Cybersecurity issues in healthcare relate to the safety of hospitals and healthcare service providers’ clinical and administrative information systems. In the last few years, increasing healthcare cyber attacks have been faster than the improvements in IT security controls. This article discusses the top security risks affecting hospitals and healthcare providers, followed by the best security practices aimed at improvements. Many of these issues we have observed during internal penetration testing work for our customers – are applicable whether it is NHS DTAC requirement, proactive assessment or other compliance-led penetration testing exercise.
Cybercriminals quickly adapt to the world around them. For example, during 2020, cybercriminals targeted the healthcare sector with pandemic-themed malicious campaigns. It resulted in data breaches and ransomware attacks disrupting business operations. This industry experiences one of the highest numbers of data breaches annually.
Watch this video to learn about the most significant cybersecurity concerns for healthcare providers:
Watch this video to learn about security best practices for healthcare providers
Cyber security for healthcare – Complexities
Constant activity 24x7x365 within healthcare organisations is inherent to their operating procedures. This organisational complexity adds to the IT operations where devices, equipment and systems require communication with external systems. This extensive mesh of networks & systems, including medical equipment, adds to the complexity of securing the most prized catch for cybercriminals: clinical data.
Data sharing and digital health records sharing between the departments or other units such as surgery centres, facilities, labs, staff stations, patient rooms, pharmacies and external suppliers (third party) are at organisations’ core. Adding MedTech evolution and cloud connectivity to this mix further complicates matters in data collection for various purposes. It expands the boundary of trust by default, and the technical controls needing grip over logical boundaries in a network lack the validation exercise. A good cyber security strategy helps organisations define these boundaries between trusted and untrusted territories, including layered checks, before deciding who can access what information. Read here how data protection is essential in health and social care.
Healthcare security is a vital component to keep businesses going.
How are attackers compromising hospitals and healthcare networks?
In the underground markets (sometimes referred to as darkweb), Public health Information (PHI) data sells at higher prices compared to PII (Personal Identifiable Information), making it a lucrative opportunity for Cybercriminals. It is one of the reasons the healthcare industry is now the biggest target for cyber attacks.
Apart from phishing campaigns, almost all the attack vectors utilised by cybercriminals target the internet-facing digital assets of an organisation. Attackers target vulnerable and unmonitored internet-facing assets to quickly gain a foothold on the healthcare organisations’ network. This makes it easier to connect and carry out further activities per various CKC stages.
In recent years, the following weaknesses have been exploited heavily by organised crime groups:
- Remote Desktop Protocol (RDP) or Virtual Desktop endpoints
- Insecure configuration of web servers, system management, Electronic Health Record (EHR) software
- Trivial or weak authentication mechanisms such as weak passwords, flawed authentication implementations
- Remote connectivity software product vulnerabilities
- Unsupported platforms, such as Windows Server 2003 Windows Server 2008, with weakened security due to the wrong choice of passwords
- Other interesting avenues for attackers during 2020 are vulnerable Microsoft SharePoint servers (CVE-2019-0604), Microsoft Exchange servers (CVE-2020-0688) & Zoho ManageEngine (CVE-2020-10189).
Who poses the most significant security threats to healthcare information systems?
- Foreign Intelligence Agencies have offensive security capabilities and may also seek to compromise healthcare information systems to exfiltrate research data, such as the issued APT29 cybercrime group targeting COVID-19 vaccine development efforts globally.
- Insider threats come from employees who may be >negligent, unintentional or problematic insiders.
- Phishing attacks utilising phishing and spam emails (unsolicited emails with false and hidden information) aimed at stealing sensitive patient information and for monetary gains
- Cybercrime groups carry out targeted campaigns using social engineering attack techniques to commit identity frauds
- Bot-network operators control vulnerable system access and trade it illegally on the darkweb for monetary gains that, in turn are used for Denial of Service (DoS) attacks, phishing or relaying spam emails.
- Espionage at the industrial, staff or nation-state level to gain a competitive edge.
