Managed Vulnerability Scanning Service
Our managed vulnerability scanning services help you to identify new vulnerabilities and misconfigurations across your networks and applications. This is a fundamental component of the security manual penetration testing program ensuring continuous checks to help remediate security risks and achieve a strong cyber security posture.
Get in touch











Vulnerabilities identified by our scanning service
Managed vulnerability scanning aims to identify security vulnerabilities affecting an organisation. It provides input to the managed vulnerability assessment process, where vulnerabilities are assessed and categorised in terms of actual risk to the organisation. Managed vulnerability scanning is a vital component of a cyber security testing program offering constant identification of new vulnerabilities in IT systems.
The issues discovered are presented in easy-to-understand formats with actionable guidance. This input is essential to quantify and categorise risks before approaching risk remediation.
A specialist-managed vulnerability scanning solution offers constant checking, and our consultant’s expertise offers a handy approach to tactical risk remediation rather than getting consumed by a lengthy report and large volumes of scan data.
A good security partner is more than a ‘point and click scan’; they help you to avoid:
- Risk – Reduce the noise that is unnecessary and adds to the chaos
- False alarms – Untrusted data that’s not a finding
- Confusion – Ambiguous data that must be reviewed.
See what people are saying about us


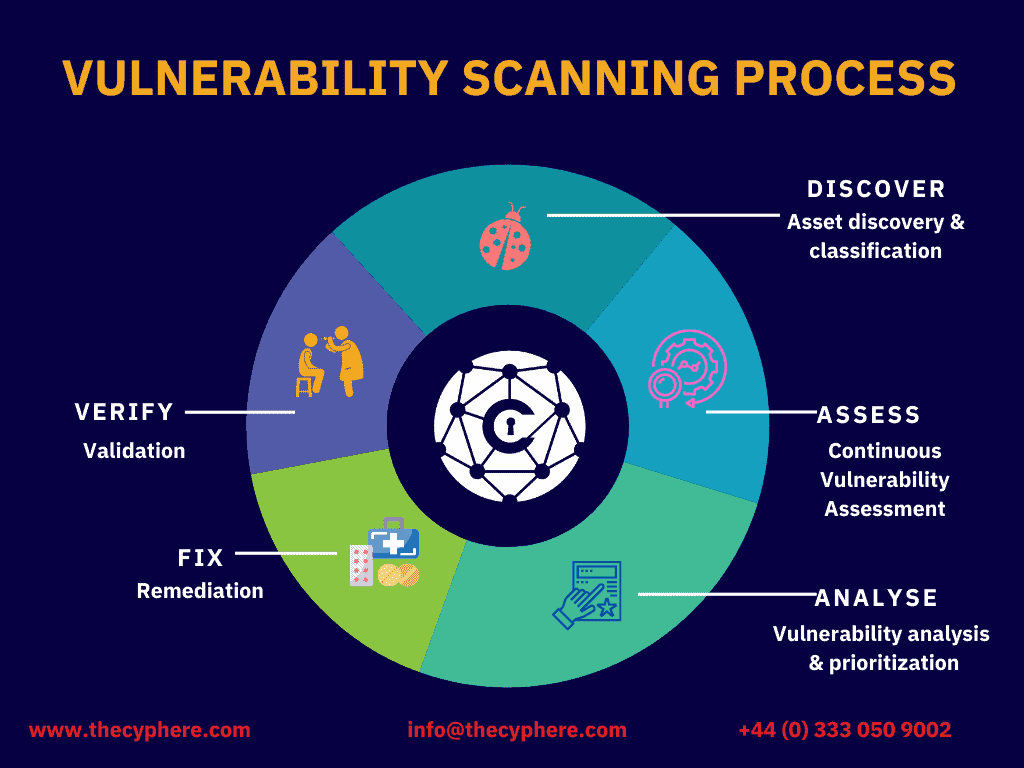
What is Managed Vulnerability Scanning Service process?
The main objective of managed vulnerability regularly scanning is to provide constant insight into vulnerabilities and misconfigurations on an ongoing monitoring basis.
Managed Vulnerability assessment is a component of vulnerability management that is a time-limited exercise aimed at finding vulnerabilities in your cloud environments. A managed vulnerability scan is an ongoing process that is more comprehensive and aimed at continuous identification and identifies security weaknesses.
The managed vulnerability scanning tools consist of thousands of checks and signatures used to probe open ports and vulnerability scanning services, collect information and discover comprehensive coverage of vulnerabilities that threat actors could use.
The presence of false positives is a downside to this process, which is taken care of by adding a human edge to the process where all issues are manually checked against the targets in scope. Problems range from simple information leakage to broken access controls or a lack of essential patches.
Vulnerability management service is broadly divided into two main categories, i.e. Network vulnerability scanning and Web applications vulnerability scanning. This vulnerability scanner identifies issues related to services in an internal network (inside a perimeter) or over the internet (external) across operating systems and services. Vulnerability scanners exist for several specialist subcategories, such as cloud infrastructure, because misconfiguration of cloud platforms is the number one threat to cloud security.
An internal vulnerability could be exposure of database to the entire company, an open share, etc. A web application vulnerability scanning detects exploitable vulnerabilities across the application components, such as checking against OWASP Top 10 application and API security issues.
The vulnerability scanning process takes in all your known software vulnerabilities and feeds them into the risk exposure remediation process, making it an effective way to assess risks for a business.
When you make the mistake of buying vulnerability scans disguised as assessment, it’s not really a vulnerability scanning in your business context – it’s not a highly specialised software tool, it will provide scan results with no expertise or insight on how these could affect us if they were exploited by cybercriminals.
An ultimate guide to Vulnerability Scanning
Vulnerabilities identified by our scanning service

Why choose Cyphere as your penetration testing service provider?

Excellent people to work with.
Very good knowledge of requirement and give us correct findings with excellent remedy to improve our security for our B2B portal site.
Harman was great, really knowledgeable
Harman was great, really knowledgeable, helpful and on hand to answer any questions. The final report was very clear providing the technical information in an easy to read format which could be understood by the leaders of the business.
My experience of the team was 5 star.
They were so helpful, and their technical delivery and client communication were excellent.
Extremely satisfied
Extremely satisfied with approach, speed and end results. Thanks.
YOUR TRUSTED CYBER SECURITY PARTNER
Why Cyphere Managed Vulnerability Scanning?
- Prioritise and assess the newly identified assets
- Maximising in-house team efficiency to focus on addressing than discovering risks
- PCI DSS, ISO 27001, GDPR Compliance support
- Gain continuous visibility of your assets across the estate
- Constant support for risk remediation from security experts
- Good cyber hygiene with reduced risk exposure
Benefits of managed vulnerability scanning
- Reduced risk of attack
- Faster identification and remediation of vulnerabilities
- Improved compliance posture
- Greater visibility into the security posture
- Increased efficiency in vulnerability management processes.
New remediate vulnerabilities are continually emerging, this can leave organisations exposed to emerging issues in the window between tests. When it comes to protecting your organisation from cyberattacks, managed vulnerability scanning is a critical piece of the puzzle.
By identifying and remediating vulnerabilities in a timely manner through vulnerability management services, you can reduce the risk of an attack and improve your organisation’s compliance posture.

