Whether you are considering vendors for a particular solution or complying with assurance requirements, this article helps you understand SaaS security.
What is the meaning of SaaS?
Software as a Service, also known as SaaS, is a cloud-based service model where a subscriber uses the software via an internet browser. This software could be anything from a simple application such as MS Word to complex business applications such as SAP. All the software tech stack or backend components are located on external servers maintained by the SaaS provider. Before diving into why security testing in SaaS applications is important element for your business strategy, let’s go through the basics and then SaaS security best practices.
Software as a Service (SaaS) applications differs from traditional software delivery model in two ways:
- Hardware, software setup and maintenance headache is gone. Most of the IT responsibilities are SaaS providers responsibility.
- Costs are subscription model, usually priced on a monthly, quarterly or annual basis.
In 1961, Professor John McCarthy said at MIT’s centennial celebration, “Computing may someday be organized as a public utility just as the telephone system is a public utility. Each subscriber needs to pay only for the capacity he actually uses,….”.
The year was 1961. How true is that!
You can watch a condensed version of this article here:
What are the examples of SaaS?
- Zendesk – Online customer support platform allows you to set up your customer support desk with all standard customer service features.
- Shopify – You can set up an eCommerce store and start your online shop in no time.
- Microsoft Office 365 – Microsoft offers its standard software online without worrying about setups, installation and maintenance.
Thousands more such software have moved to SaaS offerings.
SaaS vs PaaS vs IaaS
Cloud computing operates in three main ways, i.e. SaaS, PaaS and IaaS. Cloud providers often price their cloud computing model around these three ways:
- SaaS: Software as a Service (SaaS) is software available via a third party over the internet. SaaS covers about 24% of all enterprise networks.
- PaaS: Platform as a Service model provides hardware as well as software tools via cloud offerings. PaaS is the most popular model.
- IaaS: Infrastructure as a Service includes cloud-based services such as networking, virtualisation, storage, etc., mainly offered as a pay-as-you-go model.
Here is a cloud shared responsibility model diagram showing differences in the SaaS, PaaS and IaaS architecture.
SaaS vs PaaS vs IaaS Examples
It is easier to understand with examples of how various cloud models differ in terms of usage and flexibility. It is common to see the combined use of Saas and IaaS computing models in an enterprise. Here are some of the SaaS vs PaaS vs IaaS examples:
- SaaS examples: Salesforce, Slack, Dropbox, DocuSign
- PaaS examples: Windows Azure (mostly PaaS), Magento Commerce Cloud, AWS Lambda, Heroku
- IaaS examples: AWS EC2, Digital Ocean, IBM Cloud, Oracle Cloud, Azure
What is SaaS security?
SaaS security relates to securing sensitive data and ensuring the security for SaaS applications. These apps process gazillions of bytes of sensitive data making it accessible at any corner of the globe. Privacy and data protection are the two biggest SaaS security threats. Without sounding like causing any fear and doubt factor here, some enterprise-level SaaS cloud providers ensure that their web apps, services and the underlying information are as secure as banks. Businesses often opt for third party security assurance to identify SaaS security issues and solutions. It offers multiple benefits:
- Identification, classification and remediation of SaaS security risks uncovered by security experts
- Attestation for regulatory, commercial requirements where third-party validation proof is required
Cloud security risks
The leading cloud security threats observed across the internet are:
- Data breaches (due to many reasons, including the below risks)
- Human error
- Data loss due to no backup
- Insider threats
- Insecure APIs
- User account compromises
- Other attacks (Advanced Persistent Attacks, Phishing, shares services exploitation, etc.)
SaaS application security
A secure application in the traditional sense is more about how best to configure, tweak and change code aspects to add security. You may follow the OWASP checklist of top risks and should be good to go against the most common types of cyberattacks. Similarly, to find an extensive list of security issues in SaaSg applications and underlying data, you should consider SaaS security testing. It identifies gaps in your security controls and provides advice on remediating the security risks affecting your apps.
It is essential to investigate the data security aspect before buying SaaS services. Multiple elements such as cloud, web application security, API security and network security practices are at play when considering security-minded SaaS vendors. It is equally important to keep this in mind – it is an ongoing process, and this is not a one-time tick box homework. SaaS security as a service is one such way to manage this continuously.