Most significant security threats in healthcare
The attack surface of healthcare organisations is beyond handling phishing or ransomware threats within their organisation. Cyber security risks in healthcare involve greater scope, including personnel, digital assets and technologies.
Pandemic-themed attacks – rise in phishing and ransomware.
It is amongst the emerging security threats in healthcare information systems, especially gaining momentum during 2020. During the coronavirus crisis, there has been increased cybercrime activity across hospitals and the sector. Cybercriminals have been cashing in using phishing and ransomware attacks on hospitals, leading to downtimes affecting patient care. At a higher level, the main subjects exploited are:
- Demand for goods such as PPE, disinfectants, and masks.
- Vaccine trials, medicine and related factors
- Increased reliance on internet-based connectivity such as teleworking, buying/selling goods
The underlying pattern of these campaigns remains exploitation of increased fear, uncertainty and doubt factor in the general population.
Ransomware attacks are paralysing hospital networks around the globe. These ransomware campaigns include RobbinHood, Maze, PonyFinal, REvil, and NetWalker ransomware affecting organisations globally. Precisely, during the pandemic hit 2020, Cybercriminals have been trying to cash in on opportunities. Malicious behaviours detected by blue teams (internal security defence teams) keeping an eye for:
- Malicious PowerShell, Cobalt Strike, Metasploit, Meterpreter or other red teaming tools were used.
- Credential theft activities such as suspicious registry modifications, domain controller file movements including NTDS.dit snapshots, and access to LSASS (Local Security Authority Subsystem Service) are some indicators for internal network compromises.
- Look out for more Indicators of Compromise (IOC), such as unusual outbound internet traffic, privileged user account activities, database read volumes, unusual DNS requests, web traffic with human behaviour, any device profile changes (mobile, security or network devices).
Implications of ransomware attacks meant decreased services in patient care and emergencies redirected to other hospitals. These consequences to patient safety and data loss threats are a big security concern. Ransomware attack mitigation is sometimes costly, including the dilemma of whether to pay the ransom or not.
Loss of such Intellectual Property, information exfiltration and loss of patient information or research data are the common cyber threats to the healthcare industry.
The following image from Microsoft shows attack tactics & techniques used by Cybercriminals against healthcare organisations.

Remote access risks
Remote access is one of the critical IT components for healthcare organisations and hospitals. Increased use of home working led to an increased usage of potentially vulnerable services such as VPN (Virtual Private Networks), increasing threat exposure often to organisations and their staff. National agencies such as CISA (Cyber Security & Infrastructure Security Agency) NCSC (National Cyber Security Centre) have issued joint advisories after observing cybercrime activity across the healthcare sector.
During the coronavirus crisis, threat actors targeting the healthcare sector exploited significant flaws such as Citrix ADC (CVE-2019-19781) and Pulse Secure VPN (CVE-2019-11510). Additionally, remote connectivity infrastructure products such as VPNs, load balancers, and firewalls were also attacked due to high-risk vulnerabilities associated with the recent versions. Similarly, the lack of mobile device management leads to relaxed restrictions in healthcare, adding to privacy risks and data breach risks. It also means risks related to using smartphones to store images or data may lead to privacy breaches, failure of patient consent, lack of patient safety and associated security implications.
Shortcuts to Security
- For so many years, it has been a commonly misunderstood phenomenon that a quick audit shall help improve an organisation’s security posture. Healthcare organisations using checklist approaches that merely are tick-box exercises provide a false sense of securing hospitals and organisations.
- Inside security-aware organisations where vulnerability management and SIEM are actively in deployment, lack of visibility into clinical networks is another challenge, often missing an essential segment of the organisation. It adds to blind faith in realising everything is running smoothly within IT security teams at hospitals.
- It is essential to understand that compliance always does not means secure. Implementing frameworks or regulation is not an incorrect way of deploying security measures; these should involve dimensional gaps covering modern threat landscapes. For example, PCI DSS certified companies got breached and compromised cardholder data.
Without exact alignment within IT security, senior management, and other stakeholders, a proactive approach to cyber security for healthcare is difficult.
