
Over the last few years, the rise in data breaches involving personally identifiable information (PII) has resulted in the loss of millions of records. These breaches target big corporate names, but most victims are small businesses.
Accessing PII without authorisation poses a significant risk to both individuals and the company. Individual harms may include identity theft, fraud, or blackmail. At the same time, a company may suffer data breach harms such as a loss of public trust, legal responsibility, or remediation fines. Data breaches are becoming more common, and the headlines are often filled with stories of large companies losing customer data. But data breaches aren’t just a problem for big businesses – they can happen to anyone.
Believe it or not, during our internal network penetration tests, our security consultants often find sensitive information that is stored unprotected on the file servers. This includes scanned copies of credit cards, passports, third-party application logins to payment systems, analytics and other web marketing and business portals. This is one of the top risks identified under insecure information storage practices.
Because every business, regardless of its size, may be subject to a combination of PII laws, regulations, and other mandates related to securing PII, it should take the approach of data security and privacy to protect the PII it employs in its environment.
A data governance platform is necessary to be in place before you begin to secure the data. This blog offers practical recommendations for recognising and protecting PII, including sensitive company data, to avoid a dangerous situation such as data breach or theft.
The blog also proposes measures that may provide acceptable levels of protection. It provides some examples of how to establish methods to protect the usage of proper PII access and storage.
What is PII?
PII stands for Personally Identifiable Information, which refers to the personal data in terms of any identifier used to identify or trace an individual’s identity, such as name, address, date of birth, driver’s license, and sensitive customer information.
The PII can also refer to any additional information related to or linkable to an individual, such as medical records, educational, financial, employment and other sensitive data.
Note that there’s no definitive list of what is or isn’t personal data. Hence, it all comes down to correctly interpreting the definition of the European Union’s General Data Protection Regulation:
“Personal data means any information relating to an identified or identifiable natural person (‘data subject’).”
If you can distinguish an individual from others, that person is ‘identified’ or ‘identifiable’.
PII examples
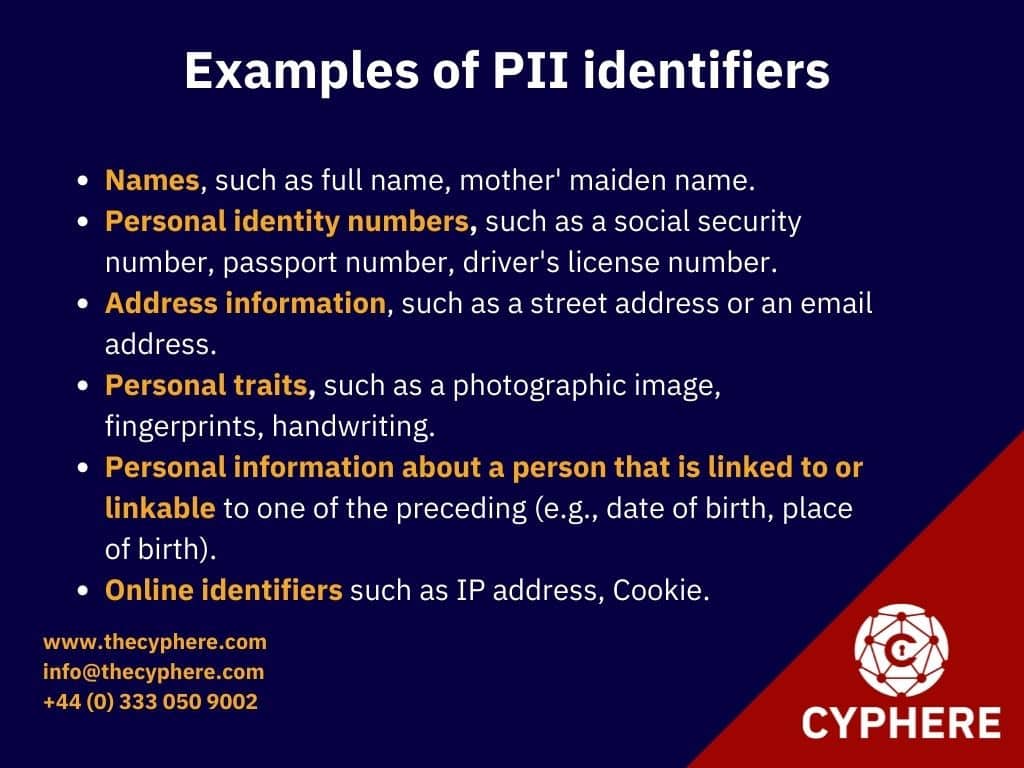
Examples of PII identifiers include, but are not limited to:
- Names, such as full name, mother’ maiden name, father’s name, or an alias.
