Policies and procedures are an integral part of an organisation. They determine the company’s culture, beliefs, norms, and expectations, thus they must be carefully drafted and regularly updated.
Effective policy management prevents your company from being held back by outdated, inaccessible policies that people just forget about.
When it comes to information security, having the correct information security or cyber security policies is crucial. Inappropriate usage of corporate networks and devices can result in malware infection, data breaches, or damage to the organisation’s reputation. Only the correct information security policies can help decrease the risk and likelihood of an incident and protect the business information from being compromised.
However, having policies in place for information systems and business processes is insufficient to improve security posture. It is a waste of time to proceed without first ensuring that these information security policies are clear and accessible to your users. This implies they should be free of jargon, concise yet with all important information, and easily accessible for subsequent reference.
This blog post will examine what information security policies are, how to guarantee they are effective in increasing security, and how to maintain compliance and effectiveness.
What constitutes a good information security policy?
Many organisations have security policies that are both technological and legalese. A commonly held belief regarding information security policies is that they exist to protect the organisation from litigation or to free it of liability in situations of employee misconduct.
A good information security policy is simple, without jargon or legalese, and genuinely changes employees’ behaviour. It’s also critical that staff grasp the policy’s goals. Employees who don’t grasp a policy’s purpose are more likely to ignore it, and those who don’t bother reading it won’t even know what it says.
An effective information security policy must meet these three criteria:
- The policy must be clear and include definitions of technical terms
- The policy must be well tested against information risks
- Legal and regulatory criteria must be met.
Preparatory phase to draft a good information security policy?
Making a policy that succeeds requires knowing what you want it to achieve. You should verify that every aspect of the policy has a valid justification for being there and that you can monitor and enforce it.
Ambiguous wording in policy text should be avoided, although basic statements on the policy’s purpose and scope are permissible.
Follow these steps while preparing for the policy draft:
- Set a clear goal for the policy.
- Define who and what the policy applies to.
- Decide the policy’s actual substance
- Describe how you will enforce and penalise non-compliance.
What should an information security policy cover?
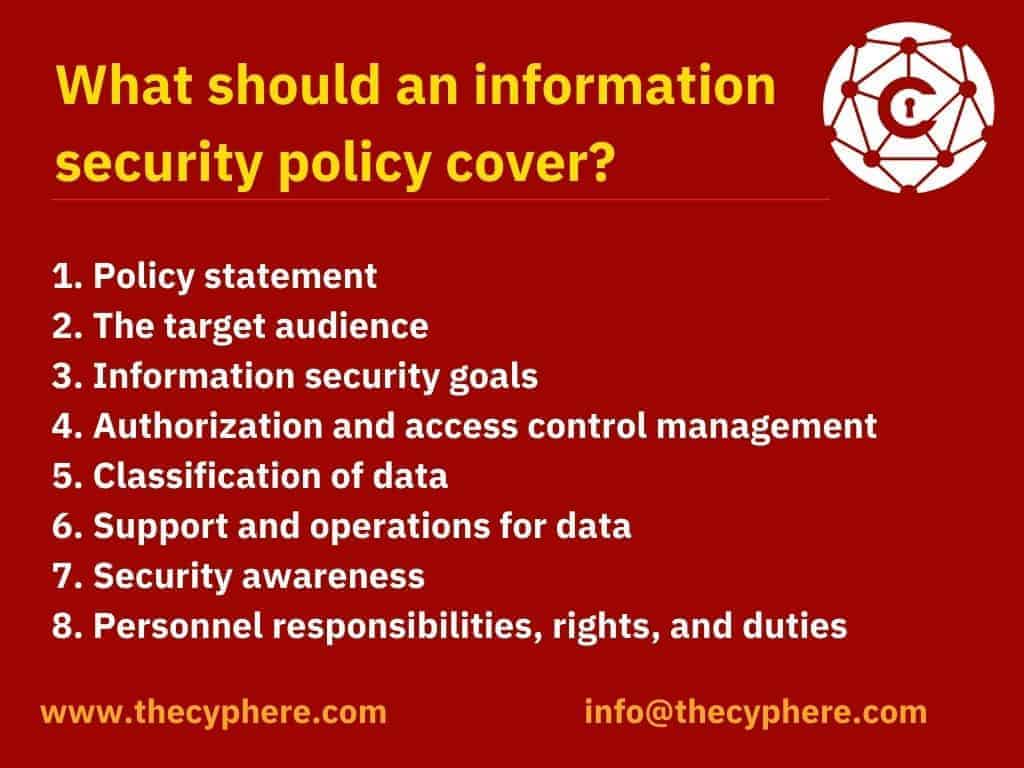
To keep readers interested, effective policies should avoid seeming too much like policies. A correct structure, however, ensures that readers know where to look for information and that you have typed down all relevant information.