Third-Party risk management
Many healthcare organisations have various types of specialised hospital computer systems such as EHR (Electronic Health Record) and EMR (Electronic Medical Record) systems, Practice Management Software used by surgeries to multi-centre hospitals and Master Patient Index (MPI) software. Manufacturers of these business-critical digital assets use different product development models, including third-party or outsourced development teams under pressure for a go-live date. Without much thought around secure coding practices, application security penetration testing or how to securely use legacy components such as vulnerable libraries adds to the risk exposure of underlying assets.
Internet of medical things or healthcare IoT
The Internet of things in the healthcare sector relates to collecting medical devices and applications linked to IT systems. These links are connectivity protocols such as sensor communications via mobile devices, Wi-Fi, Bluetooth and even external networks such as cloud connectivity for data storage and analysis. Examples include smart infusion pumps, smart insulin pens (Gocap, InPen and Esysta) and Continuous Glucose Monitor (CGM). CGMs have smart features to monitor blood glucose levels via wearable tech, mobile applications, and remote monitoring by caregivers. Similarly, connected inhalers and ingestible sensors are other examples of demonstrating how the Internet of Things is making medicine more capable.
Excellent research by ForeScout demonstrates the possibilities of exploiting weaknesses in the healthcare organisations where it was possible to dump patient test results, change the test results and vital readings, even disconnecting device access such as patient monitors.
Although cyber security and data privacy are considered barriers to cloud connectivity adoption, security issues are a valid concern for connected devices. Device manufacturers ignoring security by design principles or failing to address such issues after product releases are valid security concerns for medical device customers. The implication of these risks relates to unauthorised access by third parties and potential data breaches.

Loss of compliance
Lack of cyber security hygiene may lead to a breach of compliance and regulatory requirements. These requirements vary as per the geographic location and standard applicable to the organisations. The primary standards and frameworks known in the healthcare sector are:
- NHS Data Security and Protection Toolkit (DSPT) – An online self-assessment tool by NHS Digital that allows organisations to measure their progress against 10 data security standards. DSPT is a must for any health and care organisation that shares access to patient data, such as NHSmail, the NHS central ‘Spine’ and service providers to NHS. It is leading the change in NHS computer systems security posture, demonstrating data security commitments.
- GDPR Article 9 (GDPR superseded Data Protection Act 1998 in May 2018) relates to the rights of persons concerned by the processing of their data, including health data by health and social care organisations.
- The network and Information Systems (NIS) directive aims to establish a common baseline across the EU. It includes network security measures and incident reporting guidelines for OES (operators of essential services) in CNI (critical national infrastructure), including healthcare providers and digital service providers (DSP).
- France has approved a list of certified hosting providers (Hébergeur De Santé) that offer a certain level of protection for critical data.
- HIPAA (Health Insurance Portability and Accountability Act) provides a framework for protecting personally identifiable health data.
- ISO 27001 or PCI DSS penetration testing results not complying with standards can add to losing or failure in achieving certification for a service provider.
A few risks that commonly found in the past are now decreasing from the healthcare sector threat landscape. These include the use of unsupported operating systems, especially Windows 7 and Windows XP Extended Security Update (ESU) programs and updates around third-party supply chain applications and devices. This change had a rippled effect on the third-party supply chain forced to ensure the compatibility of their applications and devices. Although there are many challenges ahead in the sector, this positive change shows a shift in security maturity for the healthcare sector.
How to prevent cyber attacks in healthcare?
To prevent attacks among healthcare organisations, it is important to stress on solid security strategy composed of security by design principles such as the principle of least privilege, defence in depth and zero trust models. Such practices help organisations to ensure that security controls are in place after considering the attack chain and its different phases. When it comes to mitigating risks, different phases involved in a security strategy include:
- Reduce the likelihood with preventive controls
- Reduce the attack impact in case a vulnerability is exploited (such as phishing or unpatched vulnerability on external systems)
- Tactical patching in line with the risk-focused approach
- Protecting interconnected systems such as IoT
- Third-party risk management such as vendors, suppliers, partners and wider ecosystems
Good security practices – A prescription for healthcare
How to improve cybersecurity in healthcare?
