In an age where technology permeates every aspect of our lives, businesses are faced with an ever-growing array of cyber threats and cyber security risks for businesses. As cyber criminals become increasingly sophisticated and relentless, companies must stay informed and prepared to protect themselves from potential attacks.
This article will provide an overview of the various types of cyber threats, their consequences, and the latest emerging risks, such as generative AI and LLMs. It highlights the importance of a multi-faceted approach to cybersecurity that includes people, processes, and technology controls.
Key Takeaways
- Understanding and preparing for cyber threats is essential to protect businesses from unauthorized access or unlawful use.
- Cybercriminals pose a significant threat through malicious activities, resulting in financial losses, reputational damage, and operational disruption.
- Businesses must take proactive measures, including risk assessments and management plans, to guard against emerging risks such as generative AI & LLMs.
Understanding Cybersecurity Threats
Cyber security safeguards networks, data, and devices from unauthorized access or unlawful use, ensuring business infrastructure security. Cybersecurity risks rise significantly as organizations continue to embrace digital transformation, new technologies, and evolving business processes. Protecting your business adequately requires staying updated on the most common cybersecurity threats, such as:
- malware attacks
- viruses
- phishing attacks
- ransomware
Familiarizing oneself with common threats, allocating resources to tackle and enhance cybersecurity, utilizing solid passwords, and formulating a cybersecurity plan are some of the best cybersecurity practices for businesses. Understanding the diverse types of cyber threats and their consequences enables companies to devise strategies to protect their sensitive data and sustain operations amidst constantly changing risks.
Cyber Attacks and Their Consequences
Cyber attacks can have severe repercussions for businesses of all sizes, resulting in financial loss, damage to reputation, and regulatory sanctions. These attacks can take various forms, such as social engineering, ransomware, phishing and smishing attacks, and insider threats, all aimed at gaining access to sensitive information or systems.
Implementing security software, regular data backups, and employee education on safe browsing habits are necessary for protecting small and medium businesses. Multi-factor authentication and business password management technologies can further fortify defences against cyber attacks.
The ramifications of cyber attacks are far-reaching, affecting monetary assets, data integrity, and public perception of organizations. To mitigate these risks, businesses should collaborate with an infrastructure security agency and experts, ensuring that their security measures are up-to-date, comprehensive, and capable of withstanding the ever-changing tactics employed by cybercriminals.
The Role of Cyber Criminals
Cybercriminals play a significant role in cybersecurity threats, operating through online forums and offering illicit goods and services such as tools for launching cyber attacks. They are also increasingly using AI-based tools to conduct more sophisticated attacks. In addition, state-sponsored cyber threat actors engage in espionage activities against governments, organizations, and individuals.
Driven primarily by financial gain, cyber criminals employ various tactics, including malware, ransomware, skimming, phishing, and password attacks. The impact of their activities on businesses can be substantial, leading to data breaches, financial losses, detriment to reputation, and disruption of operations.
As an example, you can see how dating apps were riddled with security privacy concerns, and even some of the issues when exploited led to data breaches affecting millions of individuals.
Staying updated on the tactics and motivations of cyber criminals allows businesses to prepare more effectively for emerging threats and strengthen their overall cybersecurity posture.
Emerging Cybersecurity Risks: Generative AI and LLMs
Generative AI and LLMs (Logic-Level Machines) are revolutionizing cybersecurity, augmenting real-time detection and prevention of threats such as malware and phishing. However, these technologies also present new risks, including the potential to bypass security measures, launch sophisticated attacks, and even generate new malware.
Businesses must acknowledge the potential dangers associated with LLMs and generative AI and proactively mitigate them, including implementing multi-factor authentication, monitoring for unusual activity, and implementing regular system patches.
Understanding Generative AI
Generative AI is a type of artificial intelligence that can generate new content from existing data, creating realistic:
- images
- videos
- audio
- text
That can be used for malicious purposes. One of the most nefarious applications of generative AI is the creation of deepfakes, artificial videos or audio files designed to appear genuine.
