Service accounts can be privileged local user or domain user accounts or have domain administrative privileges. Service accounts best practice involves usage to execute applications and run automated services. A single service account can easily be referenced in many applications or processes. The critical nature of their usage and their use makes them challenging to manage. In this post, we will explore service account’s work, some everyday use cases and account types across different environments, best practices and solutions for managing and securing service accounts.
What are Windows service accounts?
Windows service accounts are a particular type of account required to run a specific service or are associated with an application that runs a specific service in the Windows environment. These services may include Microsoft Exchange Server, SharePoint Server, MsSQL Server, Internet Information Service (IIS) Servers etc. These accounts provide a security context for the services they run. For example, they may determine what local or network resources service or the application running the service is allowed to access.
What is service account management?
Service accounts are extremely common and widespread, and the risk of being an easy target has increased. It is critical to monitor, administer, and audit service accounts in order to mitigate these risks.
Service account management is a problem that too often goes under the radar since controlling them might be difficult. When done manually, it’s time-consuming and could lead to misconfiguration, errors or other issues. Especially where privileged accounts are part of the discussion, service account management is a critical task for IT/security teams to ensure misuse can be protected.
What is a directory service?
Directory services store and identify information like email addresses, users, peripheral devices, and computers within a network. Directory services hold this information shared within the infrastructure to manage network names and access resources to users and applications.
Directory services enable users to access resources on the network without knowing the physical addresses of those network resources. Directory services are a critical component of a network operating system. It serves as a central repository of information and a central source of authentication of directory users and computers within a domain-joined network.

What is Active Directory?
Active Directory (AD) is a database of users, applications, computers, services and other important objects that make up an organisational network. The active directory serves as a central authentication and authorisation platform for all the users and applications within a network. It allows users to access network resources as per the access control policies defined in the active directory.
In short, an Active Directory is a tool that provides centralised authentication of users, central authorisation of resources and any other security context configurations that users, computers, groups etc., can classify. Active Directory achieves all these feats in an integrated and straightforward manner unmatched by any other 3rd party solution for Windows.
Why is Active Directory used?
Active Directory is not a must-have solution for every organisation. With that being said, the advantages of Active Directory make it a no-brainer for almost every organisation. For example, consider there are 100 users within an organisation. There are two ways to control access within the infrastructure.
- Manage privileges by creating multiple local user accounts on every computer.
- Centralised authentication of directory users and computers and authorisation of resources.
Organisations may consider using the first method. However, the number of computers may increase unknowingly in the next few years. Using an active directory allows the organisation to use a scalable central authentication and authorisation tool.
Another significant advantage of Active Directory is instant revoking access for employees who no longer work at the organisation. Consider an employee fired from an organisation, and the IT administrator is instructed to revoke their access. With Active Directory, the IT administrator can disable/delete the user account from the active directory domain controllers, and the user will not be able to log in from any endpoint within the network.
How does an Active Directory work?
Active Directory stores data in the form of objects. An object is a single element like a user, group, application or device. Active Directory categorises things by their names and attributes. For example, a user object may have the following qualities; i.e. its name, group membership, passwords and SSH keys.
The leading service in AD is the Directory Service (DS), which holds all the information about objects and handles the interaction of users, applications and services with the domain. The AD DS verifies the user account upon authentication and controls what user has access to what resource in the domain.
What is a service account in Active Directory?
A service account in Active Directory is a specific user account used by an application or service to interact with the Windows operating system. Service accounts may be used to make changes to services or applications’ configurations. Services or applications may also access network resources as defined by the permissions on the corresponding service accounts.
Where are service accounts in Active Directory?
The Get-ADServiceAccount PowerShell cmdlet searches the domain for group managed service and returns one or more service accounts according to the user’s query.
The ‘Filter or LDAPFilter’ parameter of the cmdlet is used to search for one or more service accounts. The ‘Filter’ parameter leverages the PowerShell Expression Language and queries the domain for service accounts matching the string defined in the parameter.
Example:
Get-ADServiceAccount -Filter "HostComputers -eq 'CN=SQL-Server-1, DC=example,DC=com'"
This command gets the managed service accounts allowed on the computer CN=SQL-Server-1, DC=example,DC=com.
You can also identify a service account by its distinguished name, SAM account name, GUID or SID, and query the domain using the same cmdlet, i.e. Get-ADServiceAccount with the Identity parameter.
Example:
Get-ADServiceAccount -Identity testsvc
This command gets a managed service account with SAM account name testsvc.