Reduce the attack likelihood The following measures are both basic and effective when it comes to answering the big question above:
- Improve security measures around insecure communications and asset exposures. For instance, Health Level 7 (HL7) for transferring clinical and administrative data between various applications by healthcare organisations should not be using clear-text transport channels. Similarly, a thorough review should be conducted around using healthcare information systems protocols such as DICOM, POCT01, LIS02. Any applications with electronic health records should not be exposed to the internet without security reviews.
- Untrusted services should not be allowed to query your internal assets and vice versa. Prevent outbound and inbound permitted access on a need-to-know basis. Perform external and internal network security assessments to find gaps.
- Restricting Removable Media usage adds to limit malware delivery and infection. These restrictions help against SD card readers, USB drives and other removable media that can be used to transfer data or to launch attacks such as bootable disks.
- Segmentation at user, data and network levels would offer classification, control and safeguarding of sensitive patient data. With network segmentation, network traffic can be restricted and filtered between different network zones.
- Ensure secure remote connectivity and perimeter security by patching the exposed systems, utilising multi-factor authentication, employing the least privilege principle, and ensuring separate accounts for privileged tasks.
- Strict user management based on change and approval management processes would ensure accountability for all users. Timely account suspension, deletion or modifications demonstrate good security practices reducing the likelihood of account misuse.
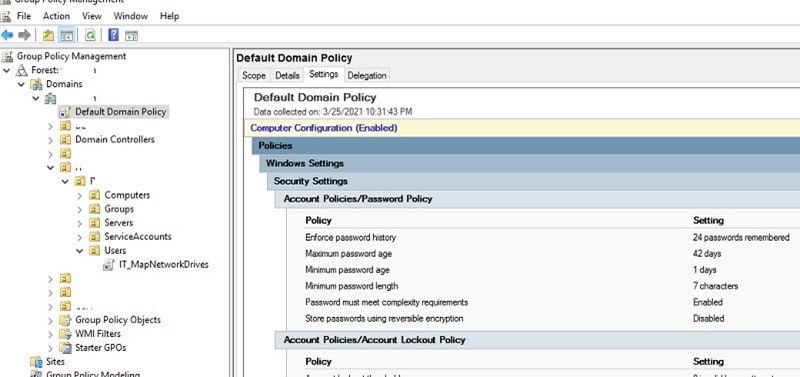
- Randomise local administrator passwords using LAPS (Local Administrator Password Solution) by Microsoft, review high privilege active directory group memberships such as Domain Admins, Enterprise Admins, Built-in Administrator groups.
All the issues mentioned above and additional checks are covered under security services such as healthcare penetration testing, vulnerability scanning and application security assessments. Sometimes in-depth penetration testing exercises are also aligned with regulatory requirements as part of compliance security assessments. As a starting point for small businesses, 10 steps to cyber security is an excellent source that covers organisation wide cyber security maturity.
Reduce the attack impact
- Isolate compromised endpoints in your network where command and control beacons or other lateral movements have taken place. These endpoints can be detected using IOCs or hunting queries through SIEM or other data flow sources. Understandably not all healthcare IT teams have this level of security expertise. Take action on the following items and prioritise investigation and remediation without changing the system state.
- Restrict access to only those functions that are critical for devices to connect to the primary environment. Removing access to services is pivotal to avoid the impact and improve detection chances.
- Network zoning to help reduce the malware infection across the entire estate. It is also the answer to why different segments are essential for easy flow control of sensitive data and infections.
- Anti-malware Capabilities in place offer early warning signs of endpoint infection. It is not a catch-all solution; this is one of the most preventative approaches in line with defence depth.
- A handy incident response plan would help with a timely response to security events. It would help limit the cyber attack damage in the event of a breach to decide on the next steps quickly than without a plan.