- Personal identity numbers include a social security number, passport number, driver’s license number, taxpayer identification number, and financial institutions account or credit card number.
- Address information, such as a street address or an email address.
- Personal traits, such as a photographic image (particularly of the face or other distinguishing feature), fingerprints, handwriting, or other biometric data (e.g., retina scan, voice signature, facial geometry).
- Personal information about a person linked to or linkable to one of the preceding (e.g., date of birth, place of birth, race, religion, weight, activities, geographical indicators, employment information, medical information, education information, financial information).
- Online identifiers include IP address, Cookie information, MAC address, RFID tag, advertising IDs, pixel tags, account handles, and device fingerprints.
Similarly, health-related information known as PHI (Protected Health Information) is an important element of why healthcare and social care organisations need to pay attention for the Data Protection Act 2018.
What is sensitive PII?
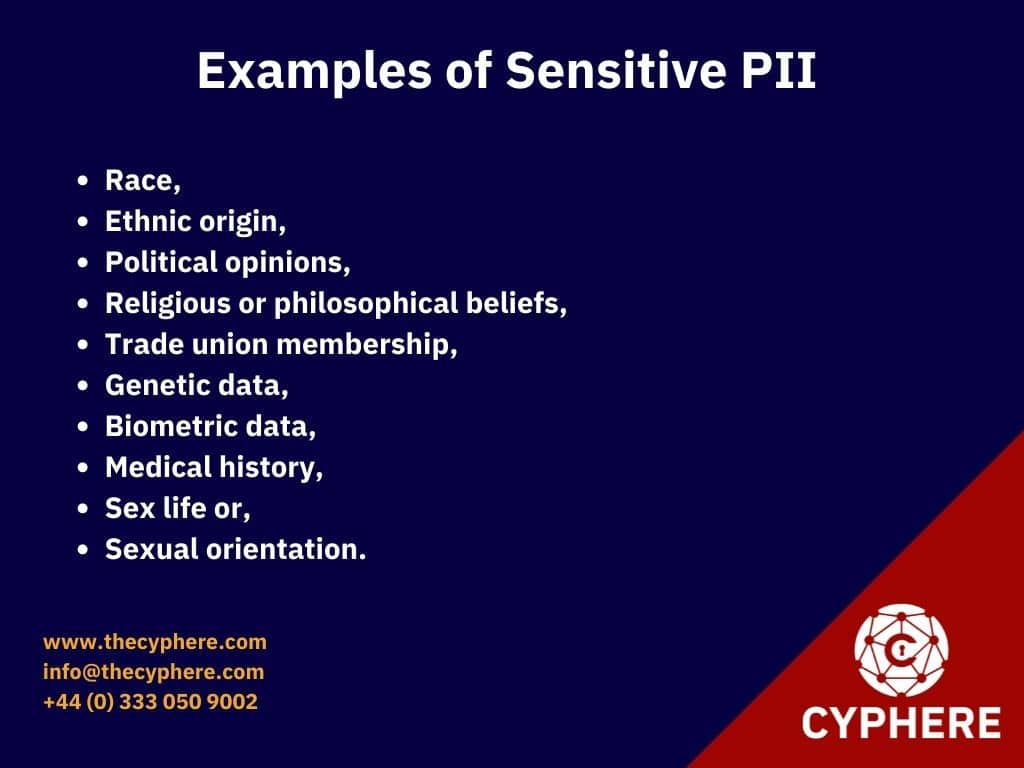
Some of the PII can be more sensitive and therefore requires a higher level of protection. The GDPR refers to this category as sensitive data. Learn more about the 8 principles of the Data Protection Act 2018 & GDPR.