A good information security policies have the following eight elements:
1. Policy statement
First, state the policy’s aim, which might be to:
- Create a comprehensive strategy for information security.
- Detect and prevent information security breaches, such as the abuse of networks, data, applications, and IT assets.
- Maintain the organization’s reputation while adhering to ethical and legal obligations.
- Customer rights must be respected, including how to respond to questions and complaints regarding noncompliance.
2. The target audience
Define the target audience for the information security policy. You can also select which audiences are not covered by the policy (for example, staff in another business unit that manages security separately may not be in the scope of the policy).
3. Information security goals
Assist your management team in developing well-defined strategy and security program. The primary goals of information security are as follows:
- Confidentiality- only authorised personnel should have access to data and information assets.
- Integrity – data must be intact, correct, and comprehensive, and IT systems must remain operating.
- Availability – when needed, users should be able to access information or systems.
4. Authorisation and access control management
A senior manager may have the ability to select what information may and cannot be shared and with whom. A senior manager’s security policy may differ from that of a junior employee. The policy should specify all the privilege and administrative access lists for data and IT systems.
Users can only access business networks and servers through unique logins that require authentication, such as passwords, biometrics, ID cards, or tokens. All systems should be monitored and all login attempts should be recorded.
5. Classification of data
The policy should classify data into categories such as “restrictive,” “sensitive,” “confidential,” and “public.” Your goal in data classification is:
- To prevent those with lesser security and privacy awareness from accessing sensitive information.
- To safeguard critical information while avoiding unnecessary security procedures for non-sensitive information.
- To protect data by deploying security controls for confidential or sensitive information.
6. Support and operations for data
Data protection legislation—systems that hold personal data or other sensitive data must be safeguarded in accordance with organisational security standards, best practises, industry compliance requirements, and applicable regulations. Most security requirements demand encryption, a firewall, and protection against different types of malware as a bare minimum.
Data backup—encrypt backup information in accordance with industry standard practices. Backup media should be securely stored, or backups should be moved to secure cloud storage.
Data transmission—only use secure methods to send protected information. Encrypt any data copied to portable devices or sent over a public network.
7. Security awareness
Inform your employees about IT security regulations. Conduct training sessions and security programs to tell the staff about your security controls and mechanisms, such as data protection, access control, and sensitive information classification.
Social engineering—emphasize the hazards of social engineering attacks (such as phishing emails). Employees should be held accountable for detecting, preventing, and reporting such attempts.
Acceptable Internet usage policy—define how access to the Internet should be limited. Do you allow YouTube and other social media websites? Using a proxy, you may block undesirable websites.
8. Personnel responsibilities, rights, and duties
Appoint staff to conduct user access reviews, education, change management, incident management, implementation, and periodic updates of the security policy. Responsibilities should be clearly defined as part of the security policy.
