
If you’re searching for an ISO 27001 certificate, you’re moving towards a new business with world-class information security. This definitive guide gives you a step-by-step breakdown of the certification process and dives into how it strengthens your business’s commitment to data protection.
Key Points
- ISO 27001 certification validates an organisation’s commitment to an internationally recognised standard, enhancing customer trust and providing a competitive advantage.
- Obtaining ISO 27001 certification involves implementing an ISMS according to the standard, undergoing audits, addressing deficiencies, and emphasising risk assessment and staff training.
- Maintaining ISO 27001 certification requires regular internal and surveillance audits to ensure continued compliance, and it can serve as a differentiator in the market and help with regulatory compliance such as GDPR.
Decoding ISO 27001 Certification Process
ISO 27001, also known as ISO IEC 27001, is a globally acknowledged specification for Information Security Management Systems (ISMS) that showcases an organisation’s commitment to cyber attacks in a recognised framework. This internationally accepted standard is a testament to an organisation’s robust data security practices. It encompasses both online and offline aspects of business and aids in safeguarding against potential loss, theft, and impairment of essential assets such as customer records, financial information, data, and intellectual property.
The benefits of certified organisations attaining ISO 27001 certification are manifold. Not only does it instil confidence in shareholders and foster trust with customers, but it also provides a competitive edge. It is especially beneficial for organisations handling valuable information assets owned by others.
The primary goal of ISO 27001 is to create an efficient Information Security Management System (ISMS) framework. This certification process necessitates two evaluations: an initial review of existing processes and identifying improvement areas, followed by confirming compliance with ISO 27001 standards.
How to get ISO 27001 certification?
Acquiring ISO 27001 certification, or to achieve certification, involves the following three steps:
-
Developing and implementing an ISMS in line with the standard
-
Undergoing audits performed by the certification body
-
Addressing any identified problems to secure the certification
Risk assessment forms a vital component of risk management.
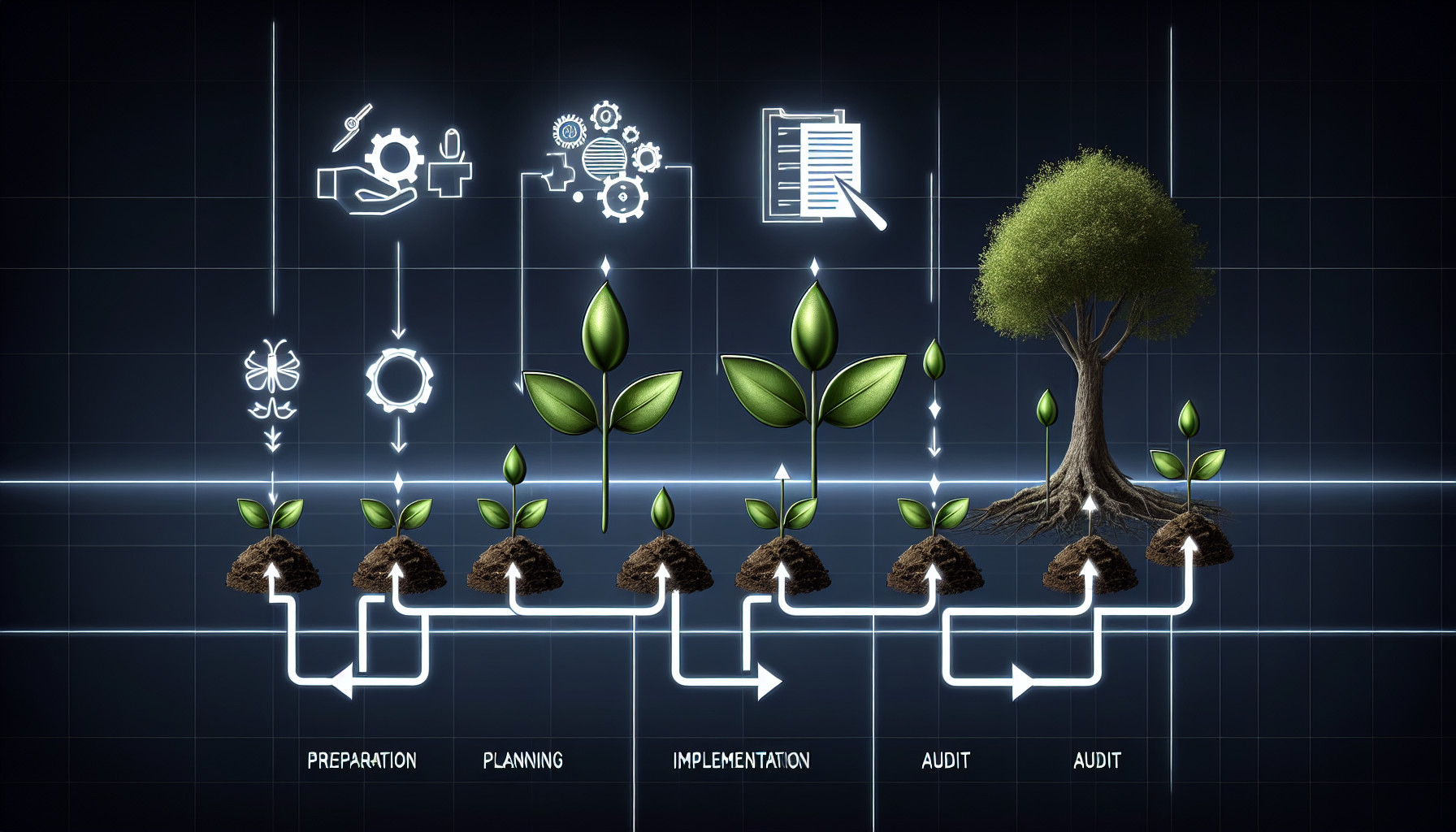
Preparation for the certification involves the following steps:
-
Development and implementation of an ISMS by the ISO 27001 Standard
-
Performing a thorough gap analysis
-
Ensuring the completeness of all essential documentation
-
Addressing any shortcomings
Selecting the right certification body is also a critical step in this journey. An accredited certification body, accredited by recognised authorities, is essential as they will conduct an impartial audit of your ISMS.
The ISO 27001 audit process involves:
-
A comprehensive assessment of the ISMS by auditors
-
A thorough review of the necessary documentation to ensure that all ISMS processes align with the ISO standard
