In the digital era, the threat of Ransomware looms more significant than ever. With an ever-growing number of ransomware types and tactics, organizations and individuals must stay vigilant to protect their valuable data. Are you prepared to defend against the different ransomware-type attacks? This blog post unravels the complexities of ransomware types and offers practical strategies to safeguard your data from these malicious threats.
Key Takeaways
- Understand the different types of Ransomware and their mechanics to develop an effective defence.
- Implement comprehensive security measures such as data encryption, secure backups, network activity monitoring, and user education for protection against advanced variants like RaaS.
- Stay vigilant against emerging threats like triple extortion, combining encryption with public shaming tactics.
Deciphering Ransomware Variants: A Comprehensive Guide
Over the years, the ransomware landscape has dramatically evolved, with attackers using diverse tactics for extortion. Comprehending the distinct types of Ransomware is critical to devising a potent defence strategy.
This guide will cover different types of Ransomware, such as crypto, locker, double extortion, doxware, and Ransomware as a Service (RaaS).
Crypto Ransomware Explained
Crypto ransomware is one of the most common attacks, encrypting files on a victim’s computer and demanding a ransom payment for the decryption key. Typically spread via malicious emails, websites, and downloads, CryptoLocker was one of the first crypto-ransomware strains to gain infamy, compromising over 250,000 computer systems within four months and collecting approximately $3 million within nine months.
Although the original CryptoLocker is no longer active, new variants continue to emerge, bypassing some Windows security features.
Locker Ransomware Mechanics
Locker ransomware operates differently from crypto ransomware. It:
- Locks users out of their devices without encrypting any data
- Exploits remote desktop protocol vulnerabilities or launches executables like rkcl.exe to gain access to systems, encrypt files, and terminate processes related to security protection
- Victims often face a pop-up message demanding a ransom payment to restore device access.
Fortunately, the risk level associated with locker ransomware is considered low, as users can often remediate the malware by booting their machines in safe mode and running antivirus software.
The Rise of Double Extortion Ransomware
Double extortion ransomware takes cyber extortion to a new level, combining data theft with encryption to heighten the urgency for victims to pay the ransom. Attackers deny access to data and threaten its eventual public release if the ransom remains unpaid. This type of Ransomware can have severe consequences for businesses and organizations that must protect sensitive data.
One example is Egregor ransomware, which employs double extortion tactics, publicly shaming its victims.
Doxware or leakware
Doxware, also known as leakware, is another sinister cyberattack that steals sensitive data and then threatens to release it publicly unless a ransom is paid. Attackers exploit vulnerabilities or use social engineering techniques to gain unauthorized access to the system and steal the data. Then, perpetrators request remuneration in exchange for not divulging confidential data publicly.
The risk of exfiltration is considerable, and the ramifications for a business can be dire, including reputational damage and possible penalties for violating data privacy laws.
Ransomware as a Service (RaaS)
Ransomware as a Service (RaaS) has emerged as a significant player in the ransomware landscape, providing ransomware tools to cybercriminals who lack the necessary resources to create them independently. The RaaS model allows cybercriminals to:
- Outsource code from an existing provider
- Use it to run criminal ransomware enterprises
- Take a percentage of the ransom payments collected from their victims
RaaS enables affiliates with minimal or no expertise in Ransomware to launch a ransomware attack quickly and cost-effectively.
The increased prevalence of ransomware attacks can be partly attributed to the rise of RaaS, with strains such as DarkSide, Black Basta, and Dharma among the most common.
