
Cyber security KPI or other Key Performance Indicators are established in different areas of every organisation to track and monitor the progress towards attaining a certain goal or target. Cybersecurity is no exception here, and companies should maintain proper cybersecurity KPIs. There are many blog posts available around this topic but in this article, we have gathered a list of important cybersecurity KPIs that every organisation should consider.
How many KPIs should be there?
Determining the number of KPIs a company should have is directly related to the goals and targets set by the organisation itself. Once the goals are identified the KPIs will become evident. Nobody other than the organisation itself can determine how many KPIs they need.
However, when creating KPI, priority should be defined to each KPI such as categorising them as Priority KPIs i.e. these indicators are vital in the cybersecurity program of the company and Relative KPIs i.e. these indicators matter but do not play a crucial role.
Creating an effective KPI
KPIs can be thought of as benchmarks, and when creating these benchmarks make sure that they are measurable. An effective KPI is one that is:
- Simple i.e. easy to understand,
- Actionable i.e. steps can be taken to achieve the KPI,
- Measurable i.e. it can be quantified,
- Relevant i.e. it pertains to the security program and
- Time-based i.e. the KPI can be achieved within a defined time limit.

Why KPIs are important in cyber security
Information security is an ever-growing field where the threat landscape, offensive and defensive mechanisms, techniques and tactics are evolving every day. It is crucial for an organisation to stay ahead of the threat actors and protect the organisation’s assets.
By keeping a set of well defined KPIs the organisation can improve their overall security posture, measure the progress made in its security program and make decisions based on its growth.
Reporting the cybersecurity issues, concerns and developments to the board members also become easier when there are quantifiable numbers to back up the statements.
Cybersecurity metrics (KPIs) to track
Below are some of the major cyber security metrics (KPIs) and best practices that an organisation should keep track of:
Preparedness level
The overall preparedness of an organisation should be quantified such as against the Top 20 CIS controls. This will give a holistic view of the security posture and the cybersecurity efforts made by the organisation.
Meantime between failures (MTBF)
The time taken in between system or product failures should be recorded to detect the problems and issues within the system.

Meantime to detect (MTTD) and mean time to acknowledge (MTTA)
The time taken for the security team to detect a cyber attack or data breach should be recorded. This also identifies how long the attack went unnoticed.
The time to acknowledge should also be recorded which will reflect the amount of time taken from the detection phase to responding to the attack.
Meantime to resolve (MTTR) and mean time to recovery (MTTR)
The mean response time of any security incident should be recorded to know how much time the team takes to respond to a cyber attack after they become aware of this. The mean time to contain (MTTC) can also be calculated at this stage.
And if the cyber attack causes system failure or downtime, what is the team’s time to resolve these issues. Both these measures should be as minimal as possible.
Number of unidentified devices
The number of unidentified devices on the internal network should be monitored to ensure that no employee or third party connects any unauthorised devices within the network, as this can lead to introducing malware and other risks.
Number of intrusions in the IT environment
The number of times any intrusion attack or intrusion attempt takes place on any system should be recorded by the security operations center (SOC). This is show the attempted cyber attacks and unauthorised accesses that took place.