The implications of deepfakes on cybersecurity are significant, as they can be used to propagate disinformation, generate false news, and damage individuals or entities. Businesses must remain alert to protect themselves from the dangers of deep fakes, including implementing strong authentication measures, monitoring suspicious activity, and educating employees on the risks associated with deep fakes.
Preparing for LLM-Driven Threats
LLM-driven threats refer to those generated or facilitated by applying LLM (Leveraged Learning Machines) technology, a form of artificial intelligence that leverages machine learning algorithms to detect patterns and create predictions. While LLMs can detect and respond to threats more quickly than traditional methods, they pose new risks, requiring businesses to stay up-to-date on LLM technology and deploy comprehensive data security measures.
Businesses should take the following steps to mitigate LLM-driven threats:

- Regularly evaluate and predict potential risks
- Set up advanced threat detection systems
- Provide regular training
- Operate AI chatbot tools securely
- Inform users about the risks and limitations
By staying abreast of cybersecurity threats and developments, businesses can better prepare for and counter LLM-driven threats.
Most common security risks for businesses that lead to data breaches
Ransomware, phishing, unpatched systems, and third-party attacks are among businesses’ most common security risks. Malware, a form of cyber attack that performs unauthorized activities on the victim’s system, poses a significant threat to companies, with phishing attacks and social engineering techniques being the most significant risks regarding cybersecurity. Organizations must be alert to these risks and take suitable measures to secure their sensitive data and systems.
Indications that a computer may be infected with a virus include:
- An increase in pop-up windows
- Unauthorized modification of the account’s password
- Deletion of files
- A decrease in network speed
Familiarity with the most common security risks enables businesses to devise strategies to protect their critical data and sustain operations amidst constantly changing cyber threats.
Ransomware
Ransomware attacks have evolved with the rise of ransomware-as-a-service and connections to organized crime syndicates, making them a significant threat to businesses. Ransomware is a type of malicious software that encrypts valuable data and demands payment to restore access to the system. Typically delivered via phishing emails, ransomware attacks can have severe consequences for businesses, including financial loss, damage to reputation, and regulatory sanctions.
To protect against ransomware attacks, businesses should employ robust security measures, including multi-factor authentication, regular data backups, and employee training on safe browsing habits. Keeping up-to-date with the latest ransomware trends and implementing thorough security measures enables businesses to shield themselves more effectively from the catastrophic effects of ransomware attacks.
Phishing, Smishing and Vishing
Phishing, smishing, and vishing attacks are attempts to deceive individuals into providing confidential information via email, text, or phone calls. These attacks are prevalent and can lead to data breaches and financial loss if not adequately addressed.
When connected to an organizational network, mobile devices can be targeted in smishing attacks, potentially giving attackers access to confidential information and leading to data breaches.
To protect themselves from phishing and smishing attacks, businesses should:
- Seek professional cybersecurity threat assessment to develop a tailored solution that meets their specific requirements
- Stay updated on the latest trends in phishing, smishing, and vishing
- Implement thorough security measures
By doing so, businesses can protect their sensitive data, including customer data, more effectively and sustain operations amidst constantly changing cyber threats.
Unpatched Systems and Devices
Unpatched systems and devices, including VPNs, firewalls, and gateways, have been heavily exploited, especially during and after COVID-19. A risk-focused approach to patching is necessary to prioritize the most vulnerable assets. Unpatched systems and devices have not been updated with the most recent security patches and updates, leaving them open to potential cyber-attacks and exploitation.
To protect their sensitive data and systems, businesses should:
- Identify which assets are most at risk and what risks are present
- Prioritize those assets over others
- Keep up-to-date with the latest trends in unpatched systems and devices
- Implement thorough security measures
By doing so, businesses can protect their critical data more effectively and maintain operations amidst constantly evolving cyber threats.
Cyber Essentials Plus Certification
- Protect sensitive data, protect your business
- Improve eligibility for new opportunities across regulated industries and public sector.