-
Confirming compliance and addressing any identified issues
-
Awarding the organisation an ISO 27001 certificate
Preparing Your Organisation for Certification Audit
In preparation for a certification audit, thoroughly scoring the ISMS is imperative. This involves:

-
Determining the scope boundaries
-
Setting the scope of the ISMS
-
Carrying out a scoping and pre-audit survey
-
Planning and preparation
-
Fieldwork
-
Analysis
-
Reporting
A crucial part of this process is staff training. Ensuring that your team comprehensively grasps all the requirements and of the standard, can proficiently identify and manage information security risks, and develops the necessary procedures and controls to safeguard the organisation’s confidential information assets are invaluable for the certification.
During the audit, auditors typically seek evidence to ascertain gaps and areas for enhancement in your organisation’s information security practices and furnish a thorough report containing actionable recommendations. This process is critical for IT service providers to ensure the security of their client’s data.
Navigating the Certification Audit Stages
The certification audit process is broken down into two-stage process:
Stage 1 Audit:
-
The auditors review the organisation’s documentation to verify the development of the ISMS.
-
The review includes examining the documented processes and checking the presence of all necessary documents as mandated by the standard.
-
Non-conformities, or areas that require enhancement are identified and categorised as minor or major.
-
Major non-conformities require immediate attention. The organisation is given a detailed report and typically 90 days to rectify these issues.
Stage 2 Audit:
-
This stage assesses the implementation and effectiveness of the ISMS.
-
The organisation must completely adhere to its documented information security management policies and procedures.
-
Upon completing the Stage 2 audit, the organisation is officially recognised as meeting the necessary standards and granted the ISO 27001 certification.
The Value of an Information Security Management System
An Information Security Management System An information security management system (ISMS) is an organised approach vital for managing confidential company data to ensure security. Establishing an effective ISMS by ISO 27001 involves systematically evaluating risks to information security and implementing thorough policies and procedures to mitigate those risks.
Implementing an ISMS and achieving ISO certification offers a myriad of benefits, such as:
-
Strengthening the organisation’s security posture
-
Demonstrating a serious commitment to security to customers and stakeholders
-
Assuring that the business controls and management processes are robust enough to tackle identified security threats.
The concept of continual improvement in ISO 27001 involves the routine identification of security risks and updating policies and procedures to effectively manage these risks, thereby reducing risk exposure and ensuring the sustained effectiveness of the ISMS.
