Imagine the chaos and financial losses your organisation could face during a ransomware attack. Now, imagine having the foresight and preparation to minimise those damages effectively. Ransomware tabletop exercises offer a unique opportunity to test your organisation’s cyber resilience and improve defences against rapidly evolving cyber threats. Get ready to unlock the secrets of a successful ransomware tabletop exercise and elevate your organisation’s security posture.
Key Points
-
-
Ransomware tabletop exercises help organisations prepare for and respond to ransomware threats.
-
-
-
Pre-exercise preparation, in-exercise collaboration, and post-exercise debriefing by an information security expert are essential components of a successful exercise.
-
-
-
Integrating compliance with relevant regulations and proactive defence measures into the exercise is necessary for effective preparedness and cyber resilience.
-
What is a ransomware tabletop exercise?
A ransomware tabletop exercise is a simulated cyber-attack scenario designed to assist organisations in preparing and responding to ransomware threats. Participating in these tabletop exercise scenarios enables technical and administrative personnel to enhance their knowledge of cyber threats and their roles in responding to ransomware incidents. Representatives from all departments and business levels should be included in a ransomware tabletop exercise for optimal results, as it helps prepare the organisation for various cyber threats, similar to how organisations prepare for natural disasters.
A typical ransomware tabletop exercise includes:
-
-
Stakeholders and representatives from departments such as security, IT, legal, human resources, and public relations
-
-
-
An information security professional as a facilitator
-
-
-
Discussion-based tabletop exercises to replicate a ransomware attack scenario
-
-
-
Testing response capabilities
-
-
-
Identifying areas for improvement
-
Ransomware readiness assessment
A ransomware readiness assessment is a self-assessment process based on a tiered set of practices to evaluate an organisation’s preparedness to defend against ransomware attacks, ultimately improving cyber resilience. The effectiveness of a ransomware readiness assessment can be determined by assessing factors such as:
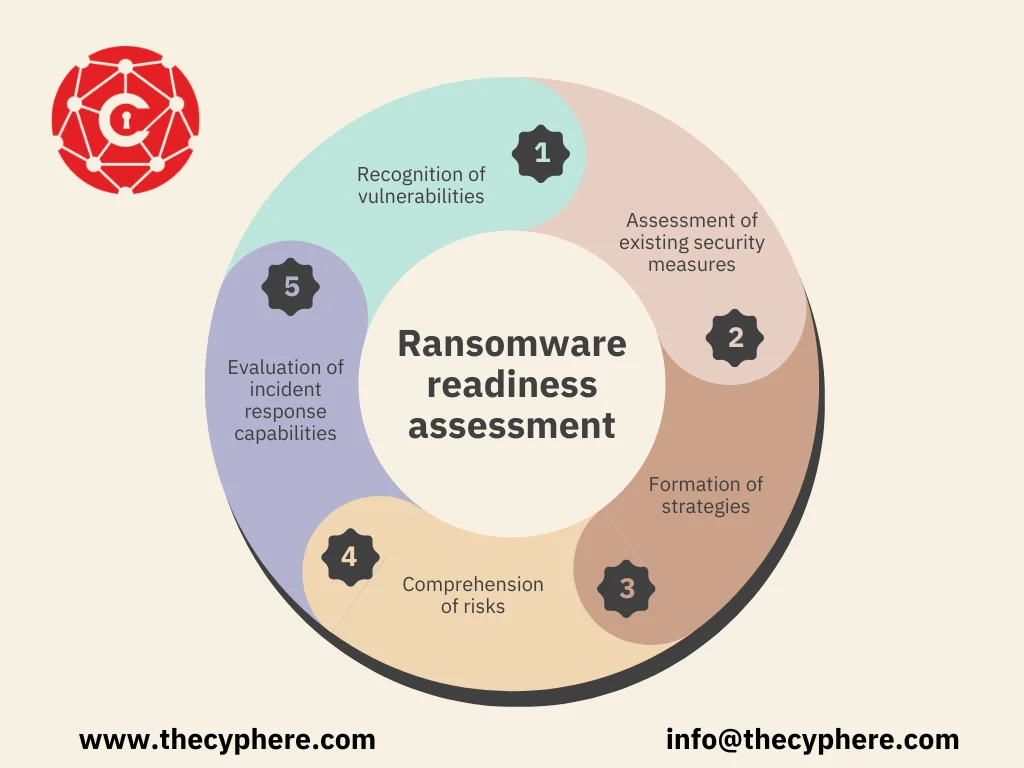
-
-
Recognition of vulnerabilities
-
-
-
Assessment of existing security measures
-
-
-
Formation of strategies
-
-
-
Comprehension of risks
-
-
-
Evaluation of incident response capabilities
-
Conducting a ransomware readiness assessment at least once a year is advisable; however, the frequency may vary depending on the organisation’s risk profile and industry standards.
