What is Vendor Risk Management VRM?
Vendor risk management (VRM) is the type of risk management practice assessing and mitigating business partners, third party vendors, or external vendors. This process is conducted before an entity enters into a business relationship and during the duration of the business contract with the vendor.
Vendor risk management also serves as a baseline for healthy vendor relationship management. Vendor relationships can range from a small scale project with an independent supplier for a one time service to an ongoing vendor relationship with a large enterprise, essential for core business process.
Though vendor risk management strategy is effective with every scale of the business relationship, it helps run operations smoothly while protecting from business disruption.
Definition of vendor risks
Vendor risks refer to any external risks relating to the business operation that may potentially harm the activity of a client company.
What types of vendor risk need to consider?
Vendor risks can be of several types depending upon the nature of contracts and services. Some common examples that need to be considered are:
Legal risk
Legal risks arise when the vendor involves in a security breach and losing customer data like social security numbers or health information. The law mandates the business entity and not the third parties to be responsible for data loss. It is the responsibility of the business entity to define security expectations in their vendor contract because they are liable to the regulation.
Reputational risk
Reputational risk is associated with the business operations of the vendor. This type of risk is identified during the procurement process. A business entity would want to know if an external vendor has been involved in a lawsuit during the time of contract and how that could affect the performance of their contract. Also, reputational harm could affect business entities significantly if their customers’ sensitive information is stolen due to an untrustworthy vendor.
Financial risk
Financial risks arise when a vendor has a poor financial record or past performance. This information is always vital before contracting any external vendor as entities want to determine the financial stability before engaging in a business relationship.
Cyber risk
Cybersecurity risk is a vast type of vendor management risk associated with financial loss due to cyberattacks, disruption or damage to an organisation’s reputation from failure to comply with laws and regulations, unauthorised access to the business infrastructure, and inaccurate use of information systems. Cybersecurity risks eradicate the inability of the vendor’s digital technologies employed for operational functions and exploit the vendor’s system via electronic means from unauthorised access.
Why is vendor risk management critical?
There is not a single business that does not hire a vendor. Either it is for purchasing IT hardware, buying cloud services or hiring a vendor for human resource management. Having these vendors would always yield the vendor risks associated with their business. If these IT security risks are not identified and managed timely, it could result in business disruptions in the worst-case scenarios.
To learn the importance of cyber security risk management for third party vendors, let’s understand that with an example.
Suppose your company contracts with Google Cloud services to run its mobile application. If Google Cloud has downtime, your customers may not be able to access your app.
Another example could be a payroll entity contracted to process employee compensation and benefit plans. Since the third party payroll would deal with the sensitive data identifiers, if it involves a security breach, the company might face hefty penalties because of the poor vendor’s security assessment.
For modern businesses, outsourcing is a basic need to optimise core business functions. There are many aspects to running a business that isn’t related to the things you excel at. For that, companies need to consider hiring a third-party vendor that provides expertise and experience in an area unrelated to their core business mission.
The drawback to hiring a vendor
The only drawback to hiring a vendor is that companies disclose their infrastructure, customers information, and data. If a proper vendor risk management program is not in place, relying on external vendors can vulnerable business processes. Make sure external vendors are vetted and onboarded securely and safely with relevant checks and paperwork.
How can companies manage vendor cybersecurity risk?
Three foundational principles could yield an effective vendor risk management process, i.e.:
Vendor risk assessment
The vendor risk assessment process uses security questionnaires to help organisations identify the individual risk vendors pose to their business. For practical risk assessments, organisations must align their evaluation parameters with their accepted risk value. Doing this allows companies to build informed questionnaires that more accurately determine security threats related to the core business operations.
Security due diligence
Security due diligence is the process of pointing out third-party cybersecurity risks and remediating them by proposing appropriate controls. It is usually done during the merger and acquisition phase so that the acquirer is conscious of any security risks they may be receiving from vendors. To conduct security due diligence, organisations can assess vendors policies and procedures that must be regularly monitored to manage vendor risks as they emerge.