The continual improvement approach aligns with the growth roadmap of SMB businesses, as services like those offered by Cyphere allow these businesses time and business case buy-in from senior stakeholders, showing improvements as they grow.
ISO 27001: Beyond the Basics
There are additional challenges associated with ISO 27001 compliance beyond the fundamental requirements. These include:

-
Completing process updates
-
Conducting regular internal audits
-
Passing annual external audits
-
Resourcing the implementation
-
Addressing over 140 separate activities
One crucial element of ISO 27001 is the concept of continuous improvement. This stimulates organisations to consistently enhance the performance, effectiveness, and efficiency of their information security controls and processes.
ISO 27001 is not just about meeting the minimum requirements but also about implementing robust information security measures. It establishes a comprehensive and powerful framework for attaining and showcasing adherence to data protection regulations such as GDPR. It guarantees data protection by helping organisations fulfil and showcase compliance with the privacy and security stipulations of the GDPR.
Risk Management Process in ISO 27001
The risk management process is a pivotal part of ISO certification. It involves identifying, assessing, and prioritising risks, followed by applying resources to minimise, monitor, and control the impact of these risks. This process is integral to developing and implementing an effective Information Security Management System (ISMS).
The risk management in ISO 27001 is continuous and cyclical, involving regular review and updating of risk assessments to ensure that the ISMS remains effective even as the organisation’s risk landscape changes.
This process is not a one-time event but a continuous cycle that involves risk identification, risk assessment, a risk treatment plan, and risk management monitoring and review.
Cost Considerations for ISO 27001 Certification

The cost of acquiring ISO 27001 certification is contingent upon the scale and extent of your company, as well as the intricacy of your information security management system. Businesses should exercise caution regarding undisclosed and continual expenses linked to certain certification bodies, such as management and travel fees not encompassed in initial estimates.
The costs for personal ISO 27001 certification, including training and exams, differ by country and are usually clearly presented by training providers.
Organisations can consider remote stage 1 audits to manage costs effectively, which can help reduce travel expenses, additional costs, and time. Cyphere provides cost-effective methods for certification audits to ensure quality and pricing with multiple options.
Maintaining and Leveraging Your ISO 27001 Certificate
Maintaining ISO 27001 certified certification involves upholding compliance throughout its validity period of three years, forming a certification cycle. Regular internal audits are integral in maintaining ISO 27001 certification. They ensure the organisation’s Information Security Management System’s effective functioning and alignment with the standard’s requirements throughout the certification cycle.
Annual Surveillance Audits and Recertification
Annual assessments of data breaches, also known as surveillance audits, are part of the ISO 27001 certification process. These data breach audits confirm the continuous adherence of the Information Security Management System (ISMS) to ISO 27001 standards, verifying its effective operation throughout the three-year certification cycle.
The recertification process encompasses conducting yearly assessments to verify continuous compliance with legal requirements, culminating in a comprehensive recertification audit after the three-year timeframe.
Capitalising on Certification for Market Advantage
ISO 27001 certification showcases an organisation’s dedication to cyber security best practices, highlighting a strong emphasis on confidentiality, integrity, and client availability. It plays a crucial role in fostering customer trust and confidence.
ISO 27001 certification can function as a marketing tool by showcasing a firm’s dedication to protecting sensitive data, adhering to regulations, and securely managing customer information.
It underscores reliability, integrity, and dedication to customer satisfaction, making its service provider more appealing to prospective clients.
ISO 27001 and Regulatory Compliance
ISO 27001 certification serves as a means to demonstrate to stakeholders and regulators that an entity is in alignment with legislation such as GDPR or the Data Protection Act (2018). ISO 27001 certification can be advantageous for GDPR compliance due to the absence of an independent and universally recognised certification for the regulation.
ISO 27001 certification is aligned with General Data Protection Regulation (GDPR) requirements as it assists organisations in fulfilling legal obligations and showcasing compliance with the privacy and information security stipulations of the GDPR.
Selecting the Right Certification Body
Choosing the right accredited certification body boosts the effectiveness of your certification by retaining existing clients and attracting new ones. At the same time, its reputation promotes trust and enhances your reputation to win credibility among stakeholders, customers, and partners.
Selecting a UKAS-accredited certification provider, such as certification bodies like the British Assessment Bureau, demonstrates that your ISMS undergoes thorough scrutiny, surveillance audit, and validation and is upheld to the highest standards by an impartial third party.