We conduct a ransomware readiness assessment to assess your preparedness of people, processes and technology. Get in touch to know more.
Organisations in high-risk sectors, including those prone to natural disasters or those that have recently suffered security incidents, such as physical security breaches, might need to conduct assessments regularly to maintain readiness and ensure proper implementation of security protocols.
Why conduct a ransomware readiness assessment?
A ransomware readiness assessment is beneficial in identifying potential vulnerabilities and enhancing defences against ransomware attacks, preparing organisations to respond to such attacks effectively. Organisations can recognise potential weaknesses by conducting a ransomware readiness assessment, evaluating incident response procedures, and minimising disruption and downtime. These assessments encourage participants to actively improve their organisation’s cybersecurity defences.
A ransomware readiness assessment presents multiple benefits for enhancing cybersecurity defences, including:
-
-
Identifying vulnerabilities and weaknesses in security posture
-
-
-
Evaluating incident response capabilities
-
-
-
Pinpointing areas at the highest risk for attack
-
Organisations can mitigate the risk of a ransomware incident by implementing necessary defences and policies based on the assessment.
Essential Components for a Successful Ransomware Tabletop Exercise
Three key components to guarantee a successful ransomware tabletop exercise should be considered: pre-exercise preparation, in-exercise collaboration, and post-exercise debrief. An information security expert, preferably an external consultant and facilitator, is the most suitable choice to facilitate the exercise, as they have extensive knowledge of cyber threats and can guide the participants effectively.
The facilitator should prompt participants to react to the attack scenario as though it were a real-life occurrence, interjecting pertinent points, providing examples of the steps that should be taken during each response phase, and asking relevant questions to guide the conversations towards the essential aspects of ransomware readiness. Ransomware tabletop exercises are crucial for improving an organisation’s preparedness for cyber threats.
Cyber Essentials Plus Certification
- Protect sensitive data, protect your business
- Improve eligibility for new opportunities across regulated industries and public sector.
Suggested Read: Cyber Essentials Plus Checklist
Pre-Exercise Preparation
Before the exercise begins, it’s essential to confirm that all participants know their roles and thoroughly understand the incident response plan. Participants in a ransomware tabletop exercise typically assume roles such as:
-
-
Stakeholders
-
-
-
Representatives from security, IT, legal, human resources, and public relations
-
-
-
Incident commander
-
-
-
Technical responders
-
-
-
Legal advisors
-
-
-
Information security experts
-
The incident response plan is an organisation’s framework or playbook to respond to a security incident. It contains the steps and procedures that participants should follow should an incident occur, including forming an incident response team, defining responsibilities, and establishing policies. Ensuring participants are familiar with the incident response plan is crucial in guaranteeing a seamless and efficient exercise.
In-Exercise Collaboration
During the ransomware tabletop exercise, it’s essential to cultivate a collaborative environment that encourages constructive and professional conversation among participants. Providing the exercise scenario to all participants simultaneously ensures everyone has the same information and can collaborate efficiently. An independent facilitator plays a crucial role in setting the appropriate guidelines and atmosphere for the exercise.
Developing an atmosphere of accountability and learning, where everyone is comfortable contributing their thoughts and differing opinions are welcomed, is of utmost importance. A stress-free, open, and professional environment enables participants to work together effectively in responding to the ransomware attack scenario and identifying areas for improvement.
Realistic Scenarios and Scenario Variations
Any successful tabletop exercise includes realistic situations. For instance, a believable situation could entail a ransomware attack originating from a phishing email, leading to the encryption of confidential client data. The situation should evolve, covering the breach’s discovery, reporting to law enforcement, a ransom demand, system restoration from backups, and the decision-making process regarding the ransom’s feasibility.
Before the exercise, the leaders should devise several credible ‘curveballs’ to introduce during the exercise. For example, the ransom demand could be exorbitantly high in one situation. In a different situation, a secondary ransomware attack, deploying another variant, could occur within a day. These diversifications allow teams to adapt to unforeseen conditions and evaluate various incident response plan elements.
