It might be hard to believe that your computer can be hacked; you might have heard people saying I have been hacked, which is a severe threat. People have stored many files containing personal data or sensitive data on their computers, and attackers are always looking for ways to access them. You may be one of those who claim that they have been hacked, but they have no idea what to do next or how to repair the breach. If you think you have been hacked, then the first thing you should do is learn about the steps taken immediately to secure it!
My computer has been hacked. How do I fix it?
You wake up to a blue screen on your laptop. A message shows that your computer has been hacked or your account has been hacked, and all of your files are encrypted with a strong password. Your heart starts racing as you figure out what to do next. Hackers can be very persistent, so you must take steps quickly if this happens to you! This article will provide information on how to fix the problem and how to find computer hackers for them not to attack others in the future. Anyone can fall victim to an attack; preparedness is the key.
There’s barely a day without some company, app or website suffering a data breach. To avoid compromising your computer, set your security software, internet browser, and operating system (like Windows, Mac OS X or other operating systems) to update automatically. Attackers carry out malicious acts for various reasons, but it is mainly used as vandalism or revenge against the owner of the hacked computer.
How to know if your computer has been hacked?
While cybercriminals will continue to find new methods to infiltrate your devices, there are ways to remain vigilant and aware of your computer’s security status.
First things first, let’s get some myths out of the way:
Can you be hacked while offline?
No.
Can you be hacked if your computer is not connected to Internet?
No. Technically, it’s impossible to infect a computer not connected to the Internet.
Yes, if this system interacts with peripheral devices such as USB drives, external hard disks, memory cards or any devices that can be used to store and transfer data to/from the isolated system.
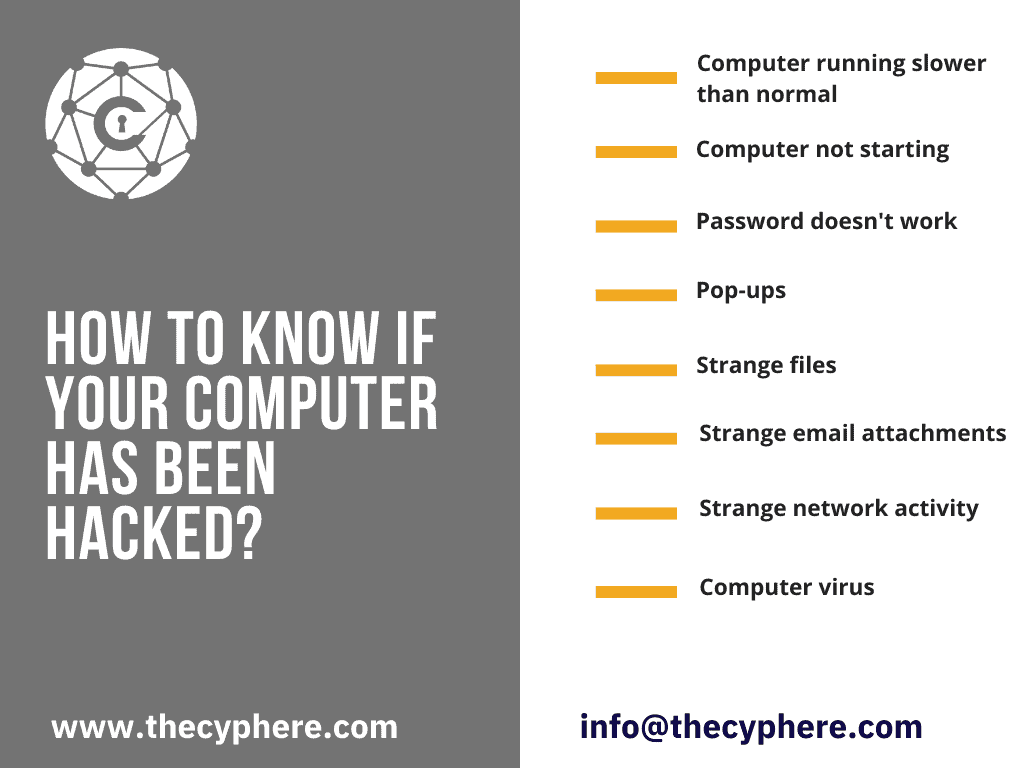
It is not always easy to tell if your computer has been hacked; there are some signs you can look for.
Computer running slower than normal
If you notice that your computer is running very slowly, then it might be a sign of hacking. Hackers can install malicious software to slow down computers to get more time before they are discovered.
Computer not starting
If your computer does not turn on at all, it might be a sign that the hard drive has been deleted or corrupted, which happens when hackers get into computers.
The same password doesn’t work.
If you notice that when trying to log in with an administrator password that it doesn’t work, then this is a sign of hacking. Attackers can change passwords to prevent you from getting back into your computer unless passwords have been restored.
Identity theft
Suppose your banking or other personal info has been compromised. In that case, it is important to limit the damage by calling your bank, cancelling and requesting a replacement card and filing complaints of action fraud.
Pop-ups
If your computer randomly pops up with strange messages or windows asking for payment to fix something, it might be another sign of computer hacking. These could also be fake warning signs or ads which criminals use to get people’s money.