Tactical patch management
Often called ‘basics’ of a proactive approach towards cyber security, patching is one of the most important priorities for any IT security team. Yet we see so many organisations falling victim to remote exploits or privilege escalation issues paving the way for compromises.
Vulnerability management solutions or any patch auditing software may come up with hundreds of vulnerabilities that can be an overwhelming task. In an ideal world full of best security practices, or at the least in the articles, we often read about patching automation and patching everything! However, in practice, it isn’t always that easy. Patching should involve assessing and prioritising vulnerabilities and using defence-in-depth tactics to manage your operational risks, reduce ways to exploit attacks with secure architecture and configuration, backup your business-critical data along with logging and monitoring processes in place.
Medical devices security best practices
A medical device could be a network-connected MRI scanner, handheld monitoring and syringe drivers and other smart devices connected to the network. Since the massive increase in NHS cyber security improvement efforts (2017/2018), NHS digital have issued base guidance on protecting medical devices that include mobile devices, scanners, imaging equipment and any other devices utilising network connectivity. It applies to any network connected device. Broadly, this guidance involves the medical device security best practices irrespective of the connected device’s operating system.
- Identify all the devices across the estate that should act as inventory with device information, operating system, IP, location, etc. This network topology shall form the base for all discussions in the future.
- Create a risk mitigation plan based on reducing the likelihood of an attack and reducing the compromise in case of an attack
- Apply mitigations to reduce the attack likelihood and impact of an attack
- Understand third party connections that are utilising untrusted devices within the network or utilising trusted (organisation owned) assets within your network and perform security validation exercises
- Review your estate periodically or upon changes (new suppliers, new technology, asset changes or infrastructure upgrades) whichever sooner
- Perform independent medical device pen testing and security assessments to identify weaknesses before threat actors leverage such vulnerabilities.
Third-Party risk management
Like an internal network, there is always room for improvement, and you can never put a marker on perfection.
- It’s essential to consider overall changes to the current IT estate how new products or the introduction of services will affect the organisation. This evaluation exercise should help make informed decisions around whether you are taking on undue risk or a right partner with plans in mind.
- Introducing security and privacy risk assessments as part of the procurement process for a new information system would offer a holistic view of the situation early in the asset lifecycle process.
- Third-party security validations provide cyber security assurance against your third-party approach. As a base, standard data protection and risk assessment frameworks such as SOC compliance audits are a good start.
Conclusion
For a moment, keeping information security aside, 2020 has shown us the importance of health and health care systems in our society. With the technical advancements, we realise this importance in the digital world and add trust based on verification for healthcare providers to operate safely and securely.
Like we discussed above, it is important to understand your attack surface exposure before applying the bandage. Just deploying a few devices here and there would only exacerbate the cyber security problems in healthcare.
Know your data, Hack yourself, Train yourself, Secure your partners and vendors.
And rinse and repeat.
Improvements in the security posture have been on the rise since WannaCry, NotPetya and other global ransomware incidents; however, these incidents are not needed as a wakeup call and can be avoided. Cyber security is an ongoing improvement, and healthcare organisations should ensure a risk focussed prioritised approach to increase the cyber security maturity of their estate. A holistic approach involves people, process and technology to work in a layered manner. Aligning cyber security to act as an enabler for business growth is less costly in the long term. It starts with identifying gaps, analysing the risks and remediating those risks to provide a safe and secure environment for users. Get in touch for a non-salesy chat for your primary security concerns.
Harman Singh is a security professional with over 15 years of consulting experience in both public and private sectors.
As the Managing Consultant at Cyphere, he provides cyber security services to retailers, fintech companies, SaaS providers, housing and social care, construction and more. Harman specialises in technical risk assessments, penetration testing and security strategy.
He regularly speaks at industry events, has been a trainer at prestigious conferences such as Black Hat and shares his expertise on topics such as ‘less is more’ when it comes to cybersecurity. He is a strong advocate for ensuring cyber security as an enabler for business growth.
In addition to his consultancy work, Harman is an active blogger and author who has written articles for Infosecurity Magazine, VentureBeat and other websites.