Post-Exercise Debrief
The post-exercise debrief entails reflecting on the exercise, preparing an after-action report, and integrating the findings into upcoming plans. If an external party or facilitator is utilised for the exercise, they will be responsible for taking detailed notes and providing a report afterwards.
Post-exercise analysis, also known as post-tabletop analysis, is essential to analyse the outcomes of the tabletop exercise, compile an after-action report or summary memo, and potentially survey or obtain participants’ feedback. An after-action report intends to evaluate the exercise and generate a report summarising insights and critical analysis of participants’ responses and conversations, helping organisations identify areas for improvement.
Cyber attacks are not a matter of if, but when. Be prepared.
Box-ticking approach to penetration tests is long gone. We help you identify, analyse and remediate vulnerabilities so you don’t see the same pentest report next time.
Integrating Ransomware Preparedness into the Exercise
When incorporating ransomware preparedness into the exercise, it’s essential to consider factors like compliance with relevant regulations and promoting proactive defence measures. Addressing compliance is critical for effective ransomware preparedness during a workout, ensuring that the organisation adheres to regulatory requirements and guidelines related to cybersecurity and data protection.
Proactive defence measures can be integrated into ransomware preparedness exercises by implementing critical controls identified in the ransomware preparedness assessment, such as regular and secure backups, updating and patching systems, and implementing advanced threat protection tools. These measures help strengthen defences against ransomware attacks and improve the organisation’s cyber resilience.
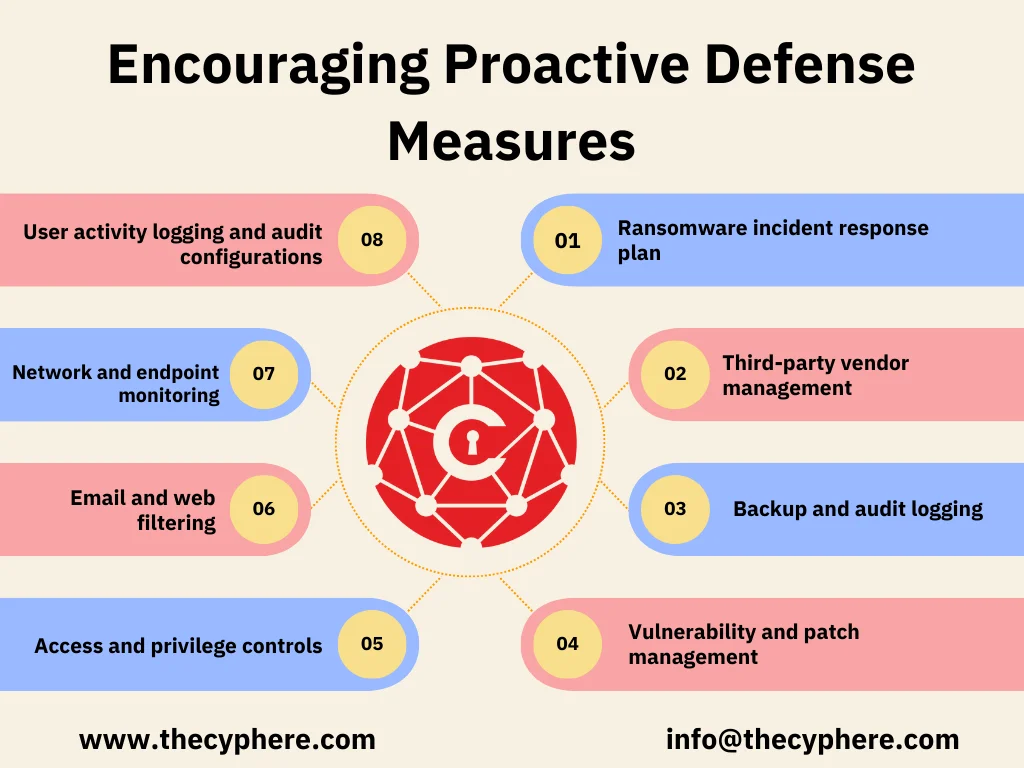
Encouraging Proactive Defense Measures
Implementing critical controls from a ransomware preparedness assessment is an effective way to bolster defences against ransomware attacks. Some of these vital controls include:
-
-
Ransomware incident response plan
-
-
-
Third-party vendor management
-
-
-
Backup and audit logging
-
-
-
Vulnerability and patch management
-
-
-
Access and privilege controls
-
-
-
Email and web filtering
-
-
-
Network and endpoint monitoring
-
-
-
User activity logging and audit configurations
-
By integrating these critical controls into ransomware preparedness exercises, organisations can proactively defend against attacks and improve their overall security posture. These proactive defence measures help organisations stay one step ahead of cybercriminals and protect valuable data and assets.