List of common information security policies
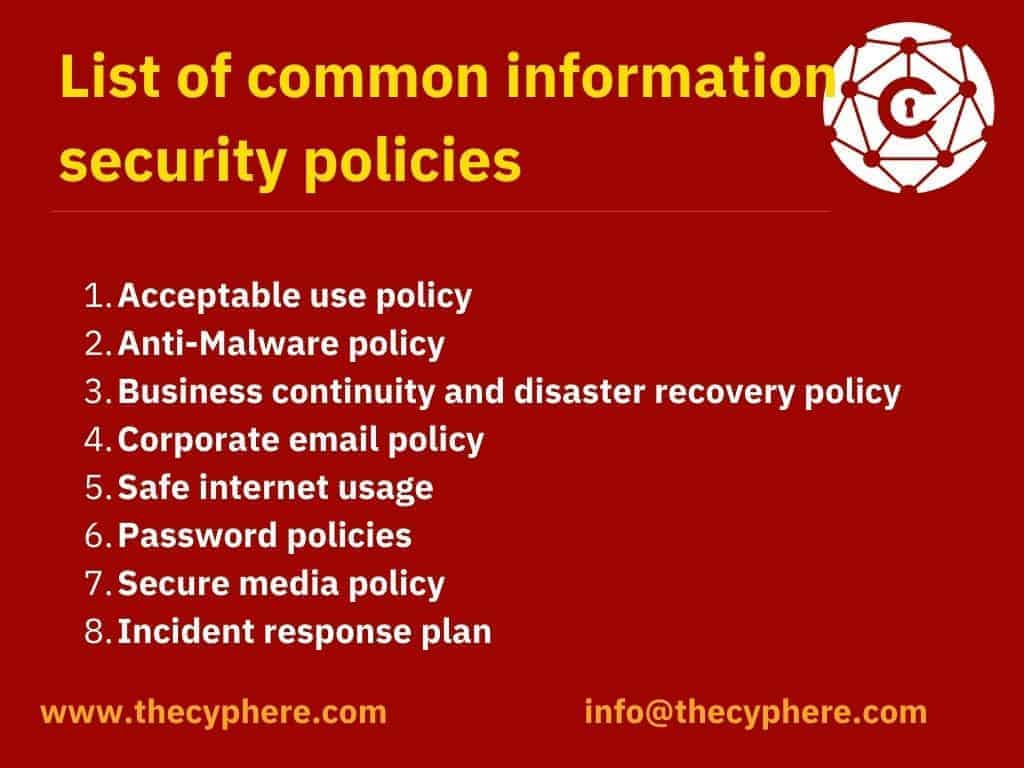
Some popular information security policies and procedures include:
Acceptable use policy
An Acceptable Use Policy governs computer usage. Every organisation with employees that use corporate devices or access company networks should have one.
This policy should explicitly define acceptable (job-related) and forbidden (personal) use of compnay devices and networks (violent, offensive and illegal content, as well as anything that could damage the company, its customers or other employees).
Anti-Malware policy
An Anti-Malware policy protects a computer system from malware by defining its use. This typically means keeping anti-virus software up to date and not opening unusual email attachments. Even though these responsibilities are generally conducted by the IT Department, it is crucial to keep users actively involved in security concerns to ensure the business’s continuous security.
Business continuity and disaster recovery policy
Business continuity and disaster recovery are receiving more attention than ever before. Every organisation, from small businesses to major corporations, is increasingly reliant on digital technology to generate income, deliver services, and support consumers who demand apps and data to be available at all times.
The business continuity and disaster recovery’s purpose is to reduce the impact of outages and interruptions on company operations. This policy practice allows an organisation to get back on its feet if a crisis occurs, reduces the danger of information loss and reputational harm, and improves operations while lowering the likelihood of an incident.
Corporate email policy
Email is the major mode of communication in most businesses, however, it must not be misused to reveal information or harm the company’s reputation. An email policy governs the usage of workplace email accounts.
Safe internet usage
It is still crucial to prevent the danger of inappropriate internet use from affecting your organisation, even though it has become a standard in many firms. Internet security policies define permitted and banned uses of the internet in the workplace, and ensure users take adequate actions to secure themselves and their equipment when online.
Password policies
Insecure password use is a common source of breaches. Employees must understand the necessity of using safe passwords, and your company must discipline non-compliance. A password policy defines the criteria for safe passwords, how passwords are saved and communicated, and the consequences for non-compliance.
Secure media policy
USB drives, for example, might create data breaches or malware infections on workplace systems. For example, a secure media policy may state that unaccounted-for or found-around-the-workplace USB devices may not be plugged into corporate computers (they could have been left behind by cybercriminals and contain malware).
Incident response plan
Almost every company will encounter a security breach. When a breach occurs, it is critical that roles and responsibilities are clearly articulated. An information security incident response plan outlines how to prepare for a security incident and what to do in the event of one.
What is a policy management system?
