Using security best practices helps businesses establish a security baseline and protect their AWS infrastructure from potential risks. By implementing these practices, companies can reduce the likelihood of data breaches, leaks, and other threats. Additionally, using security best practices can help businesses detect and respond to threats more quickly and effectively. As a result, companies that implement security best practices can improve their overall security posture and better protect their data and resources.
As a security consulting company, we are often asked to carry out AWS pen tests in different forms, i.e. security reviews of AWS assets, network penetration tests and cloud portal reviews to benchmark customers’ AWS assets. Therefore, security best practices act as a good baseline.
Why is AWS security so important?
AWS infrastructure provides unmatched infrastructure services to its customers. However, the growing complexity of the technology stack where applications, networks and databases are deployed on a cloud environment sometimes leads to unattended data exposure.
Hence it is essential to ensure that AWS security features are utilised fully where the business requirements allow them. For example, a company may decide to enforce rigorous security controls on the part of the application that deals with sensitive data such as credit cards etc. and leave the other part of the application that deals with data that is supposed to be public.
AWS believes in a shared security responsibility model. This means that while AWS is responsible for ensuring the security controls of the underlying cloud infrastructure, the customer is responsible for securing applications and containers deployed on the AWS cloud. This allows the customer to implement appropriate security controls per their business requirements.
List of AWS security best practices
Once you have created an AWS account, you might want to start using the services immediately. However, AWS recommends first following security best practices to protect the AWS resources better. To facilitate users and organisations in creating a solid security posture, we have combined a list of AWS security best practices and tips.
What is Cloud Computing, and why is it important?
Cloud Computing is a terminology that people who are not tech-savvy have trouble understanding. What cloud service providers like Amazon AWS do is that they develop their own data centres with all the essential hardware equipment such as servers, network devices, storage devices etc. These data centres are hosted at many locations worldwide, and the companies nearer to any of those data centres can utilise AWS data centre infrastructure as a service. This gigantic pool of computing, network and storage AWS resources outsourced to companies is said to be “in the cloud” somewhere.
Hence the term Infrastructure as a service was born, and it became a popular model for those companies who just wanted their infrastructure to be created and maintained and did not want anything to do with the physical aspect. This enabled the companies of the modern era to avoid the cost of buying bare hardware metal and instead just rent the resources of cloud service providers like Amazon AWS and pay only for what they utilise. We at Cyphere aim to help customers by identifying misconfiguration and weaknesses in the cloud infrastructure using a cloud penetration testing service offering.
The concept of infrastructure has been revolutionised by the on-demand availability of cloud AWS resources. Companies can expedite their business processes by focusing their investments on operational expenses rather than capital expenses. Amazon AWS Cloud services are a reasonable option for small businesses and large international enterprises.
What is AWS?
Amazon Web Services is a robustly secure cloud computing platform that offers computing power, storage space, content delivery and other functionalities that assist businesses in scaling their online presence.
AWS allows businesses to:
- Host and run dynamic web applications on AWS servers with high computing and high bandwidth
- Securely store their data and files while still allowing them access from anywhere
- Host managed databases like Oracle or MySQL on cloud servers to store information processed by applications
- Provide smooth delivery of static and dynamic files via Cloud Delivery Network (CDN).
- Sending bulk emails to their customers.
What is AWS security?
AWS Security features a wide range of tools and services that ensure the security of the public cloud service. AWS claims that it is the only infrastructure as a service that is as secure as it is flexible. It has been ranked as the best IaaS provider in Gartner Magic Quadrant for eight consecutive years.
AWS also provides a whitepaper, “Introduction to AWS Security”, a comprehensive document containing details about implementing AWS security and AWS’s approach to security. AWS infrastructure is a highly scalable and reliable platform that allows businesses to host applications and provide continuous service with security measures enforced.
The AWS infrastructure was built keeping in mind that unique cloud needs must be catered to while following security best practices. AWS offers round-the-clock monitoring and protection of the underlying infrastructure by using layered security controls, performing security testing and automating these processes.
AWS implements these security controls in every data centre worldwide as it provides services to the most security-sensitive customers. So with AWS, customers not only have a robust infrastructure with sophisticated security controls but also do not have to bear the high cost of establishing their physical data centres.
Plan a strategy before starting implementation.
Before getting down to the nitty-gritty of implementation, it is essential to focus on developing a robust strategy. The strategy should include the problem statement, the objective an organisation is trying to achieve, the technologies, tools and controls that would be implemented and what security risks they would mitigate.
Implementing all tools and controls should complement an organisation’s strategy across all organisational functions.