Compliance monitoring
Compliance risk monitoring is an essential component of third-party vendor risk management programs. By determining the applicable regulations and laws to monitor, organisations can improve their ability and identify vendor risk before it becomes problematic. This also helps organisations streamline contractual obligations aligned with secure business operations.
Vendor risk management lifecycle
The vendor risk management lifecycle is a series of stages that yields a typical relationship between a business entity and the vendor. VRM is also referred to as vendor relationship management. This term better provides an understanding of the ongoing nature of vendor engagements. Most commonly, the VRM lifecycle is broken down into the following stages:
1. Vendor identification
The first step of the vendor management lifecycle is to identify the existing vendors and list down all the new vendors required to hire for new services. The identifications can be made by leveraging a self-service portal as part of the risk management program. The portal invites all the business owners to share the preliminary information about the third party, such as vendor name, the scope of engagement and personal data involved.
2. Evaluation & selection
In this phase, companies consider requests for proposals and choose the vendor they want to use. This decision is made using several factors that are unique to the business operations and its specific needs.
3. Risk assessment
Vendor risk assessments take place to evaluate each vendor and analyse their inherent risks. This risk assessment can be done by using existing standards and frameworks such as ISO27001, NIST Cybersecurity framework or CSA CAIQ.
4. Risk mitigation
The identified risks after analysis are mitigated by using proposed controls and security standards. The risk scoring of vendors is placed against the risk appetite to plan treatment and control validation in the scope of the desired residual risk level.
5. Contracting and procurement
The contractual obligations are set in this phase (runs parallel with the risk-mitigating phase). This includes defined scope of services or products, term and termination clauses, confidentiality clause, limitation of liability, data processing agreement, second-tier or subprocessor change clauses and SLAs.
6. Reporting and recordkeeping
This includes documenting each activity of the risk management program, including total vendor count, vendors sorted by risk level, status on all third-party risk assessments, number of vendors with expiring or expired contracts.