Number of days for patching
The number of days it takes the IT department to deploy patch releases or update any vulnerable system should be recorded. This will give a clear window or timeline in which the company is at risk of attack because of vulnerable systems.
Number of cybersecurity incidents reported
The total number of cyber security incidents should be recorded as well as the number of times the employees report security incidents or suspicious activities. This shows that the employees are becoming aware of security threats.
Number of days take to deactivate unused/former employee credentials
This metric will help ensure if the IT and HR departments are working in sync. Ideally an employee’s access and accounts should be deactivated immediately after their departure. Failure to do so might lead to sensitive data exposure and difficulties in forensic investigations.
Number of systems with known vulnerabilities
When a company knows the number of its vulnerable assets, it can determine the risk exposure/data affected and act accordingly. Since the risk indicators are already known, the company knows how to handle them in such cases, such as patching, updating or replacing the asset.
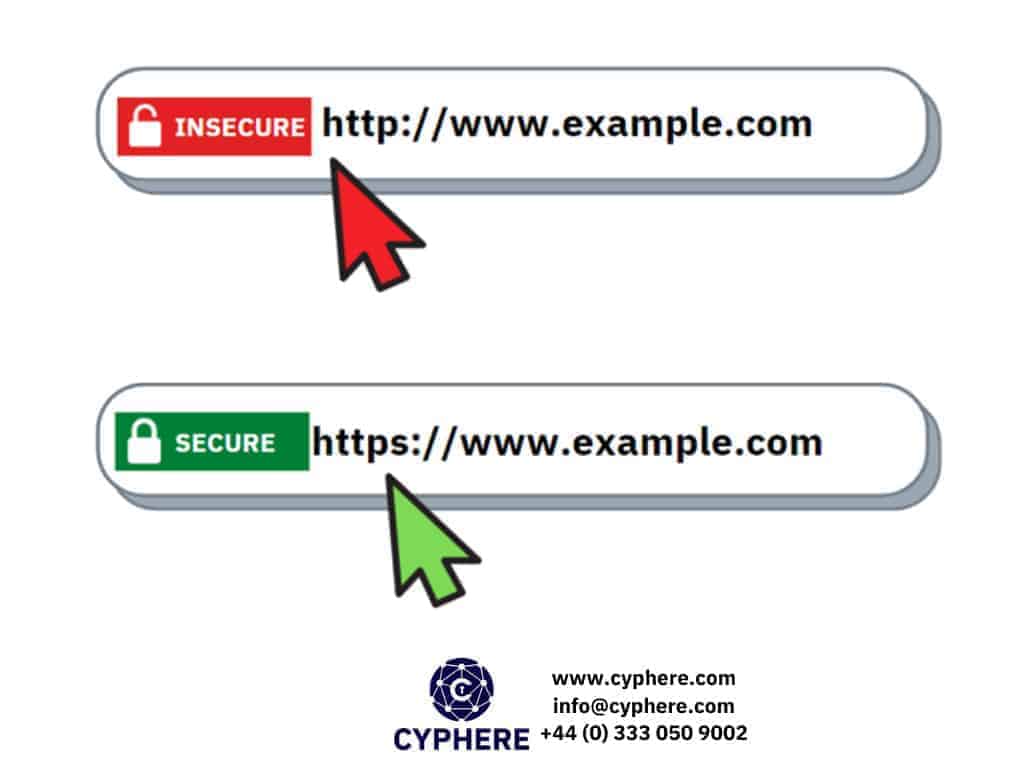
Number of incorrectly configured SSL certificates
SSL certificates are necessary to ensure the company’s digital identity and secure transfer of information. The company should monitor and keep track of all certificates and reconfigure them where needed.
Number of cybersecurity awareness training sessions conducted
The company should track the number of security training sessions they conduct each year. Employees should be well versed in basic security practices and what to do in case of a security incident.
Cybersecurity awareness training results
After conducting cybersecurity awareness sessions the organisation should keep track of the number of attendees as well as if the attendees understood the content completely.
Access management
This security performance KPI ensures that access to critical systems is monitored, access control is granted on the basis of the principle of least privilege, and monitoring the individuals with administrative privileges.

Adhering to security compliance
If any security compliance such as ISO 27001, HIPAA, FISMA, GDPR etc. is applicable to the organisations are they compliant to the requirements and tracking, documenting, configuring systems accordingly?
Amount of non-human traffic (NHT)
Is the monitored traffic normal (with respect to amount, type of packets etc.) or does the traffic indicate malicious activities such as a potential botnet attack?
Monitoring virus infections
This KPI includes the quantity of malware or virus infections that took place. As well as the frequency of detection by the antivirus software. This KPI may also include the areas that the antivirus is scanning malware such as emails, laptops, servers etc.
Results for successful phishing attacks
This security KPI can cover two aspects, firstly if the company conducts phishing simulation tests so what are the results of those tests i.e., how many employees became victims of the attack simulations and how many reported the phishing email/call to the IT department.
Secondly, this covers the legitimate phishing attacks on the company employees and how many of those attacks were successful.
The cost incurred per incident
This KPI informs the higher security management what the cost of resolving and responding to a cyber incident will be. This includes the money that will be spent on the staff, investigation cost, downtime cost, communication with customers, any fines or penalties, replacement of systems etc.

Frequency of review of third-party accesses
More often than not third party vendors are granted access inside the IT infrastructure to carry out certain tasks. The frequency of these access along with monitoring whether this access is revoked after the activity is completed is crucial in protecting the company assets from unauthorised access. Failure to do so may lead to data exfiltration or other malicious activities.
Frequency of access to critical systems
Access to critical systems should always be monitored to ensure no unauthorised access takes place and tracking is possible in case of any incident. This will also indicate if any misconduct or attempts to access sensitive systems is made by an employee or if the systems are compromised.
Quantity and volume of data transferred via corporate network
When employees are given unrestricted access to the internet using the corporate network it is important to monitor the volume and quantity of traffic, so that it is easier to identify any misuse of the company’s resources. Furthermore it will be possible to track if employees are downloading prohibited software, streaming videos etc.

Conclusion
Without effective and efficient KPIs it will not be possible for business to carry out informed decision making about their security efforts, goals, requirements and progress. A quantifiable value is necessary to ensure that everything is going according to plan, not to mention that facts and numbers are more understandable for C-suite executives.
Always try to set relevant KPIs regarding your cybersecurity performance so you would have a clear view of what is done and what needs to be done.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.