AWS assets categorisation
Before implementing any security controls, it is essential to identify which assets or information need protection and the criticality of that asset. Identifying critical assets or information and categorising them will make it easier to decide what type of security controls are required.
Assets can be of two types:
- Essential elements: These consist of web apps, customer data, personally identifiable information, financial data etc.
- Secondary components: This comprises software, personals, partner organisations etc.
Information Security Management System (ISMS) design
Once a strategy is made, and all the AWS assets are identified, an organisation needs to design and develop an ISMS based on a standard (such as ISO 27001).
Enforcing an ISMS will help an organisation implement, monitor, operate, review, maintain and improve the security aspects of AWS.
Security groups categorisation
It is always good to categorise an organisation’s security groups. For example, one AWS security group could consist of all database server and web server connection ports; the other AWS security groups can include all media connection ports, another AWS security group for all third-party connection ports and a completely separate fourth security group for all office-specific ports.
Categorising this way ensures that all different sets of connections are dealt with separately, minimising the risk of human errors when any changes are needed.
Managing AWS accounts, groups, and roles
When an AWS account is initially created, the user account has root permissions, i.e. it is the most powerful account with the highest privileges. Root AWS account should not be used for any day-to-day activities, so creating IAM users is recommended instead and assigning each unique user credentials is recommended.
These IAM users can be a person, application or service that requires access to AWS resources. The permissions and privileges given to each user have been configured very fine-grained manner.
The principle of least privilege should be adopted when assigning permissions so no user has access to resources except the necessary ones.
Groups of multiple users can also be created, and permissions can be applied to the security groups rather than individual users. This is a more practical approach.
For administrative purposes, create an IAM user and give that user administrative permissions rather than using the root user itself.
SSH keys should not be shared
SSH keys are used to get remote access via SSH. When creating SSH keys, remember only to make one SSH key per person, regardless of the number of devices (laptops, desktops) that person uses.
Also, enforce users to keep their SSH keys private and not share them with anyone else.
Avoid using expired certificates.
Do not use expired TLS / SSL certificates as, in some cases, they will no longer be compatible with the AWS services. If an organisation continues to use expired certificates, it can lead to errors for ELB or custom applications, impacting productivity and decreasing overall security.
Enforce and create strong passwords
To protect the AWS resources, ensure that password policy guidelines are followed, and strong passwords are used, including letters, numbers, special characters, etc.
If needed, third-party password managers can also be used.
Granting temporary access
During business operations, at times, specific scenarios may arise where a user needs elevated access or privilege to a system or resource to which he currently does not have access. In such cases, it is best to grant temporary access to resources using IAM roles.
IAM roles are a set of temporary permissions or security credentials that can be assigned to users on an as-per-need basis. These roles are equipped with configurable expiry dates and can be automatically rotated, which means the same role can be set to multiple users.
Using these roles ensures no human interaction is involved in assigning and revoking the access granted; all of this is carried out automatically, thus reducing human error.
Use resource access authorisation
After an IAM role is authenticated, access to system resources is granted. An organisation can control this access by implementing adequate authorisation controls using capability and resource policies.
With the help of these policies, access to resources can be controlled in a very fine-grained manner, such as access can be restricted to a particular source IP address or IP range, access can be limited during specific times of the days, or on particular days, apart from this many other conditions can also be configured.
Encrypt all sensitive information
AWS always recommends its customer encrypt all sensitive information, and AWS offers their native encryption in which end-to-end SSL/TLS and HTTPS for AWS service APIs are provided. Enabling the native encryption requires checking a box, so there is no needed tedious implementation.
Securely store encryption keys.
When an organisation uses encryption, the question of keeping the encryption keys secure comes to mind. AWS offers key access management to ensure the environment stays secure and there is no data loss.
Delete the data securely
When any data is deleted from AWS, the underlying physical media is not decommissioned. Instead, the storage space is marked as unallocated, and AWS reassigns these blocks elsewhere.
It is important to decommission sensitive data for data that fall under regulatory requirements. Best practices include encrypting the data at rest using customer-managed keys that are not kept on the cloud.
Protect data at rest and in motion
An organisation’s data can be stored in Amazon EBS, Amazon S3 or other Amazon services. This data at rest should be protected by implementing policies to properly control access, data classification, data retention and deletion. Any sensitive information within the data at rest should also be encrypted.
For data in motion, encryption methods using SSL / TLS or IPSec ESP can be used. All sensitive information, including administrative access communication, should be encrypted to ensure data integrity and confidentiality.
Protection from malware
Like any other asset on a physical network, the cloud infrastructure must also be protected from malware and outside threats; this can be achieved by installing anti-virus or anti-malware software on the AWS instances.
