a financial account number with a security code, access code, or password granting access to the account
- Health-related and/or insurance-related data
Protected Health Information (PHI)
PHI is defined as health information that is to be protected that is transferred or retained electronically, or in any other form or medium by a Covered organisation. If a piece of PHI has one or more of the following identifiers, it is deemed personally identifiable.
- Identifying Data (all geographic subdivisions smaller than state including street address, city, county, precinct or zip code)
- All dates (save the year) associated with an individual, including the date of birth, the date of admission, the date of discharge, the date of death, and the precise age if above 89)
- Contact information
- Medical histories
- Home address
- Fax number or email addresses
- Medical record number
- Beneficiary data from health plans
- Identification and serial numbers for vehicles, including the number assigned on the licence plate
- Serial and device IDs
- Internet protocol (IP) addresses Universal Resource Locators (URLs)
- Finger and voice prints are examples of biometric identification.
- Photographs of the entire face and any photographs that are comparable
- Any other identifying number, feature, or code that may be used to uniquely identify an individual
Personal data under EU law (EU)
Personal data is defined in the EU’s General Data Protection Regulation (GDPR) as any information that may be used to directly or indirectly identify a natural person by reference to an identifier, including
- An identification number assigned to an individual.
- Data on the geographical location
- An identification for use online
- One or more characteristics unique to that particular person’s physical, physiological, genetic, mental, economic, cultural, or social identity
Some best practices for creating a data classification policy
The following are some best practices for designing a data classification policy:
1. Leveraging automated technologies to assist in speeding the data classification process by automatically assessing and categorising data according to pre-defined parameters.
2. Determining the information system, their data processing activities and security controls to understand the sensitivity of data .To fully comprehend the systems and their sensitivity, the following critical questions must be asked:
- What information system is used to store this data?
- What location does the data reside in?
- What security controls are deployed to these systems?
3. Appoint an information security analyst tasked with the responsibility of managing the organisation’s records.
4. A comprehensive investigation must be conducted to determine whether rule or regulation applies to the company; this is critical and should not be disregarded, since many security and privacy regulations now include monetary penalties for noncompliance.
Conclusion
A data classification strategy serves as the foundation for successful security measures in today’s companies. Without consistent classification policies, it is hard to safeguard sensitive information adequately, after all, you cannot protect it if you do not know it exists, where it is located, or if it requires protection at all.
Get in touch to discuss your data classification procedures and policies and learn how to create a classification policy for your business.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.