7. Ongoing monitoring
This stage helps determine all the important risk-changing events in vendor risk management, including new laws, negative news stories, data breaches, and internal policy changes. It includes evolving usage of a vendor, which may greatly impact the risk significantly with third-party vendors.
8. Vendor offboarding
An offboarding procedure is critical to the vendor risk management process. Keeping records up to date and for the security purpose, it is vital to have a checklist developed for an offboarding process that confirms the company and customer information disclosed with the vendor have been taken back completely.
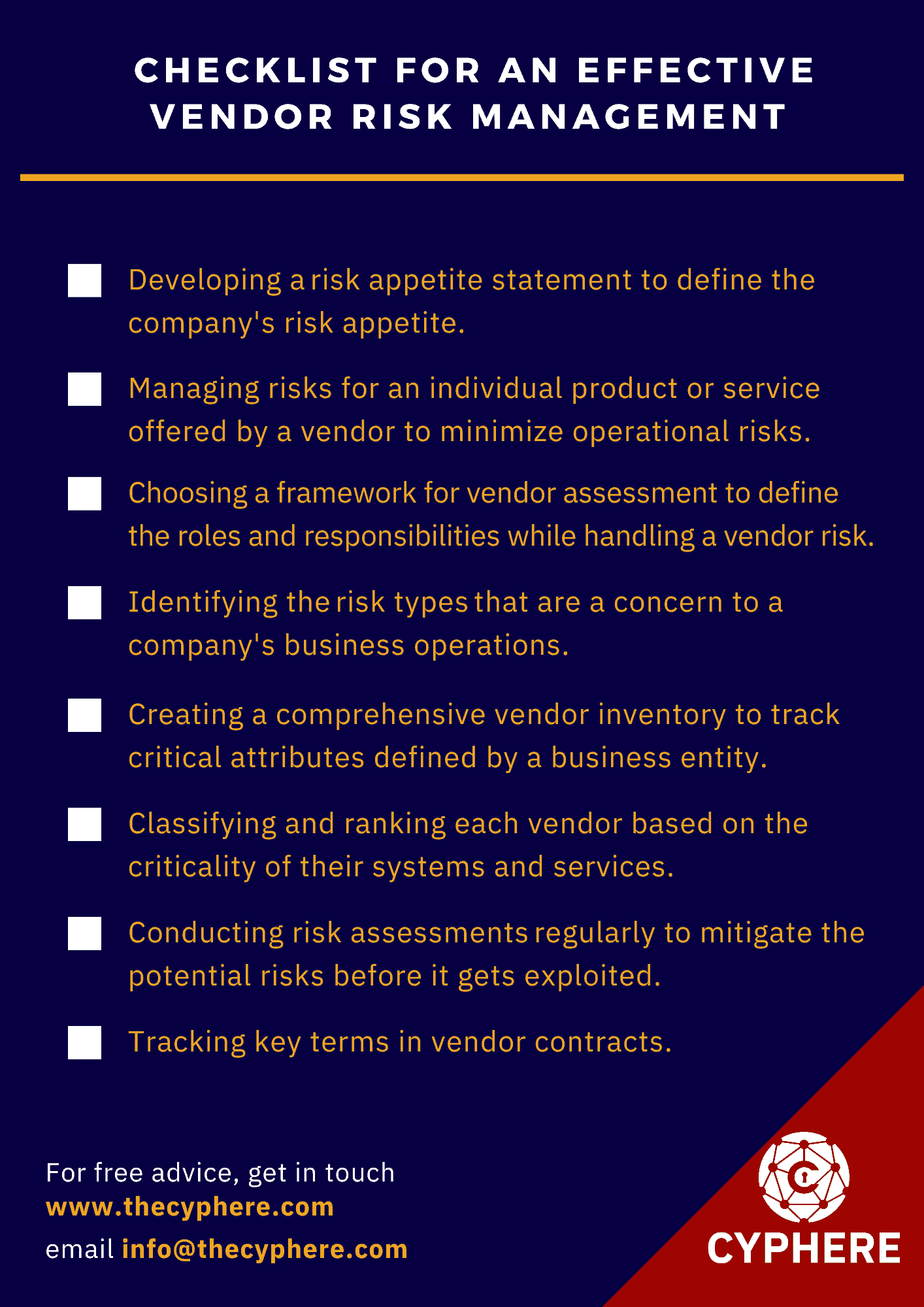
Checklist for an effective vendor risk management
How do you create an effective vendor risk or third-party risk management program?
Every business entity should have documented and implemented vendor risk management policies and procedures. These policies and procedures should be reviewed regularly to ensure the impact of changing business conditions. For that, entities need to establish standardised vendor and service provider evaluation risk ratings. These ratings will set a benchmark to assess existing and new vendors.
Policies should allow for regular review of vendor monitoring. This helps to reduce the risk exposure associated with a vendor or supplier. Companies should also incorporate vendor risk management programs into their policies that ensure they can perform the following requirements:
- It is developing a risk appetite statement to define the company’s risk appetite. Once the company identify the threshold of its risk appetite, it can understand what kind of vendor risk it can bear and what type of risk it should avoid.
- Managing risks for an individual product or service offered by a vendor to minimise operational risks.
- I am choosing a framework for vendor assessment to define the roles and responsibilities while handling a vendor risk.
- It is identifying the risk types that are a concern to a company’s business operations. Not every risk needs to be assessed as the assessment depends upon the business process and its outcome. So every VRM program should define the risk levels to eliminate the high and medium risk factors.
- We are creating a comprehensive vendor inventory to track critical attributes defined by a business entity.
- They are classifying and ranking each vendor based on the criticality of their systems and services.