Security monitoring
To protect the AWS resources from malicious threats, it is essential to notice when something is out of the ordinary. For this, it is necessary to benchmark normal activities and monitor for anomalies.
For example, if a website suddenly receives a lot of traffic which is not normal, then this traffic might cause a Denial of Service and must be blocked.
Tools such as Threat Stack can monitor more than one AWS account for any malicious behaviours using a single dashboard.
Implement MFA (Multi-Factor Authentication)
Configure the root users and other IAM accounts to use multi-factor authentication; this will protect the AWS account even if some attackers get a hold of the user’s password.
Avoid hard-coded secrets
While building apps on AWS, sometimes these apps require credentials and keys such as API or database credentials. These secrets should not be hardcoded in the source code or in the app.
Rotate credentials
Change passwords and access keys for all root and IAM users periodically. This will ensure if any password or access has been leaked, an attacker would not be able to use that. Access keys should be rotated regularly.
Delete access keys for root accounts
AWS recommends not creating access keys for the root AWS accounts for programmatic access, and if you have, delete those. Instead, create IAM users with the required permissions for the API calls and use access keys associated with the IAM user instead.
Do not share access keys.
The access keys provide a way to give access to AWS services programmatically. As mentioned above, do not complex code these keys and do not share these keys with anyone.
Configurations of CloudTrail
By default, CloudTrail can record the events for every AWS account and retain the logs for 90 days. However, this does not record all types of events. Configure CloudTrails to record all events associated with the AWS account for all regions.
Create regular backups
Ensure that backup is taken for all applications, databases, etc., regularly, so no information is lost. AWS Backup can be used to centralise and simplify this process.
Implement network segmentation and security zoning
Just like with a physical network, it is a good practice to segment the cloud infrastructure into various zones and implement security control.
Implement network security
AWS configures all infrastructure components such as routers, switches and data networks, and the owner controls the access to the cloud. Network security can be configured with Amazon VPC and directed inbound and outbound network traffic.
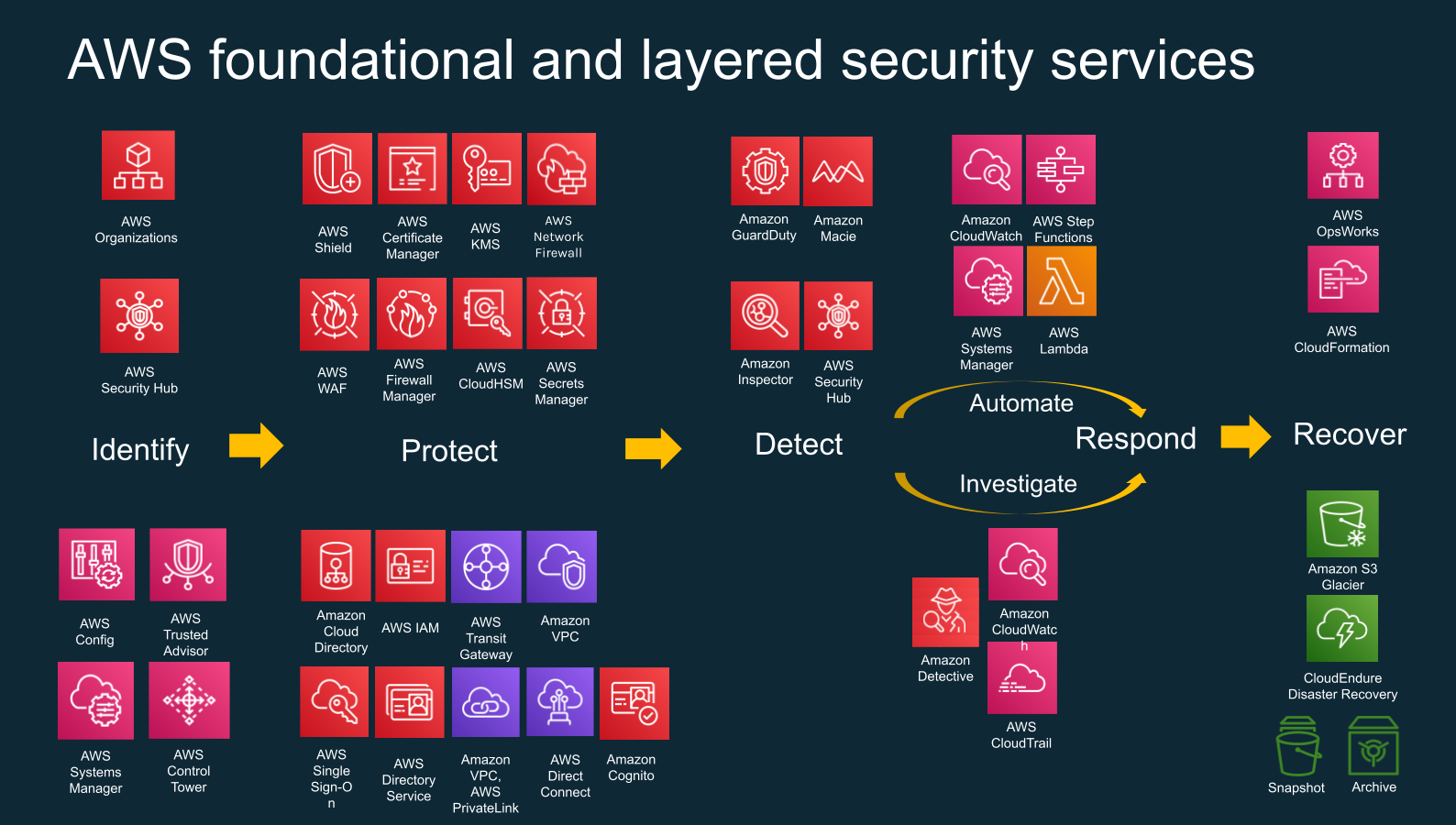
Building a layered security model
Security should be implemented on all layers, and AWS is no exception. A combination of firewall rules, Amazon VPC, network access control lists and default security groups in the cloud create a layered approach to security and maximises protection.