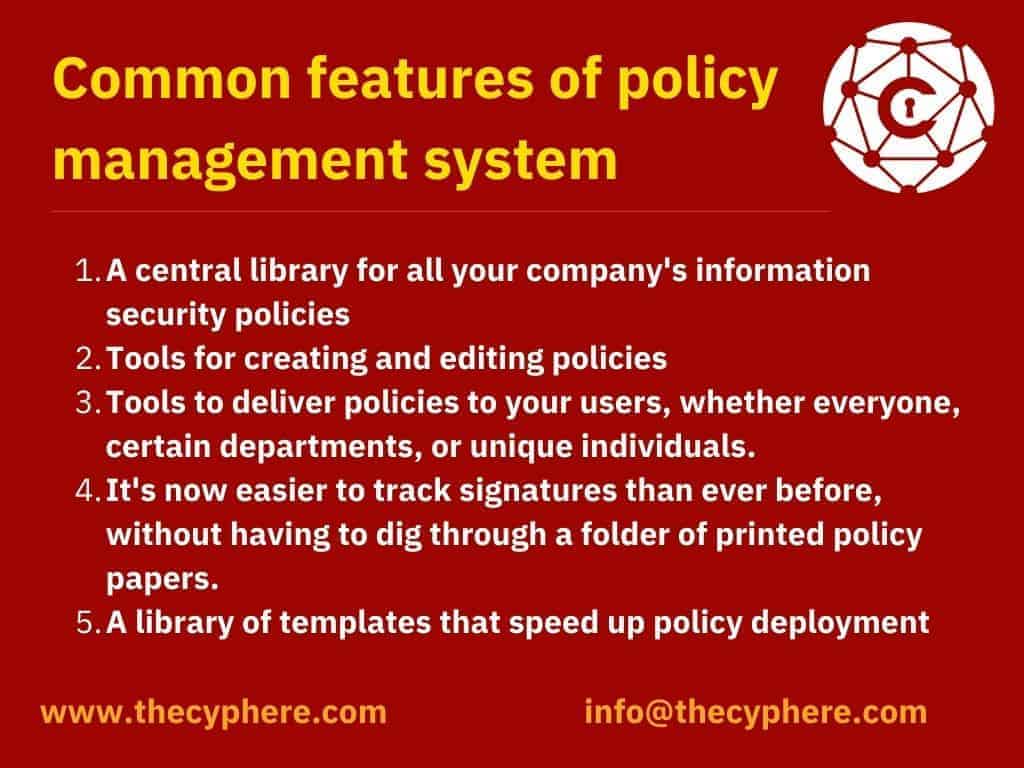
A policy management system centralises all of your organisation security policies. This simplifies amending, transmitting, and tracking all of your company’s rules and procedures, reducing administrative time.
Among the common aspects of an IT policy management system are:
- A central library for all your company’s information security policies
- Tools for creating and editing policies
- Tools to deliver policies to your users, whether everyone, certain departments, or unique individuals.
- It’s now easier to track signatures than ever before, without having to dig through a folder of printed policy papers.
- A library of templates that speed up policy deployment
Some best practices for writing security policies
Classification of data – may make or break your security operation. Incorrect data classification may expose your systems to attack. Inefficient resource management may also result in overhead costs. Clear data classification helps businesses oversee security asset distribution.
IT operations and security – should collaborate to fulfil compliance and security goals. Departmental discord might lead to setup issues. Teams can lower risks by coordinating risk assessment and identification across departments.
Security incident response –strategy assists in initiating appropriate remedial activities. A security incident plan guides initial threat response, priority setting, and suitable repairs.
Cloud and SaaS procedures – set explicit adoption rules for a unified cloud environment. This strategy can reduce wasteful complexity and poor cloud resource utilisation.
Acceptable use – helps avoid data breaches caused by misuse of organisational resources. Transparent AUPs help all employees utilise corporate technology properly.
Identity and access management (IAM) policies – allow IT managers to provide access to systems and apps and educate staff on password security. A basic password policy can help protect identity and access.
Data security policy – defines the organization’s technical operations and permitted usage guidelines for PCI DSS compliance.
Regulations – like the General Data Protection Regulation (GDPR) safeguard consumers’ privacy. Organisations that do not respect user privacy risk losing power and being punished.
Mobile devices management – companies that allow employees to access company information assets from personal devices like laptops and cellphones risk creating risks. Creating a policy for personal device security can assist protect against attacks.
How Cyphere can help you?
Cyphere helps you to administer information security policies for your organisation and provide a collection of information security policy templates that can be implemented across the organisation.
Get in touch to draft your cyber security or information security policies and procedures with cyber security services provider like Cyphere.
Shahrukh, is a passionate cyber security analyst and researcher who loves to write technical blogs on different cyber security topics. He holds a Masters degree in Information Security, an OSCP and has a strong technical skillset in offensive security.