Key considerations to take into account when selecting a certification body for ISO 27001 include:
-
The body’s specialisation in your industry, size, and maturity
-
Reputation
-
Accreditation
-
Experience
-
Integrated audit capability
-
Flexibility
-
Language proficiency
From Preparation to Certification: A Pragmatic Approach
The Assured Results Method provides a pragmatic and systematic approach to implementing an information security system to ease the acquisition of ISO 27001 certification. This method involves a systematic strategy to ensure successful accreditation on the first attempt. Organisations seeking ISO 27001 certification are advised to:
-
Thoroughly review and comprehend the ISO 27001 standard
-
Engage management
-
Perform an internal audit
-
Formulate a risk management plan
-
Tackle crucial matters to ensure ongoing compliance.
Typical obstacles organisations face when pursuing ISO 27001 certification include:
-
Understanding the guidelines
-
Building a security framework
-
Identifying security gaps
-
Convincing the board that information security is a business issue
-
Securing board and employee buy-in
-
Building a security culture
-
Allocation of resources
-
Compliance maintenance
These challenges can be overcome through strategic planning, effective communication, training, management reviews, and utilising available resources by a competent management team.

Cyber attacks are not a matter of if, but when. Be prepared.
Box-ticking approach to penetration tests is long gone. We help you identify, analyse and remediate vulnerabilities so you don’t see the same pentest report next time.
Information Security Management Systems in Action
Hundreds of companies have effectively navigated the ISO 27001 certification process, overcoming challenges and achieving certification, such as:
-
Understanding the standard’s guidelines
-
Establishing a robust security framework
-
Identifying gaps in their information security
-
Defining the correct scope for the certification
-
Ensuring management commitment
-
Adequately resourcing the project
-
Overcoming any technical feasibility issues.
Following the gap analysis and controls implementation, Cyphere customers observed various operational improvements, including:
-
The demonstration of robust security practices
-
Improved client relationships
-
Improved security posture against potential cybercrime situations such as ransomware, incident response readiness against a cyber attack
-
The fostering of a culture that encourages ongoing enhancement in information security.
Summary
In conclusion, ISO 27001 certification is a potent instrument for organisations to prioritise the security of their information assets. Understanding the certification process, preparing for the audit, choosing the right certification body, and leveraging the certification for market advantage form the core of the journey towards ISO 27001 certification.
Cyphere stands out as the ideal partner in this journey, with a flexible approach tailored to each customer’s unique requirements. We simplify the certification process into manageable steps aligned with your long-term business objectives.
Achieving ISO 27001 certification, with the proper preparation and approach, is an attainable goal that yields significant benefits. Let Cyphere guide you in securing this valuable asset for your organisation to us today!
Frequently Asked Questions
How do I get ISO 27001 certification in the UK?
To obtain ISO 27001 certification in the UK, you must develop and implement an ISMS that meets international standards and requirements and then register for certification with an accredited body. This process involves establishing an Information Security Management System (ISMS) and undergoing assessment by a certification body.
What is the validity duration for ISO 27001 certification, and what constitutes the certification cycle?
ISO 27001 certification remains valid for three years, constituting the certification cycle during which the organisation complies.
What steps should organisations take for ISO 27001 certification?
To prepare for ISO 27001 certification, organise and implement an ISMS, conduct a comprehensive gap analysis, ensure completeness of essential documentation, and address any shortcomings accordingly.
What is the significance of regular internal audits in upholding ISO 27001 compliance?
Regular internal audits ensure that an organisation’s Security Management System effectively aligns with ISO 27001 requirements, upholding compliance.
What are the benefits of selecting a UKAS-accredited certification provider for ISO 27001?
Choosing a UKAS-accredited certification service provider like the British Assessment Bureau ensures that your ISMS is rigorously evaluated and meets the highest standard set by an independent third party. This can enhance the credibility of your ISO 27001 certification.
Harman Singh is a security professional with over 15 years of consulting experience in both public and private sectors.
As the Managing Consultant at Cyphere, he provides cyber security services to retailers, fintech companies, SaaS providers, housing and social care, construction and more. Harman specialises in technical risk assessments, penetration testing and security strategy.
He regularly speaks at industry events, has been a trainer at prestigious conferences such as Black Hat and shares his expertise on topics such as ‘less is more’ when it comes to cybersecurity. He is a strong advocate for ensuring cyber security as an enabler for business growth.
In addition to his consultancy work, Harman is an active blogger and author who has written articles for Infosecurity Magazine, VentureBeat and other websites.