Protection against DoS and DDoS
AWS Cloud infrastructure, like other assets on the internet, also faces the risk of a Denial of Service (DoS) attack. To ensure uninterrupted delivery, the DoS risk must be mitigated. This can be achieved by utilising Load balancers, Web application Firewalls (WAF) and Content Distribution Networks (CDNs).
Use managed IAM policies.
Different Identity and access management policies can be used for different types of Security Hub users. This means that specific permissions can be given to users depending on their needs and assigned privileges. Access control must be ensured by following the Principle of Least Privilege and giving Security Hub to write permissions to trusted users only.
Knowing the user and reason for accessing of database
To ensure database security, it is essential to identify which user is accessing the database servers and what is his purpose. The principle of least privilege must be followed while assigning administrative rights to users.
Moreover, data in transit encryption and data integrity validation controls should be in place to ensure data from other sources remains secure.
Use tags for access control
Amazon web services Security hub also provides a metadata tagging feature where each tag contains a key-value pair that helps the customer manage resources. Tags help identify similar resources with one tag and manage access to it.
As per the best practices, it is crucial to use name tags for resources as they allow management of the resources with the same tag individually.
Involve the security team throughout the development lifecycle
Security and development must go hand-in-hand. Security controls must be implemented throughout the application’s development lifecycle and not as a separate process done after the application has completely developed. Ensuring security controls at every stage allows the developers to mitigate the weaknesses as soon as they are discovered.
Grant the minimum privileges to application users
Any application or user must be given the minimum privilege required to complete their function. Users or applications with unnecessary applications increase the risk of data loss if that user or application is compromised.
Remove unused security groups.
As more security groups are created for different needs, it is expected that some groups stay unused. It is vital that these security groups who are not attached to any instances are deleted to ensure that the AWS environment remains clean.
Deleting unused groups also removes the risk of human error, such as mistakenly attaching the unintended group to an instance.
Create security policies for groups over users
As per the security best practices, assigning policies to security groups rather than to individual users is recommended. Fine-tuning an access policy is much simpler when it is attached to a group rather than multiple unique users.
Ensuring validation of policies
Validating the policies is also considered one of the security best practices. Identity and Access Management(IAM) identify syntax errors and provides more than 100 policy checks and actionable items to write more secure and optimised policies.
Managed policies over inline policies
It is a recommended best practice by Amazon web services to use managed policies instead of inline policies when utilising custom policies. The managed policies can be viewed from a single pane of glass in the AWS management console.
Managed policies can be attached to multiple users as opposed to inline policies, which can only be connected to a single user.
Time email notification for critical alerts
It is of paramount importance that security teams are notified immediately in case of suspicious activity on AWS infrastructure. Security professionals need timely alert notifications to investigate the incident and take necessary corrective actions. Timely detection of unauthorised activities like deleting access control rules can avert a significant security breach.
Careful handling of multiple security groups
One must create security groups carefully. Multiple security groups can be applied to a single instance, or a single security group can be used in various cases. So when numerous security groups are devoted to one example, there are high chances the security group rule becomes overlapped.
For example, one of the security groups might open port 443 to the entire internet while the other security group may only open it for one IP address. If both security groups are assigned to a single instance, the enforcement of security groups may be inconsistent.
- Data Security Breach
- NIST Framework
- Software Development Practices