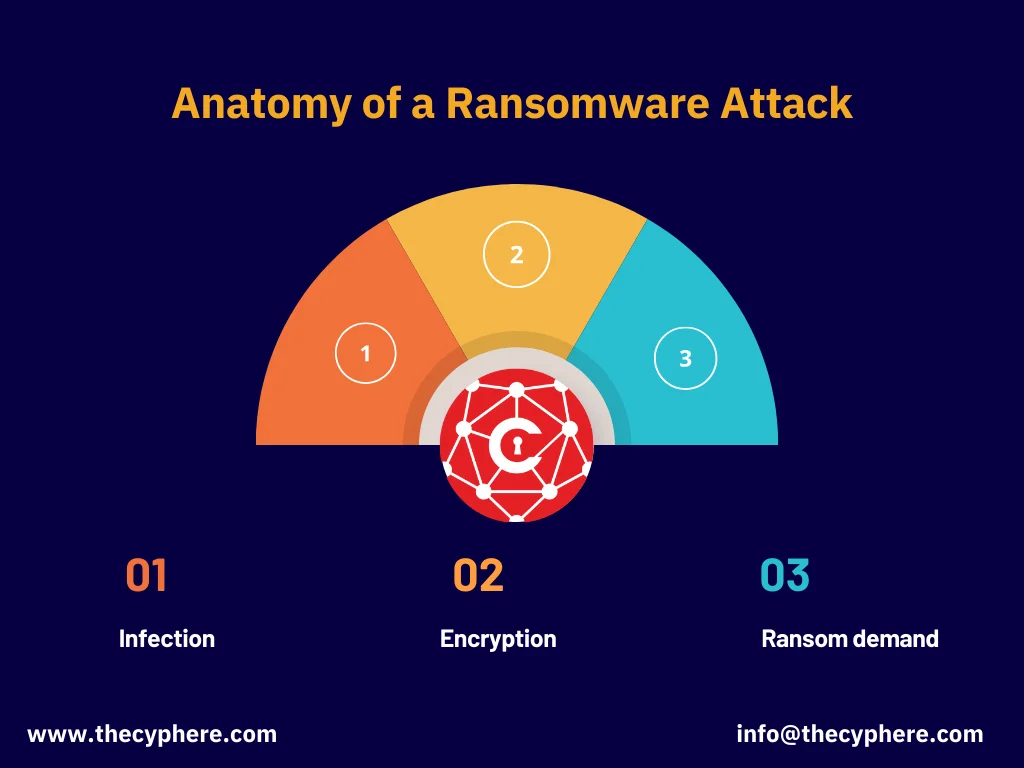
Anatomy of a Ransomware Attack
A ransomware attack unfolds in three stages:
- Infection: Attackers use various methods to infiltrate systems, such as phishing emails, malicious downloads, and software vulnerabilities.
- Encryption: Once the Ransomware has entered the system, it encrypts the victim’s data, making it inaccessible.
- Ransom demand: After encrypting the data, the attackers demand a ransom from the victim in exchange for the decryption key.
The attackers then demand a ransom for the decryption key, typically a percentage of the target company’s annual revenue. Comprehending how a ransomware attack unfolds is key to creating a potent defence strategy and ensuring data safety.
Infection Vectors: How Ransomware Enters Systems
Ransomware infection vectors include phishing emails, malicious downloads, and software vulnerabilities. For instance, Locky ransomware was distributed through phishing emails with Word or Excel attachments containing malicious macros. Ransomware attackers often exploit older vulnerabilities discovered between 2010 and 2019 or target a list of vulnerabilities frequently targeted by ransomware groups.
Malicious downloads are a major factor in ransomware infections, as they are the primary way Ransomware is delivered to a target system. Understanding the methods through which Ransomware infiltrates systems is vital for deploying efficient security actions.
The Encryption Process: Holding Data Hostage
Ransomware combines symmetric and asymmetric encryption techniques to render files inaccessible. For example, AES is a standard symmetric cypher that quickly encrypt user files, with the encryption keys stored on the disk. Upon ransom payment, the attacker supplies the decryption keys to restore access to the encrypted data.
Grasping the encryption process, Ransomware uses is fundamental in formulating a potent defence strategy and preventing your data from becoming a hostage.
The Ransom Demand: Attackers’ Ultimate Goal
The primary objective of ransomware attacks is to extort money from victims, with attackers seeking financial gain. Ransom demands can range from $240 million to as low as $247,000, with the average ransom payment of around $1 million. Factors influencing the ransom amount include the size and importance of the target, the attacker’s assessment of the victim’s capacity to pay, and the overall costs of the attack.
The highest ransom demand in a ransomware attack is $70 million. Comprehending the ransom demand and the ultimate aim of the attackers is instrumental in devising an efficient strategy to tackle ransomware attacks.
Dark web monitoring can help detect if your data is being sold after a ransomware attack.
Identifying the Most Common Ransomware Attacks
There are numerous ransomware strains, each with its unique tactics and methods of distribution. Some of the most prevalent ransomware attacks include:
- Cryptolocker
- Maze
- Ryuk
- WannaCry
- REvil
- Chimera
- Mamba
- Petya
- Cerber
- Jaff
- RobbinHood
- Tycoon
- LockerGoga
- SamSam
- Bad Rabbit
- NotPetya
- Goldeneye
- GandCrab
These attacks have caused significant financial losses, with corporations losing between $50 to $70 million in revenue.
Gaining knowledge about the most prevalent ransomware attacks enables us to fortify our defences against them.
Cryptolocker Ransomware: A Persistent Threat
Cryptolocker is a notorious ransomware that encrypts files and demands a ransom for decryption. It was initially distributed through malicious attachments in spam emails, compromised websites, and counterfeit tracking notices from delivery services such as FedEx and UPS.