SaaS security checklist
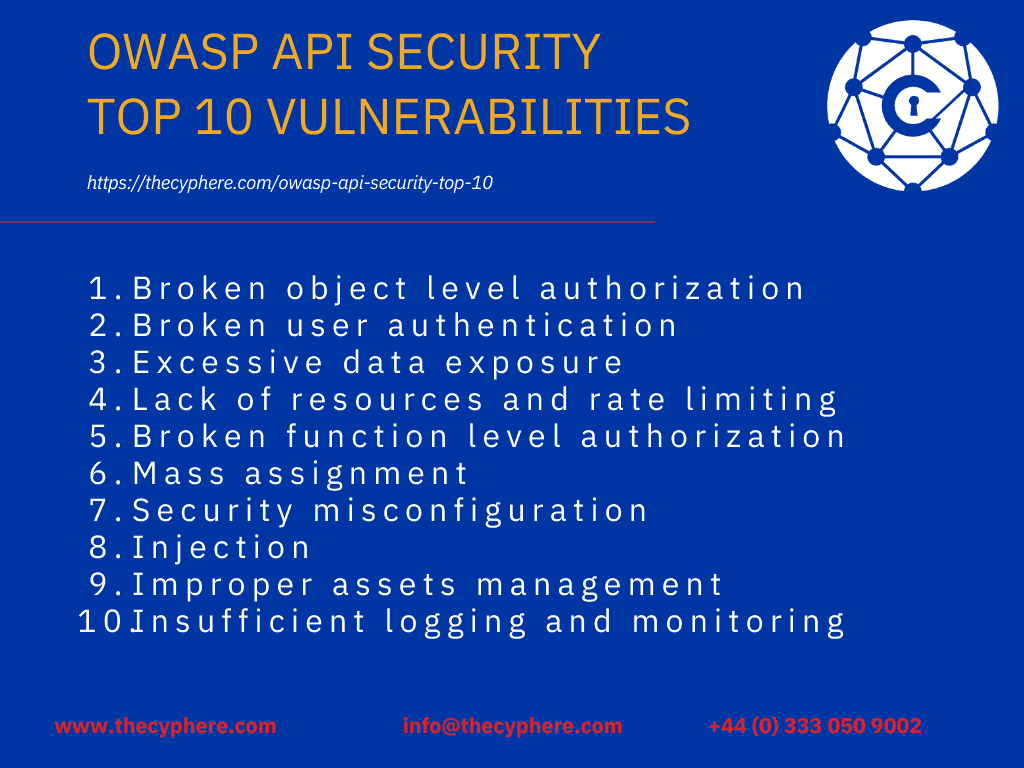
Several SaaS security principles should be followed to answer if the provider is doing enough to protect user data. Be careful this list doesn’t apply to the product at the code level, for which you should look into OWASP top 10 risks for applications and APIs. This security checklist is also usable as internal guidance or extended to include SaaS security best practices in each area to avoid pitfalls when considering marketing your SaaS product.
Cyber security ‘in letter and spirit.’
It should do what it exactly says on the tin.
Cyber security should not be limited to marketing fluff but adopted as a proactive measure by the SaaS providers. Security aware cloud providers and SaaS vendors often share their annual validation results and explain security features on their websites or customer portals. If you haven’t come across this documentation, you should prompt the potential vendor during the product demo. It may act as an excellent opportunity to learn about the security features of cloud service in action. Overall, the service provider’s business portal or vendor section should have an exact process in dealing with the following areas:
- Security advisories around publicly reported flaws.
- Patching availability, status and updates
- Resources around cyber security practices for SaaS users
- Regulatory assessments and security decisions around cloud services (based on sector)
In our experience with SaaS vendor security, many are still climbing the maturity ladder. Small and medium-sized organisations often tend to forget security during design and development. Now, in a flash, a big tender has a mandatory requirement – third-party assurance. Running around to find a security service provider to provide you with a quote and deliver a service is not the end of it all. You need to consider timelines for SaaS security testing, liaison with third-party if involved in the development and maintenance, risk remediation of assessment findings and then a revalidation to ensure there are no residual risks.