Sensitive PII requires more safeguards than non-sensitive PII. The consequences of exposing sensitive information in a data breach will be catastrophic.
Examples of sensitive PII
This means data about a person’s identity such as race, ethnic origin, political opinions, religious or philosophical beliefs, trade union membership, genetic data, biometric data (where this is used for identification purposes), medical history, sex life or sexual orientation.
How does a combination of PII identify a person?
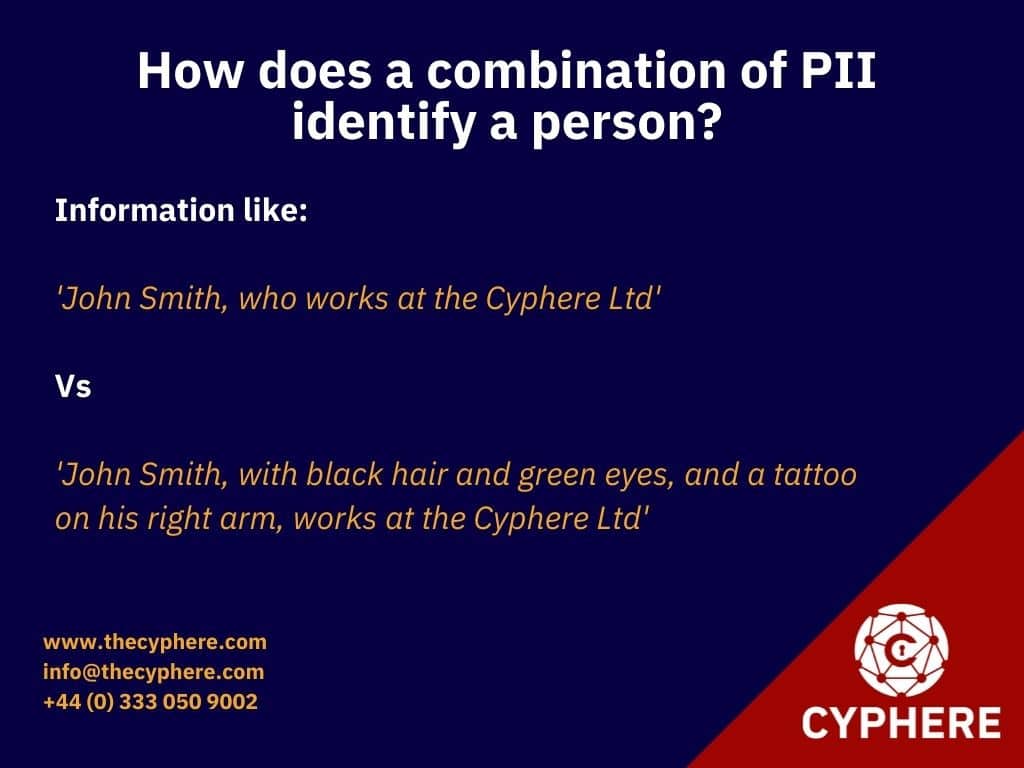
It should also be noted that when a single piece of PII is combined with other PII identifiers, the threat actors can develop a complete profile on an individual, which can have serious consequences for data privacy.
For example, an individual’s name, along with some other information, will be sufficient to identify them. the information like:
‘John Smith, who works at the Cyphere Ltd.’
Usually, this is enough information to identify a person directly. However, if it is a common name and more than one John Smith is working at this company, you would need extra information to identify them directly, such as:
‘John Smith, with black hair and green eyes, and a tattoo on his right arm, works at the Cyphere Ltd.’
This additional information aids in identifying that specific individual. The more personally identifiable information (PII) a threat actor has, the greater the risk to a company or individual.
How do we protect PII?
The following six best practices can be observed to protect personally identifiable information (PII), including sensitive company data:
1. Identify the PII you are collecting and make a PII inventory
A company cannot adequately protect personally identifiable information (PII) that it does not know about! This is the very first step of any risk assessment.