Although the original Cryptolocker is no longer active, new variants continue to emerge, bypassing some Windows security features and posing a persistent threat to data security.
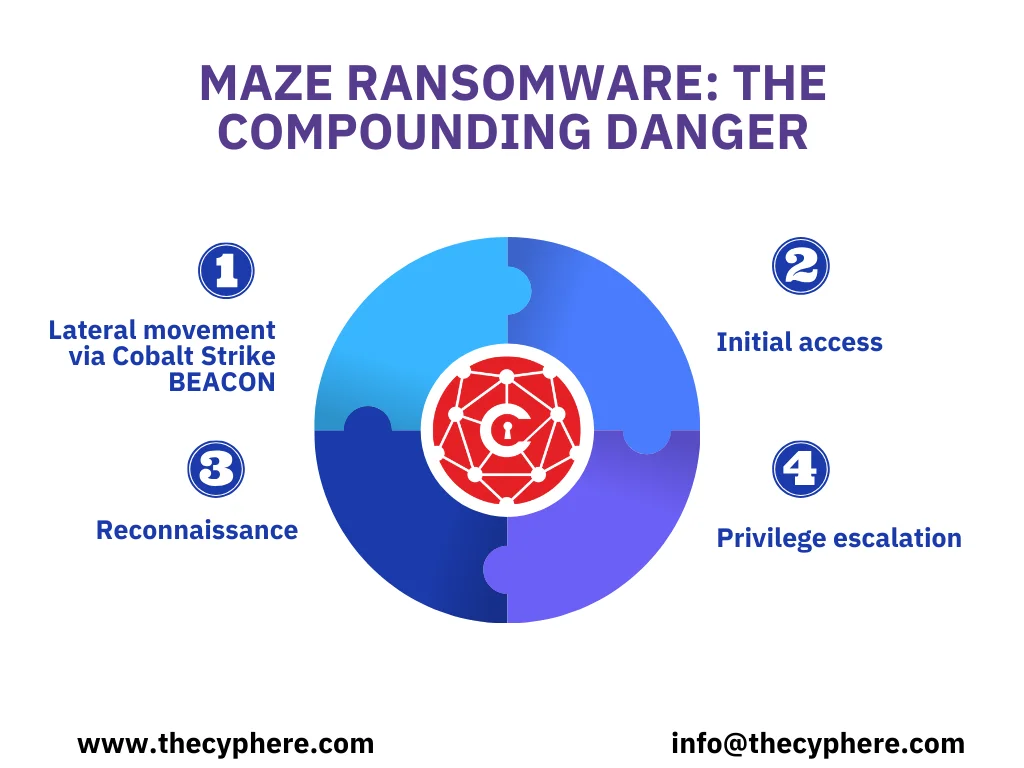
Maze Ransomware: The Compounding Danger
Maze ransomware is a particularly dangerous strain that combines encryption with data theft, increasing the pressure on victims to pay the ransom and avoid public data leaks. Maze ransomware infiltrates systems using advanced techniques such as:
- Lateral movement via Cobalt Strike BEACON
- Initial access
- Reconnaissance
- Privilege escalation
The attackers then threaten to release the stolen data if the ransom is unpaid. Maze ransomware has caused significant financial losses in the healthcare sector, with global repercussions.
Ryuk Ransomware: Targeting High-Value Networks
Ryuk ransomware targets high-value networks, using advanced techniques to infiltrate systems and encrypt data. Ryuk is primarily derived from the well-known Hermes commodity ransomware, which has been accessible on the dark web and hacker forums. Once inside the network, Ryuk attackers map the network, identify and infect high-value targets, and deploy the Ransomware onto those systems.
The concluding stage of a Ryuk attack involves the attackers compromising the environment and extracting valuable data, followed by using locker ransomware to lock the machine and encrypt the files in the background.
Protecting Against Each Type of Ransomware
Regardless of the ransomware type, implementing sturdy security measures is vital in preventing and shielding against ransomware infections.
This section will cover targeted strategies to defend against crypto, locker, and double extortion ransomware attacks.
Security Measures for Crypto Ransomware
To protect against crypto-ransomware attacks, it’s crucial to implement strong encryption, regular backups, and robust security software. Effective encryption methods involve establishing a powerful data encryption strategy, forming a secure backup strategy, and incorporating data encryption as a fundamental element of a comprehensive data protection plan. Regular backups provide a reliable and cost-effective method to restore data without paying the ransom.