Suggested Read: Cyber Essentials Plus Checklist
Third-party and supply-chain attacks
Third-party and supply chain attacks, such as the SolarWinds incident, can significantly impact businesses and highlight the importance of securing the entire supply chain. These attacks target weaknesses in the systems or software of third-party providers or suppliers that companies depend on. The repercussions of these attacks can include:
- Data breaches
- Malware infections
- Business disruption
- Reputational damage
- Regulatory and legal consequences
To mitigate these risks, businesses should:
- Collaborate with infrastructure security agencies and experts
- Ensure that their security measures are up-to-date, comprehensive, and capable of withstanding the ever-changing tactics employed by cybercriminals.
- Stay updated on the latest trends in third-party and supply-chain attacks
- Implement comprehensive security measures
By following these steps to protect your business, small businesses can access more effective shields against the devastating effects of these attacks.
Excessive reliance on security products adds to cyber threats.
While security products are critical in safeguarding businesses from cyber threats, excessive reliance on them alone is insufficient for a comprehensive cybersecurity strategy. Combining people, processes, and technology controls is necessary to improve cybersecurity maturity. Over-reliance on security products can lead to a false sense of security, complacency, and a lack of proactive measures to identify and mitigate potential threats.
Adopting a balanced approach considering people, processes, and technology can help businesses strengthen their cybersecurity posture and protect their sensitive data and systems. This includes:
- Conducting regular risk assessments
- Implementing robust authentication measures
- Monitoring for suspicious activity
- Training employees to recognize and respond to potential cyber “threats” s
Cyber attacks are not a matter of if, but when. Be prepared.
Box-ticking approach to penetration tests is long gone. We help you identify, analyse and remediate vulnerabilities so you don’t see the same pentest report next time.
Cybersecurity workforce shortage
The cybersecurity workforce shortage poses a risk for businesses that rely solely on IT service providers for security without internal accountability and specialized expertise. The global cybersecurity workforce has reached its highest-ever levels, with an estimated 4.7 million professionals. However, there is still a shortage of skilled cybersecurity professionals, with a global workforce gap of almost 3.4 million. This deficiency leads to high burnout and attrition rates among cybersecurity staff and an increased risk of cyber attacks due to the lack of qualified professionals.
To address the cybersecurity workforce shortage, businesses can:
- Invest in training and development programs for existing staff
- Recruit and hire new cybersecurity professionals
- Consider outsourcing some of their cybersecurity needs to third-party providers
By taking these measures, businesses can ensure they have the specialized expertise and internal accountability necessary to protect their sensitive data and systems from cyber threats.
Assessing and Managing Cybersecurity Risks
Assessing and managing cybersecurity risks is essential to a comprehensive cybersecurity strategy. By conducting risk assessments, implementing risk management plans, and continuously monitoring and updating security measures, businesses can better protect themselves from the ever-evolving landscape of cyber threats.
Conducting a Cybersecurity Risk Assessment
A cybersecurity risk assessment helps businesses:
- Identify vulnerabilities
- Prioritize organization’sforts
- Analyze the organization’s current security posture
- Identifyorganization’seats
- Evaluate the organization’s capacity to respond to and reduce those threats.
Cyphere offers affordable, high-quality assessments with risk remediation support, focusing on service quality in their assessments and providing risk remediation assistance to help businesses address their cybersecurity challenges.
Conducting a cybersecurity risk assessment allows businesses to understand their security landscape better, pinpoint weaknesses, and plan remediation efforts to strengthen their overall cybersecurity posture. Utilizing services like Cyphere can provide cost-effective, superior quality assessments with risk remediation assistance, ensuring businesses are well-equipped to address their cybersecurity challenges.