Begin by identifying all of the personally identifiable information (PII) that your company is processing. Identify as many potential sources of PII as possible (e.g., databases, shared network drives, backup tapes, contractor sites). You may need to identify data collected from your website’s contact forms or data collected for research purposes.
For example, if you are a software seller, you may have customer bank information and login credentials that you need to keep secure.
The best way to identify this data is to create a PII inventory.

PII inventory is a record of all PII housed within your company and on your website or its affiliates. It provides a centralised platform for all data stored in systems. However, putting that into effect requires some effort.
What should data inventory contain?
You need to create a centralised PII inventory and add all the relevant details related to it like:
- What PII you are collecting for which purpose?
- What PII identifiers do your systems contain?
- How much data do you have across all these systems?
- Do the stored PII belong to the customer/ lead/ employee/third party?
- The geographical location of this data? (the UK, US etc.)
- Is this PII shared with any third parties? If yes, list all third-party customer names?
- What controls are deployed for protecting PII against a data breach?
2. Classify PII based on their sensitivity
Once this inventory is created, you must classify this data based on its sensitivity level.
Data classification is organising data by relevant classification labels so that it may be used and protected more efficiently. The classification process makes data easier to locate and retrieve by tagging the classification labels, i.e. Confidential, Sensitive and Public data.
Confidential data
It is a highly restricted sensitive PII that includes identifiers such as name, social security, bank accounts or credit/debit card number, home address, compensation & benefits, medical history etc.
Sensitive data
This category has a moderate level of sensitivity that may include educational data of employees, dependents or beneficiary data, personally identifiable financial information related to revenue generation, marketing promotion development, system configuration settings; privileged user accounts information, service provider account numbers etc.
Public data
It is non-sensitive low-risk data that can be company-wide policies, internet-facing websites, blogs, social media, promotions-related data, news or press releases etc.
Confidential data requires more protection, whereas sensitive data requires less protection than personal data but more than public data. Data that is available to the general public is less secure.
3. Ensure purpose limitation and retention
If your company uses, gathers, and maintains as little PII as possible, the chances of a PII breach causing harm are considerably decreased.
A company should assess its holdings of current and previously gathered PII regularly to see if the information is still relevant and essential for the business purpose and objective.
The PII should only be collected for a legitimate purpose aligned with the applicable privacy laws like GDPR or any other privacy act across the globe. California Consumer Privacy Act (CCPA), Australia’s Privacy Act 1988, The privacy act in New Zealand, Family Educational Rights and Privacy Act (FERPA) in the US. The company should also establish a plan to eliminate PII’s unnecessary collection and use.
Any older, useless PII should be deleted to make it inaccessible to any possible attackers. Make careful steps to securely remove PII, and keep an eye on old files in your data backups that may include PII.
4. Apply encryption to PII and sensitive data
Encrypting your PII in transit and at rest is an unavoidable part of PII security. Use robust encryption algorithms with key management, and always encrypt PII before sending it over an insecure network or uploading it to the cloud.
To ensure that PII is encrypted, you’ll need the correct set of technological controls in place. However, there are several solutions available today that can automate the encryption process depending on data classification.
5. Apply the principle of least privilege
Companies that lose track of their access privileges leave their PII vulnerable to attackers. Mergers and acquisitions can also cause confusion and errors in access restrictions.
As a result, businesses must enforce the principle of least privilege when allowing access to other sensitive data. Consider network segmentation for specific areas of the organisation that deal with sensitive data processing.
The principle of least privilege concerns access control, emphasising that an individual will only have the access privileges required to execute a specified job or activity.
6. PII protect awareness training for employees
Employee education is a simple yet critical step while securing PII. Security education and training are not limited to stopping phishing attacks and their controls. It is a wider subject dealing with company culture, employee behaviour, understanding people and the psychological approach to tackling cyber attacks. This should be more than a security quiz through CBT-based training programs. Phishing is the most common attack vector in cyber attacks. Phishing attacks will not stop anytime soon, given the economics and the returns for cybercriminals to carry out cyber attacks.
