What is encryption?
Encryption is the process of converting plaintext data into an alternative form known as ciphertext. However, only authorised users can decipher the ciphertext back into clear-text to access the information.
There are two types of encryption in widespread use, i.e. symmetric and asymmetric encryption. These names symbolise whether the same key can be used for encryption and decryption processes. These two terms: Encryption and cryptography, are often used interchangeably. We have dedicated an entire topic to hashing, encryption and salting with examples.
A simple explainer:
- Public key – It is just like your bank account number. You can share this with anyone.
- Private key – It is like your ATM PIN. You should not share this with anyone.
Symmetric encryption vs asymmetric encryption
It is important to understand the differences between symmetric and asymmetric encryption processes. To start with, we will explain the basics and then advantages and disadvantages along with asymmetric and symmetric encryption example.
What is symmetric encryption?
Symmetric encryption is the process of converting plaintext into ciphertext and vice versa using the same key. An encryption key is a random string of bits used to encrypt or decrypt data. It is, therefore, important that key is transferred between the sender and recipient using secure methods.
RC4, RC5, RC6, IDEA, Blowfish, AES, DES and 3DES are symmetric encryption algorithms.

Advantages of symmetric encryption
One main advantage of symmetric encryption is its speed because keys are much shorter, and the overall process is quicker.
Disadvantages of symmetric encryption
One main disadvantage of using symmetric encryption is using the same key. This key is shared between the sender and recipient. It adds to overheads such as secure storage of key and keeping it secure during transmission.
symmetric encryption example and use case
- Data storage, for instance, data at rest such as laptop disk drives, USB that is not moving and stored in one place, is often encrypted using symmetric encryption. Full disk encryption software work on this concept where a user’s secret key is generated to encrypt disk volumes and can only be decrypted when the key is provided.
- Payment information such as credit card numbers, PII or other sensitive information in databases is encrypted using symmetric cryptography.
What is asymmetric encryption?
Asymmetric encryption, also known as public-key cryptography, uses the concept of a key pair. The sender and the recipient use a pair of keys, i.e. a private key and a public key during the encryption and decryption process. It works like this:
- Private keys are kept secret by the senders and recipients to encrypt/decrypt messages.
- Only public keys are shared across the public at large.
- The private key and public key pairs are mathematically related to each other, but you cannot generate the private key using a public key.
Asymmetric encryption algorithms examples include RSA, Diffie-Hellman, ECC and DSA.

Advantages of asymmetric encryption
Asymmetric encryption is considered more secure as it does not involves sharing of keys. A user never reveals or shares their private key.
Disadvantages of asymmetric encryption
It takes more time than symmetric encryption, tends to be a slower process. However, this is not a huge drawback and is used widely to encrypt data where security is the primary concern.
Asymmetric encryption example and use case
- Public key infrastructure (PKI) – It is everything relates to governing encryption using digital certificates and management of public-key encryption.
- Cryptocurrency is finding the primary use of asymmetric encryption through blockchains to authorize transactions and confirm identities. Public key cryptography is a major component of Bitcoin’s protocol, utilising Elliptic Curve Digital Signature Algorithm (ECDSA).
- Digital signatures help with confirming identities using asymmetric encryption.
Everything you need to know about PKI:
What is the difference between encrypting and signing in asymmetric encryption?
Encryption in public-key cryptography uses someone’s public key to encrypt a message and recipient can see the message using their private key.
Signing is related to verification to ensure it’s really the right sender who has sent the message. For instance, when signing, you use your private key to compose a message and the recipient using your public key to verify it’s indeed sent by you.
Combining symmetric and asymmetric encryption
Many applications take advantage of the combination of symmetric and asymmetric encryption together. When both, symmetric key and asymmetric key cryptography, are combined, it most likely follows this methodology:
- The plaintext is encrypted to ciphertext utilising symmetric encryption to make use of speed.
- Asymmetric encryption is used for keys exchange used for symmetric encryption. This ensures the security of asymmetric cryptography, making sure only the intended recipient can perform decryption.
Common examples include SSL/TLS connections and messaging applications such as Signal, Whatsapp that use end-to-end encryption to prevent third-parties and application vendor from accessing calls or messages. Here, asymmetric encryption is used to establish the encrypted communication between the two users, and symmetric encryption is used for communication duration.
What is hashing?
Hashing is a one-way function (say algorithm) used to calculate a fix size value from the input. Hashing is meant to verify data integrity (a file, properties of a file, piece of data, etc.) that it is authentic. Hashing is quite often wrongly referred to as an encryption method.
Top encryption mistakes to avoid
Inadequate keys management, encryption misconfiguration, insecure storage practices are some of the key risks when it comes to encryption practices. A business must understand the power of cryptography when done right. Therefore, a third party validation exercise must be performed to ensure no gaps in your security controls responsible for protecting your most prized assets. Applications utilising a reversible form of encryption to store sensitive information is a high-risk scenario at the web application layer. It could be internal cryptography gateway, your database storage mechanisms, your external websites serving customers or cloud encryption keys management.
Here are the top encryption mistakes that pose threat to any environment:
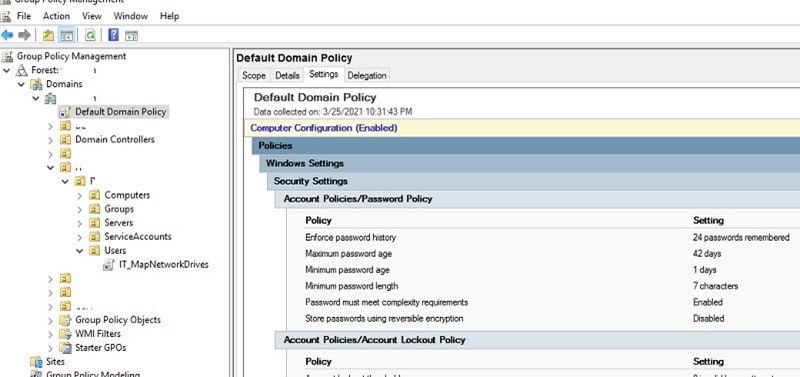
- Insecure encryption configurations
- Insecure key management
- Relying on your developers without third party validation
- Compliance means ‘secure’
- Relying on cloud provider to handle your crypto
- Low-level encryption solves your data at rest crypto
Conclusion
There is no one method to rule all, both symmetric and asymmetric encryption concepts are important and have practical uses. The above sections covering definitions, examples, advantages and disadvantages should help you with the basics.
Both the cryptographic processes are important and used in combination, as mentioned earlier. Encryption configuration must be secure from flaws , at the least above mentioned top mistakes, that would put users information or communication at risk.
Get in touch to discuss your security concerns or to review your internal or external encryption configuration.
Harman Singh is a security professional with over 15 years of consulting experience in both public and private sectors.
As the Managing Consultant at Cyphere, he provides cyber security services to retailers, fintech companies, SaaS providers, housing and social care, construction and more. Harman specialises in technical risk assessments, penetration testing and security strategy.
He regularly speaks at industry events, has been a trainer at prestigious conferences such as Black Hat and shares his expertise on topics such as ‘less is more’ when it comes to cybersecurity. He is a strong advocate for ensuring cyber security as an enabler for business growth.
In addition to his consultancy work, Harman is an active blogger and author who has written articles for Infosecurity Magazine, VentureBeat and other websites.