What is the difference between a user account and a service account?
User accounts are created for real users trying to complete their daily assignments within an organisation. While service accounts are designed for applications or services running within the organisation’s infrastructure.
service accounts vs user accounts
When discussing service accounts vs user accounts topic, think of this similar to systems versus user usage of accounts. Most of the applications, services/and software utilise service accounts without interactive logon and user accounts are used by humans.
For example, suppose the organisation wishes to host a local web application. In that case, it can utilise an IIS Service account to an IIS Web server and deploy its desired application on that server. Similarly, that web application may need to store data in an MSSQL Database. For that, the organisation’s technical team will run MSSQL Server with an MSSQL Service account and create a database for their local web application.
Another difference between user accounts and service accounts is that user accounts are allowed interactive login on computers on the network. However, service accounts are not allowed interactive logons since their only purpose is to run a service or application.

Why is a service account required?
Service accounts run automated processes and are used by applications to run a particular service. These services can be backup, database, SharePoint, IIS services etc., and one service account can be referenced in multiple places.
Usually, these services require a persistent application. Service accounts are required for these reasons to run these constant applications and perform actions on behalf of the users.
How do I create a service account in AD?
To create a service account in AD, the following set of Powershell cmdlets can be used:
New-ADServiceAccount -Name "TestAcc" -RestrictToSingleComputer
The above command creates a new service account named ‘TestAcc’ and restricts it to a single computer.
Add-ADComputerServiceAccount -Identity TEST-SRV -ServiceAccount "TestAcc"
The above command associates the service account ‘TestAcc’ with the server ‘TEST-SRV’
Next, we need to install the service account on our server. This can be done using the PowerShell Active Directory users Module:
Install-ADServiceAccount -Identity 'TestAcc'
Now, we can query the domain for our newly created service account using the ‘Get-ADServiceAccount’ cmdlet:
Get-ADServiceAccount -Identity 'TestAcc'
What is a managed service account?
Managed Service Accounts (MSA) were one of the most intriguing features of Windows Server 2008 R2. Managed Service Accounts allows the IT administrator of an organisation to create accounts in Active Directory that are bound to a specific computer. Managed Service Accounts have their own complex passwords which are managed by the Active Directory itself.
Managed Service Accounts login to Active Directory through Kerberos and NTLM protocols. This makes Managed Service Accounts ideal for hosting services and tasks that require authentication and authorisation before granting access to a particular resource or application.
Which type of account should you use for service accounts?
Depending on the organisations’ use case, the type of account used for service accounts may vary. It is recommended to run any service with a Managed Service Account provided that service is able to run with a Managed Service Account.
Selecting the right type of service accounts:
 p
p

What are the best practices for managing service accounts?
The following is the list of service account best practices:
Maintain an updated repository of all service accounts
This helps when creating new service accounts or looking for old and stale service accounts, also helps in auditing if a service account is no longer required.
Keep access limited
Apply the Principle of Least Privileges when creating active directory service accounts. Don’t give service accounts administrative privileges, as a compromise of a service account would compromise the entire domain.
Always create new service accounts
Don’t copy old active directory users service account, as there might be service accounts in the AD that may have administrative privileges. Copying an old service account may lead to administrative privileges for a service account that may not require those privileges.
Prevent membership of built-in privileged groups
Putting the active directory service accounts in groups with built-in privileges can be dangerous as all the members of that group would have access to the credentials of that service account. And in case of account misuse, it would be difficult to determine the offender.
If built-in privileges are required, copy the group, remove all members and only include the service account in it.
Disallow access to sensitive data
Define access control rules and policies and implement ACLs to prevent service accounts from accessing sensitive and critical data. Also, apply ACLs to prevent service accounts from making registry changes or writing to files or folders with higher privileges.
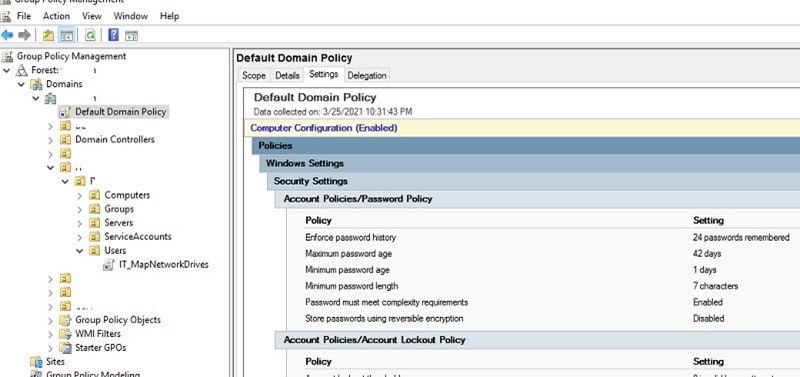
Set up password policies
Most administrators set the password of the service account to never expire or use the same password for all the service accounts. Just like user account, password policies should be created for service accounts as well. Their passwords should be strong, lengthy and complex. Use a Privilege Access Management (PAM) solution or a Password Manager to rotate and create strong passwords, limit and control access, and enforce password policies.