- It is conducting risk assessments regularly to mitigate the potential risks before it gets exploited.
- We are tracking key terms in vendor contracts.
- They are reporting on relevant vendor-related metrics.
- We are monitoring risks and vendor performance continuously.
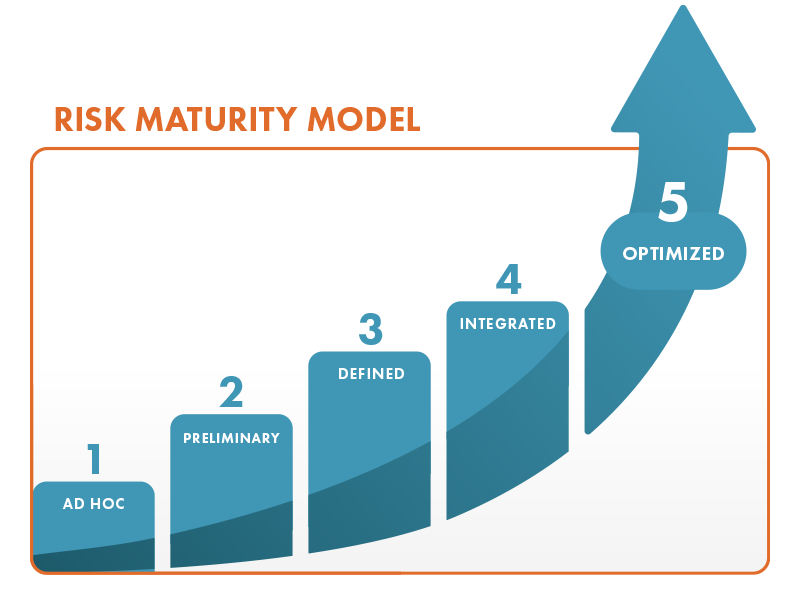
What is the Vendor Risk Management Maturity Model (VRMMM)?
The vendor risk management maturity model (VRMMM) helps business entities to set a framework for assessing the maturity of third-party risk management programs. The framework creates vendor management strategies to incorporate best practices for risk management into procedures and tools they can use to assess a vendor’s risk management program.
The framework also helps to assess the vendor management program in both its current and future states.
Vendor risk management maturity levels
There are five levels of vendor risk management maturity:
1. Initial stage
In this stage, there is an inconsistent approach to risk management. The risk ratings and risk appetite are not defined, and the procedures to evaluate security risks are discrepant. The vendor management strategies are not formalised and documented, though the ability to take risks depends on individual incidents.
2. Repeatable stage
The approach to risk management is still unstructured in this stage. However, companies may start developing their vendor management programs. They may begin to calculate risk ratings and their risk appetite to assess which vendor ranks top of the list.
3. Defined stage
The vendor management procedures and practices are defined, and companies successfully incorporate their vendor risk management program. The procedures and policies are documented, but there is still effort required to operationalise the vendor management into business practices fully.
4. Managed stage
Companies finally adopted the fully implemented and operational risk management programs. Vendor management policies for governance have been established, and compliance measures are an integral part of it. At this stage, the vendor management program also analyses the process improvements to make it more effective.
5. Optimised stage
The final destination of the vendor management maturity model is the optimised stage. The risk management program is effectively identifying and mitigating vendor risks. The industrial best practices are fully incorporated into the program. Nearly all the risks are managed, and the execution of crucial program elements has been automated. Ongoing monitoring of the program is running smoothly to align the program with governance standards and achieve compliance.
Wrapping up
The assessment of vendors is a vital concept of risk management strategy needed to put in place during the evaluation of external vendors and the procurement process. With that approach, organisations are mainly concerned with:
- regularly identifying business risks related to their vendors with timely mitigation of these risks by adopting security controls. And,
- Vendor management strategies to be incorporated in customer contracts for a healthy vendor relationship.
To address these requirements, the above article explains all the criteria for an effective vendor management process.