Multi-factor Authentication
The use of multi-factor authentication (MFA) on privileged accounts is a no brainer. It decreases the risk as a threat actor would need to perform more complex attacks to target MFA tokens. Many data breaches occurred due to the easy compromise of highly privileged accounts using phishing attacks. Although certain MFA implementations could be susceptible too, the likelihood of such attacks is relatively lower than not using MFA at all.
Authentication and Authorisation
Authentication and authorisation are amongst the top two most important aspects of SaaS application security. At a higher level, this phase is mainly Identity and Access Management (IAM). These SaaS security best practices determine if a user should or should not have legitimate access (authentication) followed by access levels and roles (authorisation). Broken authentication and session management are the main security risks related to login mechanisms, access controls, keys, session tokens or implementation flaws that may allow an attacker to compromise accounts. The exploitation of authentication and access control vulnerabilities occurs in many ways, such as brute force attacks, take over user sessions, enumerate legitimate user data and related implications.
Secure encryption configuration
Data at rest should utilise strong encryption measures, including strong cloud security measures for backup data. It is similar to data encryption of your laptop hard drive. Similarly, protecting information such as client sensitive data is a crucial factor for most businesses out there. Lack of seriousness around data protection and missing secure SDLC (Software development lifecycle) steps alone could be a red flag while considering the security of SaaS solutions.
Data in transit between the clients and service vendor should be protected. Secure encryption configuration provides the needed privacy and protection from eavesdropping, tampering or other interferences. The use of TLS protocol is the de-facto standard for securing data in transit over the web. Although TLS 1.3 is the current version, TLS 1.2 is the most popular version in use. Any predecessors such as TLS 1.1, TLS 1.0 and SSL versions are considered insecure. Similarly, sensitive data in transit between microservices, whether within the same cloud or multiple cloud services, must be protected similar to client/service protection levels.
API security
API security vulnerabilities are an ignored area, receiving much love from threat actors. This is often due to the misconception that they are hidden. Although hidden from user view, APIs are not hidden from the browsers in complete control of an internet-based threat actor. Insecure or missing protection mechanisms for API endpoints causes broken user authentication flaws. All internal and external APIs dealing with sensitive or customer data must use an authentication mechanism. To mitigate insecure API risks, OWASP top 10 API security checklist should be followed to secure all communication endpoints.
Privilege separation
Privilege levels act as checks against controlled use of application functionality on the need to know basis. Your SaaS product (applications and infrastructure) should implement multiple levels of privilege (based on functionality) to enforce the separation of privileges between different user accounts, groups or customer bases of an organisation. It should also be acted at the network level, e.g. Network Security Groups (NSG) changes should not be available to large groups without a change approval process.
Logging and auditing
Logging and auditing is a critical element of a good security strategy. You should ensure that the SaaS provider implements useful logging and auditing policy, providing a granular view of resource logs and events. These applications and network logs should be available to customers, especially since security event logs access is essential to customers’ security and confidence in the cloud provider. Cloud services generate a lot of data. It is necessary to consider which cloud services and properties are worth logging in because log storage and analysis are resource-consuming tasks.
Incident response
Preparation is vital when it comes to cyber-attacks. Apologies in advance, but I have to include this famous saying it’s no longer a question of ‘if’; it’s a matter of ‘when’. Questioning the vendor over how they dealt with incident response matters in case of a past event or their process would be a useful metric. SaaS vendor should have a well-defined incident response policy dealing with cloud security incidents.
Conclusion
The above-listed SaaS audit checklist contains practices that are sure to help assess security properties. It’s worth pointing out that this is not an extensive list to rely on because, ultimately, your organisations’ risk management identifies more and precise security requirements. Network security, hosting, third-party extensions and libraries also play an essential role in protecting SaaS applications’ supporting infrastructure and services. For instance, PCI DSS, GDPR and other organisations’ requirements may add another dimension to ensure your providers adhere to a minimum set of requirements.
Get in touch for free advice or discuss your SaaS cloud security concerns.