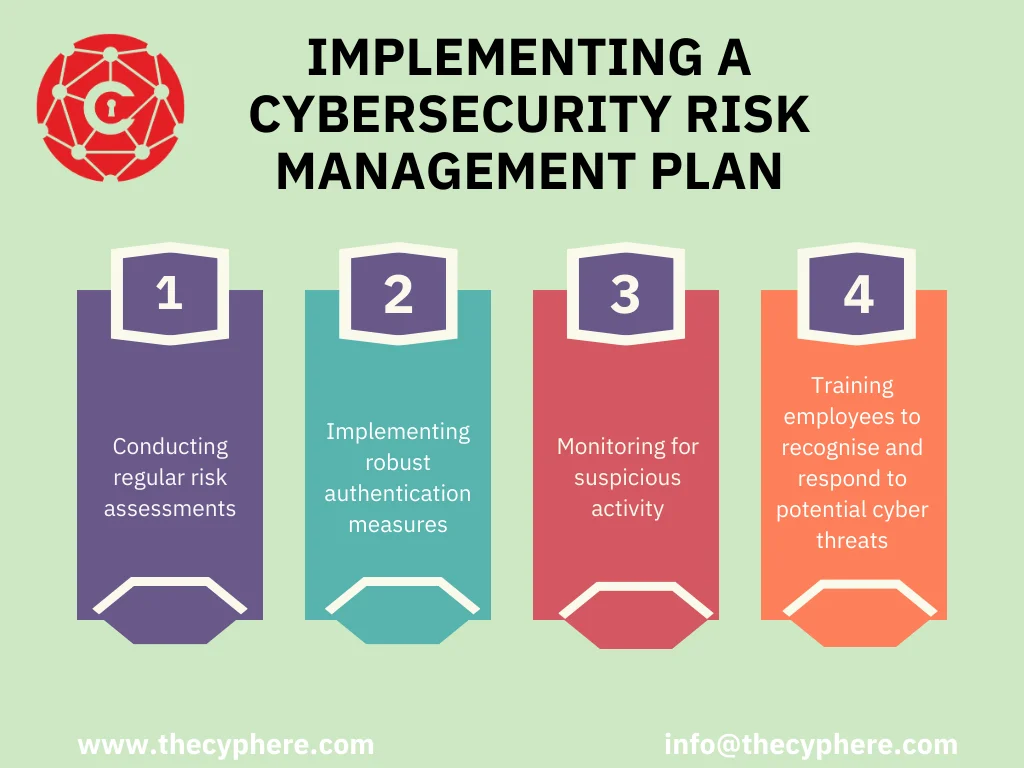
Implementing a Cybersecurity Risk Management Plan
Implementing a cybersecurity risk management plan involves a combination of prevention, detection, and response measures to protect businesses from cyber threats. Prevention strategies should focus on identifying and reducing potential threats before they occur, while detection strategies should monitor user accounts and activities to spot suspicious behaviour. Response strategies should focus on containing the threat, evaluating and restoring any damage caused, and implementing measures to prevent similar threats in the future.
Adopting a holistic approach towards cybersecurity risk management can help businesses protect their sensitive data and systems from cyber threats. This includes:
- Conducting regular risk assessments
- Implementing robust authentication measures
- Monitoring for suspicious activity
- Training employees to recognize and respond to potential cyber threats.
Summary
In conclusion, businesses face many cyber threats that can have severe consequences if not adequately addressed. Companies can better protect their sensitive data and systems by staying informed about the latest cyber threats, emerging risks, and best practices. Adopting a comprehensive approach to cybersecurity that includes people, processes, and technology controls, conducting regular risk assessments, and implementing robust cybersecurity risk management plans are all crucial steps in safeguarding businesses from the ever-evolving landscape of cyber threats.
Frequently Asked Questions
What are cybersecurity risks for business?
Cybersecurity risks for businesses include phishing, ransomware, malware, third-party risks, internal risks, and compliance failures. These attacks are often done through emails or text messages that look legitimate and can be devastating for small businesses. Criminals also look for access to information and data on your business, employees and customers through theft or unauthorized access to hardware, computers and mobile devices and infecting computers with malware.
What cybersecurity challenges do businesses face?
Businesses face many cybersecurity challenges, including hackers breaking into networks and phishing scams gaining access to confidential data. With the increasing prevalence of these threats, companies need to take more significant steps to protect their information.
What measures can businesses take to protect themselves from ransomware attacks?
Businesses can protect themselves from ransomware attacks by implementing multi-factor authentication, regularly backing up data, and training employees in safe browsing practices.
What are the potential dangers of generative AI?
Generative AI poses a severe risk as it can be used to create malicious content, such as deepfakes and phishing campaigns, that can harm individuals and organizations.
How can businesses address the cybersecurity workforce shortage?
Businesses can address the cybersecurity workforce shortage by investing in existing staff, recruiting new specialists, and outsourcing when necessary.