Your company’s security and privacy awareness programs can be an essential feature for protecting the PII. Security awareness training sessions in an interactive manner are deemed to be more effective on how to access and store PII and how to ensure PII security through quizzes, newsletters, posters and other creative ways. See this excellent ICO data protection guide for further knowledge.
The training modules should also concentrate on related protection modules such as physical security covering device security, being aware of your surroundings, removable media usage, document access and disposal or leaving devices unlocked. Employees should be made aware of different types of processes and procedures related to the company’s policies around BYOD (Bring Your Own Device), access control, social media usage, emergency operations, data protection and Internet use.
Role-based customised security training
Designing customised security awareness training to meet the specific role-based requirement is also helpful. For example:
- Healthcare providers handling health records should receive security training on laws like the health insurance portability and accountability act (HIPAA).
- Human Resources involved in the employee onboarding process should know the requirements for applicable laws like UK-GDPR to handle PII carefully.
- IT Managers need security awareness training in their context to influence information security by deploying proper access controls, ensuring PII protection with two-factor authentication and securing employee laptops and mobile devices through an acceptable usage policy.
- The IT team is likely to be trained for the actual deletion of data under consumer inquiries or creating reports when consumers request access to their personal information.
- Customer service representatives handle calls to their toll-free lines and manage to respond to digital requests that come in via email or another online process.
- Marketing will need to inform the person in charge of the company’s policies of the new data collection method.
- Employees must be informed on how they can report a PII data breach incident.
Example scenario of how to protect PII
Assume that a human resources manager is required to deliver sensitive documents of employees to a pension organisation. These documents contain compensation and benefits data, salary data and other data identifiers that are sensitive PII. Non-sensitive personally identifiable information would include public records (phone books, directories, public databases). Non-sensitive PII or indirect PII is easily accessible and wouldn’t result in personal damage if lost or compromised as it’s already public.
The person, before sending out these documents, must ensure the following points:
- Encrypting document files at rest to ensure PII protection if an employee’s laptop is lost or stolen.
- Employing threat protection to keep his computer safe from viruses, phishing, and other threats.
- Using data loss protection software will alert him if he is going to submit a file containing personally identifiable information (PII) in plain text.
- Following the company’s acceptable usage policy will prevent him from using a browser with a known security flaw or storing PII on an unencrypted USB stick.
- They were blocking anonymous proxies for web searches because they allow proxy server admins to access PII.
- Avoiding public wifi while sending out sensitive information.
The above is not the comprehensive list of protecting PII, including sensitive company data steps. The risk assessment must be carried out in line with a risk management program, ensuring you are aware of important data to your business, security controls are assessed with IT risk assessments, gaps are analysed, and risks are treated accordingly.
Ending note
The PII stored by your company appeals to malicious attackers who can sell PII on the black market for a reasonable price. Data breaches caused by Identity theft, fraud, and social engineering attacks are all examples of how PII can be exploited for illegal purposes.
Businesses must protect PII data to avoid the consequences of non-compliance, as failure to protect PII exposes your company to highly focused social engineering attacks, significant regulatory fines, and a loss of customer confidence and loyalty.
Whether it is a dark web scan to monitor credentials leakage, risk assessment, or a proactive approach to compliance requirements, Cyphere offers services in this area that are tailored to your business objectives. Get in touch to schedule a call to know more about our no muss, no fuss approach.
Harman Singh is a security professional with over 15 years of consulting experience in both public and private sectors.
As the Managing Consultant at Cyphere, he provides cyber security services to retailers, fintech companies, SaaS providers, housing and social care, construction and more. Harman specialises in technical risk assessments, penetration testing and security strategy.
He regularly speaks at industry events, has been a trainer at prestigious conferences such as Black Hat and shares his expertise on topics such as ‘less is more’ when it comes to cybersecurity. He is a strong advocate for ensuring cyber security as an enabler for business growth.
In addition to his consultancy work, Harman is an active blogger and author who has written articles for Infosecurity Magazine, VentureBeat and other websites.