Security software like Bitdefender, Kaspersky, Avast, Norton 360, and Trend Micro can help provide ransomware protection and prevent crypto ransomware attacks.
Mitigating Locker Ransomware Risks
To defend against locker ransomware, it’s essential to ensure devices are updated and secure, utilize robust authentication methods, and educate users about potential threats. Maintaining regular application updates on devices can be an effective measure to prevent locker ransomware. Multi-factor authentication (MFA), regular monitoring and patching, a data backup and recovery plan, and network segmentation are the recommended authentication methods for preventing locker ransomware infiltration.
Users should be aware of potential threats concerning locker ransomware, such as phishing attacks, common attack vectors, and unsafe browsing habits.
Preventing Double Extortion Ransomware Breaches
Protecting against double extortion ransomware requires a multifaceted defence strategy, including the following:
- Data encryption: ensures that even if attackers acquire the data, they cannot access or utilize it without the encryption key.
- Secure backups enable organizations to restore their data without paying the ransom demanded by attackers, thereby preventing data loss and minimizing the consequences of a ransomware attack.
- Monitoring network activity for signs of intrusion.
By safeguarding against double extortion ransomware attacks, organizations can:
- Restrict access to data
- Monitor for breaches in the supply chain
- Track relevant data on the Dark Web
- Ensure visibility of data movement
Advanced Ransomware Types and Their Unique Challenges
As the ransomware landscape evolves, the emergence of new and advanced types of Ransomware presents unique challenges for organizations. This section will cover the distinct challenges of triple extortion ransomware and Ransomware as a Service (RaaS).
Triple Extortion Ransomware Tactics
Triple extortion ransomware combines encryption, data theft, and public shaming to extort victims, requiring a multifaceted defence strategy. AvosLocker is an example of a triple extortion ransomware attack, which utilizes DDoS attacks as part of its toolkit.
In a triple extortion attack, the perpetrators attempt to extort money from the initial target organization, as well as anyone whom the release of confidential data could impact. To defend against such attacks, organizations must implement robust security measures that address each aspect of the triple extortion tactic.
Ransomware as a Service: Democratizing Malware
Ransomware as a Service (RaaS) enables cybercriminals with limited resources to launch ransomware attacks, making it crucial for organizations to implement robust security measures.
RaaS provides a business model in which developers can sell or rent their ransomware variants, simplifying the process for anyone to launch a ransomware attack without creating the malware themselves.
This democratization of malware has resulted in a rise in cybercriminals utilizing Ransomware. It underscores the importance of robust security measures to protect against increasingly sophisticated ransomware attacks.
Ransomware as a Service (RaaS) gangs operate like businesses, providing cybercriminals with ransomware tools for a fee or a share of the ransom. This model democratizes cybercrime, enabling even less skilled hackers to launch attacks. Notorious RaaS gangs include REvil and DarkSide, which are known for high-profile attacks.
REvil targeted meat producer JBS, demanding $11 million, while DarkSide was behind the Colonial Pipeline attack, causing significant disruption. These gangs typically use a double extortion model, encrypting victim’s data and threatening to leak it unless a ransom is paid. Negotiations often occur via communication channels set up by the gangs, sometimes involving professional negotiators.
The ransomware code is usually sophisticated, bypassing security measures and often includes updates and customer support, mirroring legitimate software services.
Summary
In conclusion, understanding the various types of Ransomware and their unique tactics is crucial for developing an effective defence strategy. Organizations can protect their valuable data from the ever-evolving ransom landscape by implementing robust security measures, such as solid encryption, regular backups, and comprehensive security software. Stay vigilant and proactive in the fight against Ransomware, and safeguard your data from these malicious cyber threats.
Frequently Asked Questions
What are the three main types of Ransomware?
The three main types of Ransomware are Crypto Ransomware or Encryptors, Lockers, and Scareware.
What is the most common type of ransom attack?
Crypto ransomware is the most common type of ransom attack, using encryption to block access to files on a computer and any related network or cloud drives. Victims are unable to access their data due to encryption.
What is a ransom attack?
Ransomware is a malicious attack that seeks to deny access to files by encrypting them and demanding payment to decrypt the key. Organizations are often forced to pay a ransom to regain control of their files.
What is the difference between crypto-ransomware and locker ransomware?
Ransomware encrypts files and demands a ransom payment for the decryption key. In contrast, locker ransomware locks users out of their devices and requires a ransom payment to restore access without encrypting any data.
How does double extortion ransomware increase pressure on victims?
Double extortion ransomware increases pressure on victims by threatening to release stolen data publicly if the ransom is not paid, combining data theft with encryption.