Strange files
Computer hackers will often install malicious software on your computer and leave it there for future cyber attacks. If you notice that there are strange or unknown programs, then this is another sign of hacking or maybe a data breach. You can also look through your installed program list and see if anything stands out as not being familiar. Attackers can also delete files on your computer which you might notice are gone when trying to access them later, but this is rarer since they usually want to use the computer for their purposes if they do get into it.
Strange email attachments
Threat actors know that many people open up emails from unknown senders because they might be expecting a message. Attackers can send phishing emails or fake antivirus messages, or antivirus software notifications which will trick you into opening up an attachment and getting their malicious software onto your computer. If you notice any strange messages on your email accounts or social media account, it is important to not open any attachments from them since this could lead to further problems down the road.
Strange network activity
It can also be possible for cybercriminals to use their computer to access other systems. If you notice that there is a strange network or internet connection for programs that you have never installed, then this is another sign of hacking. Hackers might install remote access tools onto your computer, which will allow them to access it from a remote location.
Computer virus
Cybercriminals can gain access into your computer by infecting systems with computer viruses and install different types of malware onto the system to make money off advertisements, hijack email accounts, social media accounts, bank accounts, other personal accounts or even use your computer for other illegal means. It might also indicate that your system has been hacked.
What to do if your computer has been hacked?
Once you’ve discovered that your system has been hacked, it’s time to take some action. There are many threat actors who try to sell computer security services to get your computer back, also known as tech support scammers. These can often be scams, so it is important not to give out any information or click on anything suspicious link that they might send you. Attackers sometimes use several techniques, i.e. domain hijacking, spoofing attacks, social engineering techniques, etc., to carry out various types of attacks.
- Do not panic; try to stay calm. This will ensure you can act faster and strategically to limit the loss of personal data.
- Disconnect the computer from the Internet: pull the network cable or turn off the wireless connection based on which type of Internet connection you are using.
- Remember, reset your key account passwords starting with accounts with single-factor authentication and high severity accounts, i.e. Internet banking, shopping accounts, utilities & identity-related websites.
- Remove any peripheral devices attached to the system. These could be USB drives, external hard drives or SD cards.
- Run an antivirus scan to get rid of viruses or any infections.
- Let your close friends and contacts know about your situation if they receive any impersonation emails, messages or other asks.
- Monitor your financial accounts with credits, debits and statement activities.
- Call your ISP and speak to them if they can assist with this scenario, and check the bandwidth usage if your system is part of a denial of service or DDoS/botnet infrastructure.
- Take steps or technical help to repair a hacked pc to ensure your information is still not exposed due to malicious code still present in your system.
You can read more about types of cyberattacks here:
Attackers might have installed something onto your computer, and you should be able to find it on the list of processes running on the system. You can check what services have been started up by attackers if someone is remotely accessing your system and disable these if you are not familiar with them.
Criminals might also install services that you will find suspicious, but again, it is essential to know what these programs do before uninstalling them.
Use either the security software that comes with your computer, phone, or tablet or download software from a reputable, well-known security company. Computer attackers can get into your computer and change the configuration of specific settings in order for this process to go unnoticed.
You should check if attackers have changed any startup settings and what they have changed them to, but again do not change anything unless you are sure about what the attackers did. In this way, you may protect yourself from the many harms that hackers might cause.
How to fix a hacked computer?

Regaining control of your system may not be straightforward, depending on who has access. Hacker groups often do not care about the security of your computer and will use brute force techniques for them to gain access. Each company will have its policies, procedures, and account recovery steps when it comes to compromised accounts. However, to restore your system to normal, you may use the methods described below:
Running safe mode
Safe Mode is a way to keep your computer safe. It doesn’t let anything wrong happen when you turn it on and only runs the essential things in an operating system. This Mode is used to fix your security and other system stuff problems.
Scanning and removing rootkits
If rootkits have been installed on your computer by attackers, you should run antivirus software or an anti-rootkit program that can identify and remove them as directed by attackers.
Changing password
It is also possible that if a hacker has been able to access your system, email account or social media account, or personal information, this might be a sign that hackers have been able to get into your other accounts like google account or bank or any online accounts. If this is the case, you should change the password of your email account, social media account, online banking accounts and all system passwords and never use the same password again.
You must change passwords of all personal accounts after data breaches for attackers not to be able to access them in the future. Also, if you can get back into a hacked email account, double-check the account settings to ensure that they haven’t been tampered with.
Removing/Uninstalling suspicious processes
You need to scan all of the files you have with antivirus software to ensure that none is infected. Your system is secure, and attackers can use viruses, worms and Trojan horses to infect systems to get their malicious software onto them.
Attackers may have installed many other programs on your computer. It will help if you start by identifying these processes so that you can uninstall and remove them. Attackers might disguise their presence by changing the name of processes, but there are ways to find out what attackers did.
Checking startup settings
Attackers might have changed some startup settings, so it is vital to check them. They might have done this to hide malicious processes in the background.
If they did, you could use MSConfig to check the startup security settings of a hacked computer and restore them if attackers changed anything.