Enable auditing
Enable auditing for all service accounts and related objects. Regularly monitor and check the logs to see who is using the service accounts, what data is being accessed etc.
Limit login scope and time
Limit service accounts to log in to certain machines to prevent these accounts from accessing sensitive data. Additionally, service accounts can be configured to log in only at certain times of the day. Also, don’t allow service accounts to remain logged in.
Clean up an account that is no longer needed
Old and stale service accounts usually are a target for threat actors and can be used to gain access or establish a foothold into your network. Additionally, old and stale service accounts cluster the directory and make service accounts a bit difficult.
Use Managed Service Accounts whenever possible.
Managed Service Accounts cannot perform interactive logons and cannot be locked out. Plus, their passwords are managed by the active directory domain itself, so no human user needs to remember or change the password.
Remove redundant user rights.
Review and remove any unnecessary user rights by creating a group policy object, for example, ‘Deny access to this computer from the network’ and ‘Deny logon as a batch job.’
Windows server service account best practices
A Windows server service account is a user account that is created specifically for running a service on a Windows server. This account is usually created by an administrator during the installation of the service. The service account has specific privileges that allow it to run the service properly.
A list of top best practices to manage Windows server service accounts or service accounts active directory best practices include:
- Do a quick inventory of what service accounts you have and what they are used for.
- Excessive permissions – Interactive logon rights and higher privileges are a strict no! 99% (I’d say all times) of the time, service accounts do not need domain administrator or highest level account access – take action!
- Segregation of accounts – Do not allow administrators to use corporate accounts as service accounts. Corporate accounts or personal accounts should be for an office user, and not for the production environment. Ensure there are separate accounts for office/corporate use and production/infrastructure environment use.
- Use Microsoft service accounts dedicated to the specific service in question, not the LocalSystem or other privileged services. Don’t add service accounts into any built-in privileged groups.
- Constrained delegation – Microsoft active directory service accounts can be configured to allow access on behalf of a user, through delegation. Configure accounts with constrained delegation so they don’t enjoy access to anything and everything.
- Implement stricter password policies for service accounts, privileged accounts and any non-staff accounts through a separate group policy.
- Regular audits to clean up and revoke/review privileges.
Frequently Asked Questions (FAQs)
Q: What is a directory service account?
A: Directory service accounts are accounts used to manage services in the directory services, similar to those in an Active Directory.
Q: What is an SVC account?
A: SVC is short for service, so svc accounts are the same as service accounts.
Q: What is a managed service account?
A: Managed service accounts or active directory service accounts are a particular type of service accounts that allow you to run a program or application without requiring a password. Their password is set and managed by AD itself and is automatically and periodically rotated and reset.
Q: What are the two types of managed service accounts?
A: There are two types of service accounts; (1) Standalone managed service account (SMSA) and (2) Group managed service account (GMSA). The Standalone Managed Service Account is used to isolate domain user account from crucial applications such as the IIS and eliminate the need of the administrator to manage such account manually. The Group Managed Service Account was introduced in Windows Server 2008 R2 (but not in other operating systems) and is an extension of Standalone Managed Service Accounts. These are managed domain user accounts similar to SMSA but with extended functionality over multiple servers.
Q: What is the purpose of a service account?
A: Service accounts are used to manage multiple services in the network. These various services are usually persistently run and provide local and network resources to a local user.
Q: What is a service account for an application?
A: Usually, service accounts are required by applications running a particular service. For example, Internet Information Services are persistently run to provide web services to the users. To manage the internet information services (IIS) server, a service account is created. Similarly, to run and manage the database services, an SQL service account is created and used.
Q: What is an active directory example?
A: Active directory is an example of a hierarchical database where all the information about user accounts, computer accounts, files, networks, devices etc., is stored and can be retrieved quickly. It makes organisational management easier and simpler.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.