14criticaly controls of the ransomware readiness plan
To effectively combat ransomware threats, organisations should implement the following critical controls:
-
- Firewall configuration
-
- Remote access controls
-
- Email and web filtering
-
- Endpoint protection
-
- Employee training on security best practices
-
- Vulnerability management
-
- Regular data backups
-
- Network segmentation
-
- Incident response plan
-
- User access controls
-
- Patch management
-
- Security monitoring and logging
-
- Encryption of sensitive data
-
- Regular security assessments and audits
These controls help organisations protect their networks from malicious traffic, unauthorised access, and other potential threats while facilitating rapid detection and response to security incidents.
Tailoring the Experience to Your Business Continuity Plans
For optimal results, tailor the ransomware tabletop exercise to suit your organisation’s unique needs and vulnerabilities. By identifying critical business functions and developing response strategies, you can ensure that the exercise is tailored to your business continuity plans and effectively tests your organisation’s preparedness for ransomware attacks.
A risk analysis can be conducted to identify the most critical parts of the business for the exercise, and the scenarios can be tailored to the company by customising them based on events that are critical for the particular organisation. This ensures that the ransomware tabletop exercise focuses on your organisation’s specific needs and vulnerabilities, making it more relevant and effective.
Identifying Critical Business Functions
Identifying critical departments and groups for the ransomware tabletop exercise is necessary. Involving the following ensures a comprehensive representation of your organisation’s essential functions of business:
-
-
Senior leadership
-
-
-
Legal department personnel
-
-
-
IT professionals
-
-
-
Communications coordinators
-
-
-
Human resources representatives
-
-
-
Facilities employees
-
-
-
Technical and administrative staff
-
Recognising vital business functions guarantees that the ransomware tabletop exercise is customised to the organisation’s requirements and business continuity plans. By involving key stakeholders from various departments, the exercise becomes more relevant and effective in testing your organisation’s preparedness for ransomware attacks.
Developing Response Strategies
It’s critical for effective ransomware preparedness to develop response strategies that are tailored to the organisation’s specific needs and vulnerabilities. Some techniques that may be employed to respond to a ransomware attack include:
-
-
Developing a plan to restore data from backups
-
-
-
Implementing a system to detect and respond to ransomware attacks
-
-
-
Training employees on how to recognise and respond to ransomware threats
-
By customising response plans based on the organisation’s unique needs and vulnerabilities, you can ensure your organisation is better prepared to handle ransomware attacks and minimise potential damages and disruptions. Developing these strategies is essential for maintaining business continuity in the face of evolving cyber threats.
Summary
In conclusion, ransomware tabletop exercises are crucial in preparing organisations for the ever-present threat of ransomware attacks. By understanding the importance of ransomware tabletop exercises, conducting ransomware readiness assessments, focusing on essential components, integrating preparedness assessments into the exercise, and tailoring the experience to your business continuity plans, organisations can bolster their defences against ransomware attacks and improve their overall cyber resilience.
Don’t wait for a ransomware attack to weaken your organisation. Leverage the power of ransomware tabletop exercises to identify potential vulnerabilities, enhance defences, and ensure business continuity in the face of these relentless cyber threats.
Schedule a conversation with our security team to discuss your security objectives and avail free advice.
Frequently Asked Questions
What is a ransomware tabletop exercise?
A ransomware tabletop exercise is a practical framework used to help organisations prepare for and understand their roles in incident response.
What is a tabletop incident response exercise?
Tabletop incident response exercises involve personnel with roles and responsibilities in an IT plan discussing their roles during an emergency in a classroom setting or through breakout groups. This helps to validate the content of the plan.
What is a tabletop exercise in disaster recovery?
Tabletop exercises are an effective tool for preparing disaster recovery teams for emergencies, allowing personnel to discuss potential scenarios in a non-threatening environment and become familiar with their assigned roles and responsibilities.
What is the tabletop exercise?
A tabletop exercise is a simulated activity where key personnel assigned emergency management roles discuss various scenarios in a non-threatening environment. Participants are expected to engage and contribute to the conversation.
How often should a ransomware readiness assessment be conducted?
Ransomware readiness assessments should be conducted annually to ensure compliance with industry standards and best practices.