Backing up your data
Attackers might try to access your sensitive data, including credit card account details, email addresses, or personal data and this way, they will be able to delete your backups. You should ensure that criminals can’t access them before restoring them to your system again. Attackers might also delete your backups to hide their presence on the computer.
Computer hacking can also happen when hackers try out different programs available on the Internet and combine them with other tools that they find online, which may get access to your system, credit card account, email addresses or social media or other online accounts. You will often need computer security experts or professionals who know what they are doing to remove malicious programs from a remote computer.
If you want to prevent attacks on your system, then you should always make sure that there are no open ports on the computer. Attackers often use port scans to find out what they can use on a remote system, so you should close them if there is no need to access your computer remotely.
Frequently Asked Questions – signs of computer and phone devices getting hacked.
How can hackers access your computer?
Hackers can remotely access your computer in multiple ways. This could be through malicious software installed on your computer without your knowledge. This takes the form of browser toolbars installation, search bar, pop-ups you clicked to install something or as part of a phishing email that asked you to do something in return for a fake service or product offered to you.
How can hackers get your password?
Here are the top ways hackers steal your passwords:
- Credential stuffing attacks
- Phishing
- Password spraying
- Keylogging
- Brute force attacks
- Spoofing attacks
- Fake extortion emails start with an email displaying one of your leaked passwords online and prompting you to submit your credentials.
- Due to your lack of awareness – you are writing down passwords, plain-text storage somewhere, etc.
How can hackers hack your phone?
Hackers find their way into mobile devices just like computers. Through phishing emails, links to persuade you to download legit-looking mobile apps, too good to be valid offers in various forms, etc.
Does google tell you if you have been hacked?
Yes, only to a certain extent. It won’t tell you entirely about your computer system, but it tells you anything malicious you are visiting through Google chrome or your account passwords.
Google chrome could alert you if your passwords were disclosed in data breaches. You can go to privacy settings and check passwords to see if any of your passwords were involved in leaks. You should change those passwords and turn on two-factor authentication where possible.
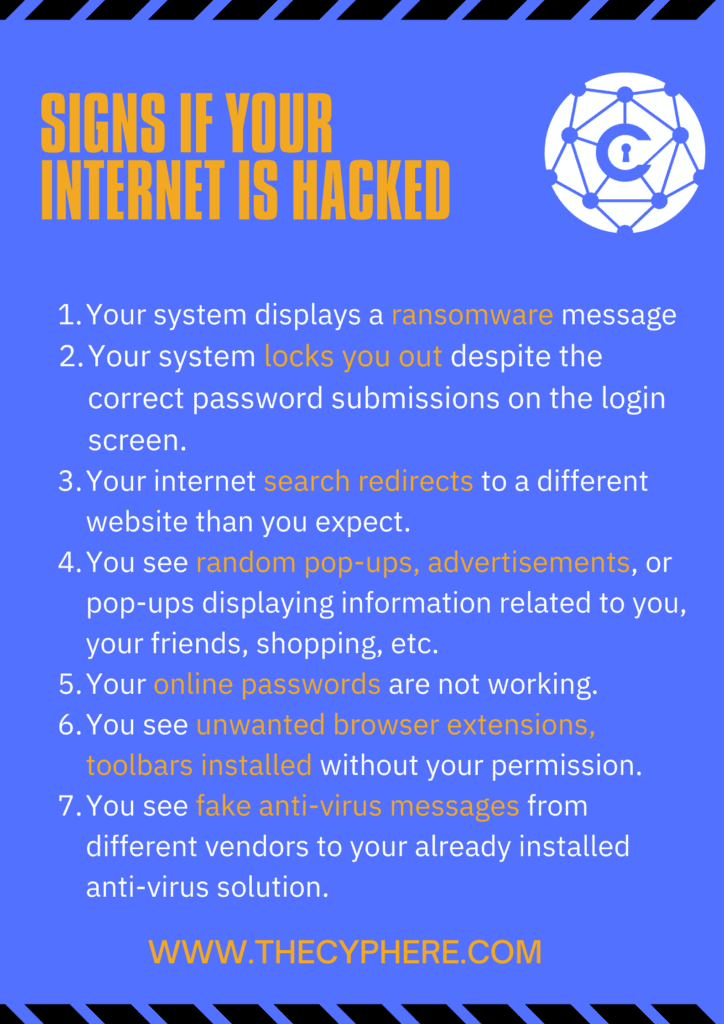
Can you tell if your Internet has been hacked?
This relates to any of the long lists of initial symptoms to know if you’ve been hacked:
- Your system displays a ransomware message
- Despite the correct password submissions on the login screen, your system locks you out.
- Your internet search redirects to a different website than you expect.
- You see random pop-ups, advertisements, or pop-ups displaying information about your friends, shopping, etc.
- Your online passwords are not working.
- You see unwanted browser extensions and toolbars installed without your permission.
- You see fake antivirus messages such as fake antivirus scan from different vendors to your already installed antivirus software.
Can hackers access your computer when it is off?
No. There is no way to access a system’s components when it’s not operational.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.